Attack path mapping is a critical practice in cybersecurity that involves visually or logically outlining the sequence of steps an adversary takes within a network or system to achieve their objectives, such as data exfiltration, privilege escalation, or persistence.
Aligning attack path mapping with the MITRE ATT&CK framework enhances its value by providing a standardized taxonomy of adversary tactics, techniques, and procedures (TTPs).
This alignment enables organizations to better understand attack behaviors, evaluate defensive coverage, and prioritize remediation efforts.
Mapping attack paths using MITRE ATT&CK is a powerful approach for threat hunting, incident response, and proactive security management.
Understanding Attack Path Mapping
Attack path mapping visually represents the chain of events or attack vectors from initial compromise through lateral movement to an adversary’s end goal. It helps security teams to:
1. Identify weak points in defenses across the attack lifecycle.
2. Assess “kill chains” to interrupt attacker progress.
3. Recommend targeted controls and detection strategies.
4. Facilitate communication and reporting to stakeholders with concrete, contextualized scenarios.
The MITRE ATT&CK Framework
MITRE ATT&CK is a globally recognized knowledge base of adversary tactics and techniques organized into matrices by platforms such as Windows, Linux, macOS, and Enterprise environments.
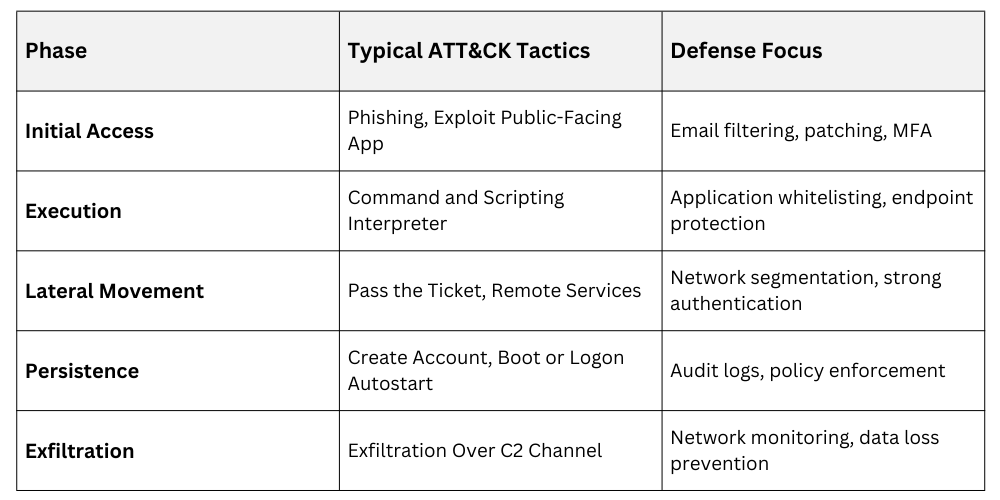
1. Tactics: Represent adversary objectives like Initial Access, Execution, Persistence, Privilege Escalation, Defense Evasion, Credential Access, Discovery, Lateral Movement, Collection, Exfiltration, and Impact.
2. Techniques: Specific methods adversaries use to achieve tactics (e.g., spearphishing, DLL injection, pass-the-hash).
3. Sub-techniques: More granular descriptions refining techniques.
The framework encourages a structured understanding and categorization of attacker behaviors.
Aligning Attack Path Mapping with MITRE ATT&CK
Mapping to MITRE ATT&CK standardizes attack description, improves threat intelligence use, and guides detection and mitigation strategies.
Steps for Alignment:
1. Data Collection: Gather event logs, forensic evidence, or observed attack patterns.
2. Identify Adversary Behaviors: Match observed actions with MITRE ATT&CK tactics and techniques.
3. Construct Attack Paths: Sequence techniques in the order adversaries likely used them, highlighting branching paths where multiple attack options exist.
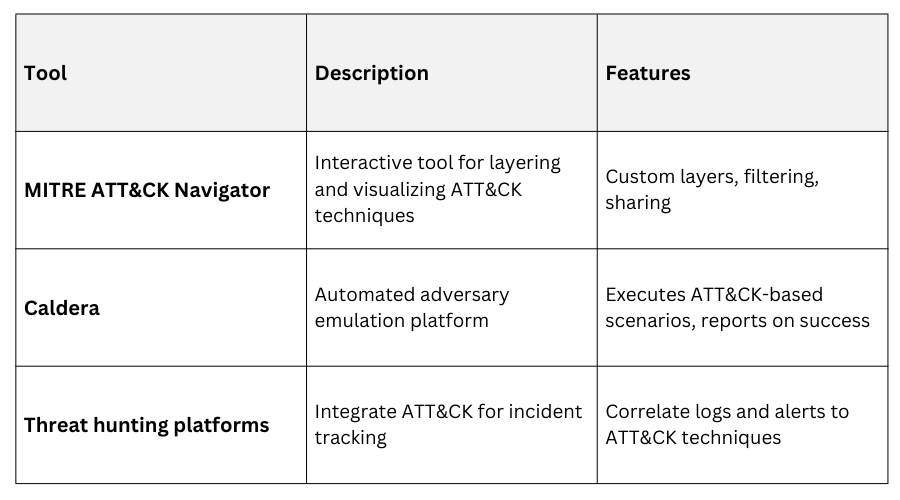
4. Analysis and Visualization: Use visual tools (e.g., ATT&CK Navigator, threat modeling diagrams) to present mapped paths.
5. Gap Analysis: Determine which techniques lack detection or mitigation coverage.
Tools for Attack Path Mapping
Practical Use Cases of Attack Path Mapping
Below are the essential scenarios where security teams benefit the most from implementing attack path mapping.
1. Incident Response: Reconstruct attacker actions during breaches to guide remediation.
2. Red Teaming & Penetration Testing: Validate attack paths against real assets and simulate adversary movements.
3. Security Architecture Review: Identify defense gaps and strengthen controls around weak links.
4. Threat Hunting: Guide proactive searches for indicators and behaviors mapped to known attack patterns.
ATT&CK-Aligned Attack Path Phases