In cybersecurity, the identification of vulnerabilities is only the first step toward securing an organization. Efficient prioritization of remediation efforts is essential to focus resources on the most critical risks and maximize security impact.
Prioritizing remediation involves evaluating vulnerabilities based on severity, exploitability, business impact, and ease of mitigation. Security hardening complements remediation by implementing measures to reduce attack surfaces and strengthen defenses.
Together, they form the backbone of a proactive security posture that reduces exposure, prevents breaches, and aligns security efforts with organizational objectives.
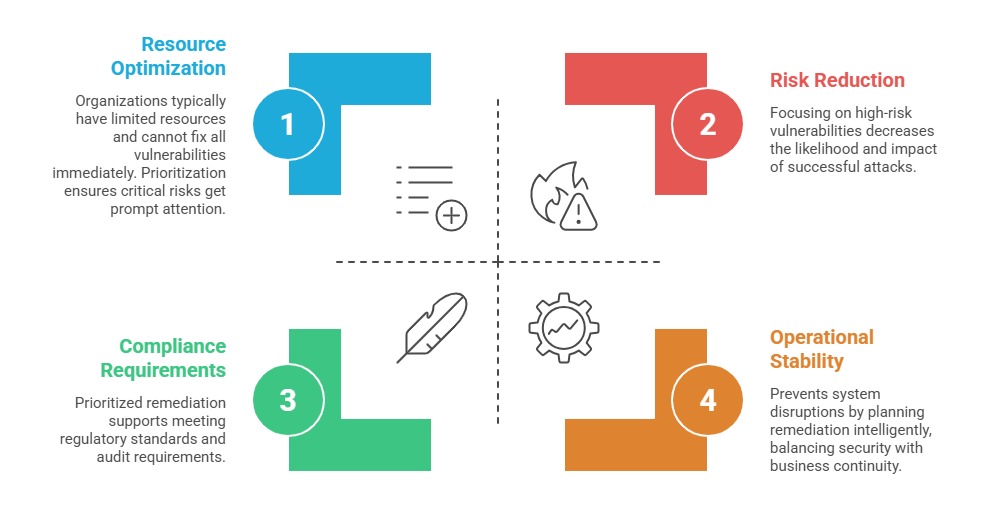
Importance of Prioritizing Remediation
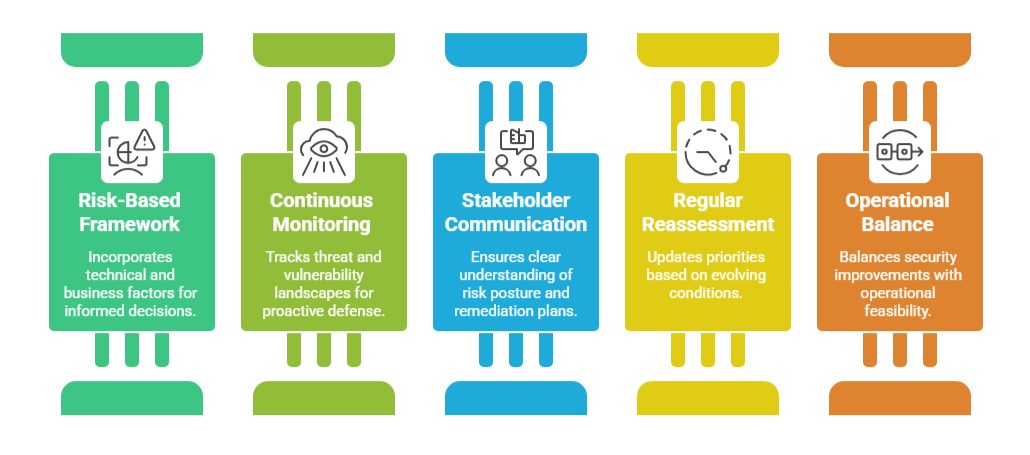
Remediation prioritization ensures that limited resources are directed toward the highest-impact vulnerabilities. The following points highlight its role in reducing risk, meeting regulatory standards, and maintaining operational stability.
Criteria for Prioritization
Effective prioritization requires a balanced assessment of technical risk, business consequences, system exposure, and remediation feasibility. The points below outline the essential factors used to rank vulnerabilities.
1. Vulnerability Severity and Exploitability: Using standardized scoring systems like CVSS to determine technical impact. Additionally, factors such as exploit availability, ease of attack, and potential for automated exploitation are considered to evaluate the overall risk posed by the vulnerability.
2. Business Impact: Assessing the importance of affected assets, including data sensitivity, operational role, and potential effects on customers. Financial, legal, and reputational consequences are also considered to understand the broader implications of the vulnerability.
3. Exposure and Accessibility: Prioritizing vulnerabilities on internet-facing systems or critical internal infrastructure. It is also important to evaluate whether compensating controls are in place to mitigate potential risks.
4. Remediation Effort and Time: Evaluated by considering factors such as complexity, required downtime, and dependencies. Quick wins—easy fixes with high impact—may be prioritized higher to achieve immediate risk reduction.
Remediation Approaches
Listed below are the main methods for remediating security issues. Each approach focuses on patching, configuration adjustments, mitigation strategies, and automation to reduce risk.
1. Patching and Updates
Apply vendor-supplied patches and hotfixes promptly.
Prioritize patches addressing critical and actively exploited vulnerabilities.
2. Configuration Changes
Harden system and network configurations (disable unused services, restrict permissions).
Implement policies like secure baselines and CIS benchmarks.
3. Mitigation When Immediate Remediation Isn't Possible:
Use compensating controls such as network segmentation, EDR tools, or access restrictions.
Monitor vulnerable assets closely for signs of abuse.
4. Automation: Employ patch management and vulnerability scanning automation to reduce human effort and accelerate remediation cycles.
Security Hardening Guidance
To build a robust security posture, organizations must harden systems, networks, and applications while maintaining continuous monitoring. The points below summarize the main strategies for effective protection.
1. System Hardening: Strengthening the security of systems by disabling unnecessary services and ports, enforcing strong authentication and authorization policies, and implementing encryption to protect data both at rest and in transit
2. Network Security: Protecting the infrastructure by applying firewall rules and intrusion detection or prevention systems, along with implementing network segmentation and adopting zero-trust principles to limit unauthorized access.
3. Application Security: Ensures software safety by following secure coding practices and performing regular code reviews and penetration testing to identify and fix vulnerabilities.
4. Continuous Monitoring: Enhances security by integrating security information and event management (SIEM) for real-time alerts and leveraging threat intelligence to dynamically adjust priorities.