In cybersecurity, an attack surface refers to the sum of all potential entry points or vulnerabilities through which an attacker can gain unauthorized access to a system, network, or infrastructure.
Identifying attack surface expansion paths involves understanding how new vulnerabilities or access points emerge as an organization grows or changes, thereby increasing the potential vectors for exploitation.
Understanding Attack Surface Expansion
Attack surface expansion is the increase in the number and complexity of exploitable points within an IT environment.
Factors driving this expansion can be strategic business decisions or technological changes, such as onboarding new partners, deploying new applications, or integrating with cloud platforms.
While such growth is necessary for innovation and scalability, it introduces new vulnerabilities if not carefully managed.
Key Factors Contributing to Attack Surface Expansion
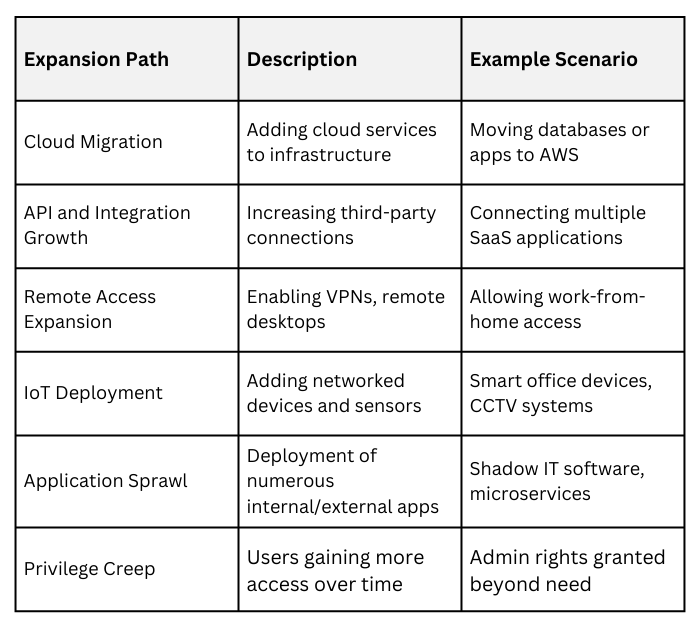
Multiple organizational and technological trends can widen security exposure. Below are the factors most responsible for attack surface growth.
1. Digital Transformation: Adopting cloud infrastructure and SaaS platforms introduces new cloud endpoints and roles that require security controls.
2. Third-Party Integrations: Partner networks and APIs increase trust boundaries, potentially introducing insecure interfaces.
3. Remote Workforces: Allowing remote access expands the network perimeter to external, sometimes less secure, environments.
4. IoT and Mobile Devices: Proliferation of connected devices increases physical and network access points.
5. Application Proliferation: Multiple internal and external software applications may have varying security postures.
6. Shadow IT: Unmanaged or unauthorized technology use within organizations often increases unseen vulnerabilities.
Identifying Expansion Paths
To identify these paths, organizations must systematically map their entire IT ecosystem, including cloud services, on-premises infrastructure, mobile endpoints, and third-party connections.
Steps in Identifying Attack Surface Expansion Paths
To maintain robust security, organizations need to uncover where their attack surface could increase. The following steps guide this process.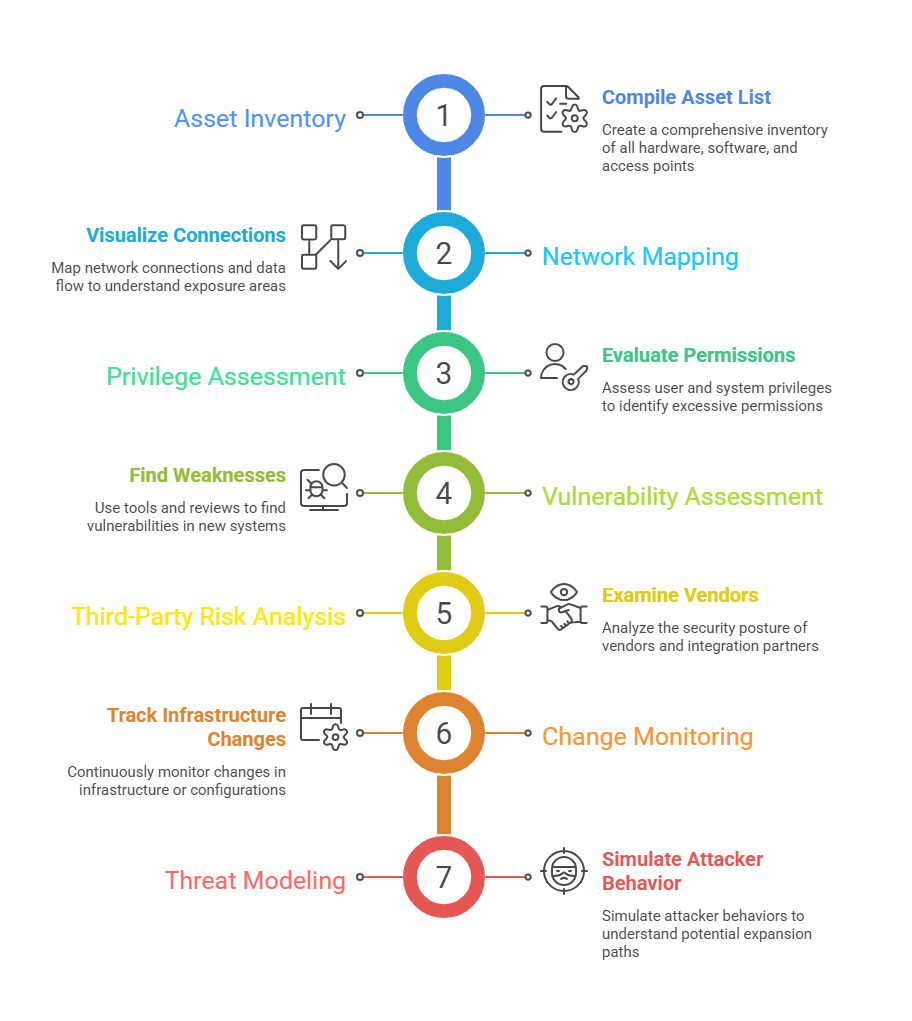 Visualization and Analysis
Visualization and Analysis
Visualization tools help clarify complex attack surface expansion by representing assets, connections, and trust boundaries as graphs or topological maps.
These visualizations highlight critical nodes, potential attack vectors, and layered defense weak points. Combining these models with threat intelligence enables prioritization of security controls based on risk exposure.
Common Attack Surface Expansion Paths
Mitigating Risks Associated with Expansion
As organizations scale, maintaining security becomes more complex. The following approaches help reduce vulnerabilities tied to expansion.
1. Continuous Visibility: Implement tools for real-time asset discovery and network monitoring to maintain up-to-date knowledge of the attack surface.
2. Access Control: Apply least privilege principles and segment networks to limit lateral movement opportunities.
3. Security Policy Enforcement: Automate security configuration management across environments.
4. Regular Audits: Conduct periodic reviews and penetration tests targeting newly added assets and integrations.
5. Zero Trust Architecture: Adopt zero trust to assume no implicit trust and continuously verify access every step.
6. Incident Response Readiness: Prepare to quickly identify and contain breaches originating from expanded surfaces.
