Application Programming Interfaces (APIs) are essential for modern software systems, enabling communication between different software components and services.
As APIs increasingly expose critical functionalities and sensitive data, their security becomes paramount.
Advanced API security testing focuses on thoroughly evaluating authentication, authorization, input validation, and abuse protection mechanisms.
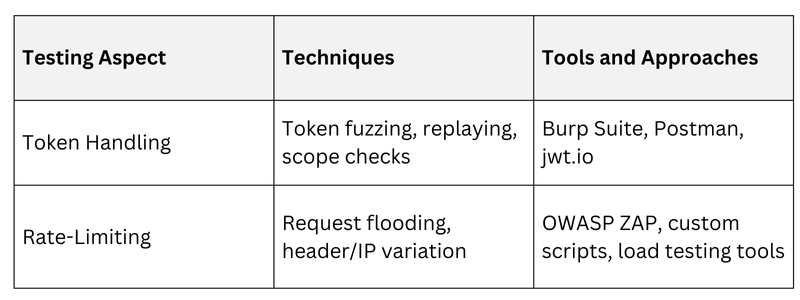
Two critical aspects of API security testing are token handling and rate-limiting bypass, as improper implementations in these areas can lead to unauthorized access, data leakage, and denial of service.
Token Handling in API Security
Tokens such as OAuth tokens, JSON Web Tokens (JWT), and API keys authenticate and authorize clients accessing APIs. Proper token management is essential for securing API endpoints.
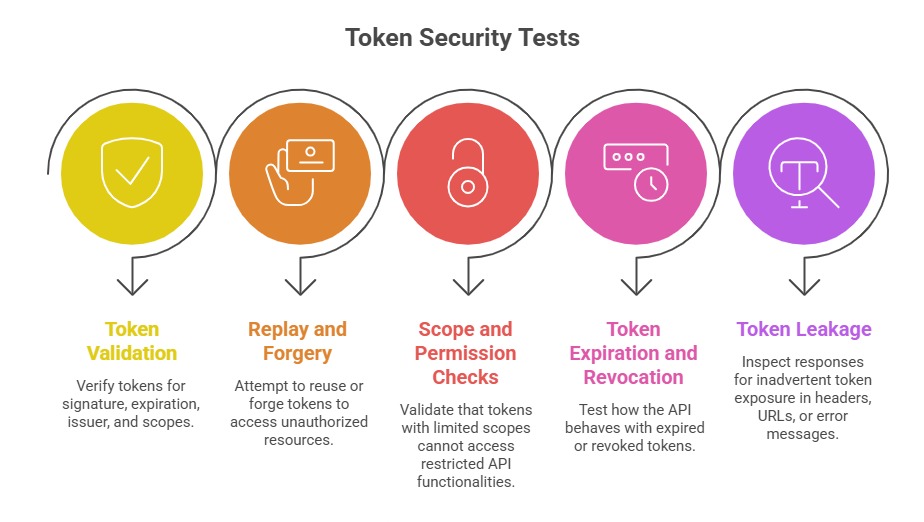 Common Token Handling Vulnerabilities: Arise from weak or improperly implemented signature verification, including the use of insecure algorithms. Tokens that carry excessive permissions or have overly long expiration periods increase the risk of misuse if compromised.
Common Token Handling Vulnerabilities: Arise from weak or improperly implemented signature verification, including the use of insecure algorithms. Tokens that carry excessive permissions or have overly long expiration periods increase the risk of misuse if compromised.
Additionally, failing to validate critical fields such as issuer and audience can allow attackers to use forged or replayed tokens. Storing sensitive information in JWT payloads without proper encryption further exposes data, making the system vulnerable to unauthorized access or leakage.
Rate-Limiting and Abuse Prevention Testing
Rate limiting controls the number of requests a client or user can make within a specific time to prevent abuse, brute-force attacks, and denial of service.
Testing Rate-Limiting Controls:
1. Request Flooding: Send bursts of requests to detect thresholds and enforcement gaps.
2. Bypass Techniques: Attempt to evade limits by varying IPs, tokens, or user-agents.
3. Distributed Requests: Use multiple sources to simulate distributed attacks to overwhelm API endpoints.
4. Parameter Manipulation: Modify request parameters to bypass client or API-level limits.
Common Weaknesses: Inconsistent enforcement across different API endpoints, creating opportunities for attackers to exploit gaps. When systems fail to distinguish between users or IP addresses, rate limits can be easily bypassed.
Additionally, misconfigured thresholds—either too high to be effective or too low to allow normal usage—reduce the reliability of throttling mechanisms.
The absence of comprehensive logging and alerting further weakens detection, making it difficult to identify or respond to abuse patterns in real time.
Test Methodologies and Tools
Mitigation Best Practices
1. Enforce strong token validation including signature, issuer, expiration, and scope.
2. Use short-lived access tokens with refresh tokens for long sessions.
3. Encrypt sensitive JWT claims and avoid exposing tokens in responses.
4. Implement consistent and granular rate-limiting policies considering IP, user, and token.
5. Monitor API usage patterns and trigger alerts on anomalies.
Class Sessions
Sales Campaign

We have a sales campaign on our promoted courses and products. You can purchase 1 products at a discounted price up to 15% discount.
