In the rapidly evolving landscape of cybersecurity, understanding adversary behaviors and crafting effective defenses requires more than just reactive measures.
Threat intelligence integration combined with tactics, techniques, and procedures (TTP) mapping empowers organizations to proactively identify, analyze, and mitigate threats by linking real-world attack behaviors to known adversary strategies.
This process involves gathering, analyzing, and operationalizing threat data, then aligning it with attack methods to anticipate future actions and bolster security postures.
Proper threat intelligence and TTP mapping are critical components in modern cybersecurity, enabling informed decision-making and strategic defense planning.
Threat Intelligence
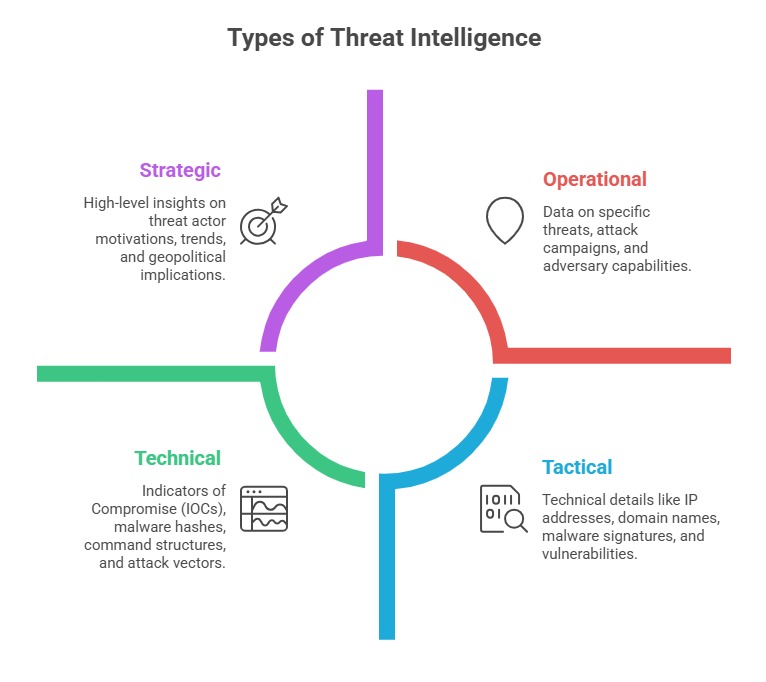
Threat intelligence, often called cyber threat intelligence (CTI), refers to the collection, analysis, and dissemination of information about potential or active cyber threats.
Sources of Threat Intelligence:
1. Open-source intelligence (OSINT)
2. Commercial threat intelligence feeds
3. Internal security logs and incident reports
4. Industry-sharing platforms (ISACs, MISP, ThreatConnect)
TTP Mapping: Understanding Attack Patterns
TTP stands for Tactics, Techniques, and Procedures, used by threat actors to delineate how adversaries operate.
Tactics: The high-level goals or overarching objectives behind an attack (e.g., data exfiltration, credential theft).
Techniques: The specific methods used to achieve tactics (e.g., phishing, lateral movement).
Procedures: The detailed, step-by-step actions threat actors take (e.g., leveraging a specific malware or exploiting a particular vulnerability).
Why TTP Mapping Matters:
TTP mapping is important because it helps connect observed attacker behaviors to known threat groups, enabling more accurate attribution. It also strengthens detection capabilities by highlighting recurring patterns that may indicate malicious activity.
Additionally, understanding these techniques, tactics, and procedures enhances response efforts by revealing how attackers operate, which in turn supports more effective threat hunting, incident response, and mitigation planning.
Integrating Threat Intelligence with TTP Mapping
Integrating TI with TTP mapping aligns indicators, behaviors, and adversary patterns into a unified analytical model, helping analysts pinpoint threats with greater accuracy.
Steps for Effective Integration:
1. Data Collection: Gather threat intelligence from multiple sources, including logs, alerts, and feeds.
2. Data Enrichment: Correlate raw data with known IOCs and boost insights using contextual information.
3. Mapping & Analysis: Match observed behaviors, IOCs, and artifacts with established TTP frameworks, such as ATT&CK or Kill Chain models.
4. Visualization: Use dashboards, graphs, or heatmaps to depict threat behaviors relative to the organization’s environment.
5. Operationalization: Automate detection rules, alert triggers, and response workflows based on TTP patterns.

Benefits of Threat Intelligence & TTP Mapping
Listed below are the primary advantages that threat intelligence and TTP mapping provide in enhancing cyber defense capabilities.
1. Proactive Defense: Identifies attack patterns before they impact systems.
2. Attribution & Hunting: Enhances attribution accuracy and supports targeted threat hunting.
3. Incident Response: Accelerates detection and containment by understanding attacker workflows.
4. Strategic Planning: Guides security investments and policy updates based on evolving threats.
Challenges & Best Practices
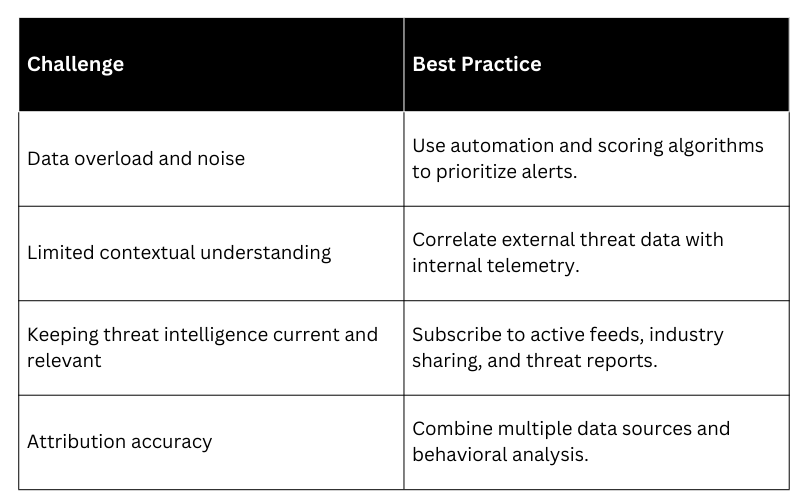
For effective TTP mapping include regularly updating threat intelligence sources and TTP models to stay aligned with evolving attacker behaviors. Automating IOC correlation, detection, and response workflows helps improve efficiency and accuracy.
Using a structured framework like MITRE ATT&CK ensures consistency in mapping and analysis. Moreover, fostering a culture of threat intelligence sharing within industry groups strengthens collective defense and enhances overall security posture.
