In cybersecurity and IT operations, the efficient handling of large volumes of data is crucial for effective decision-making, incident response, and compliance.
Data parsing, reporting, and workflow automation streamline the transformation of raw outputs from tools and systems into structured, actionable information.
Parsing converts unstructured or semi-structured data into usable formats, while reporting communicates insights clearly to stakeholders.
Workflow automation ties together these processes, integrating multiple tools and tasks into seamless operations that reduce manual effort and human error.
Data Parsing: Extracting Meaningful Information
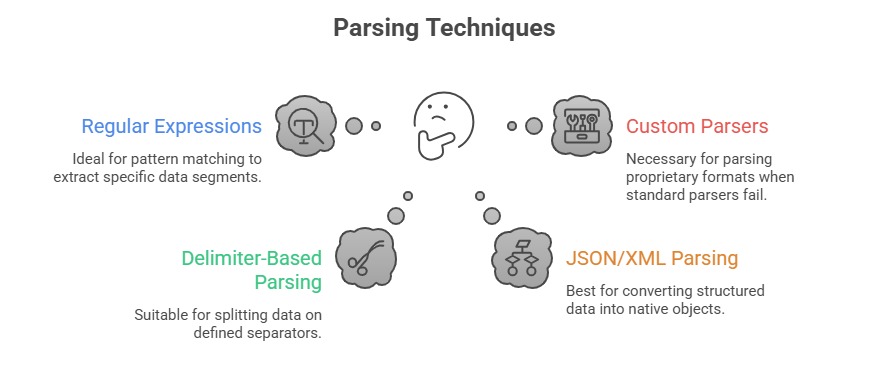
Data parsing involves breaking down data streams or logs into structured components that enable further analysis.
Types of Data Parsed:
1. Logs from security devices (firewalls, IDS/IPS, endpoint protections).
2. Scan and vulnerability assessment outputs.
3. Network traffic captures and packet data.
4. API responses and raw application data.
Tools & Libraries:
1. Python (re, json, xml.etree.ElementTree)
2. Bash (awk, sed, cut)
3. PowerShell (ConvertFrom-Json, Select-String)
4. Log parsing frameworks such as Logstash and Fluentd
Reporting: Summarizing and Presenting Insights
Reporting aggregates parsed data to generate clear, insightful outputs suitable for various audiences—from technical analysts to management.
Report Formats:
1. Tabular CSV or Excel sheets for detailed review.
2. Dashboards using BI tools (PowerBI, Grafana).
3. HTML or PDF documents with charts and summaries.
4. Alerts or notifications for critical findings.
Effective Reporting Elements:
1. Clarity: Clean layouts and understandable language.
2. Relevance: Focus on actionable and high-priority data.
3. Contextualization: Add metadata like timestamps, source information, and trend insights.
4. Automation: Regular, scheduled report generation without manual input.
Common Reporting Tools:
1. Scripting languages generating CSV/Excel (Pandas in Python).
2. Report generation libraries (ReportLab for PDFs, Jinja2 with HTML).
3. Cloud-native services (AWS QuickSight, Azure Monitor).
4. Specialized security platforms with built-in reporting.
Workflow Automation: Integrating and Orchestrating Processes
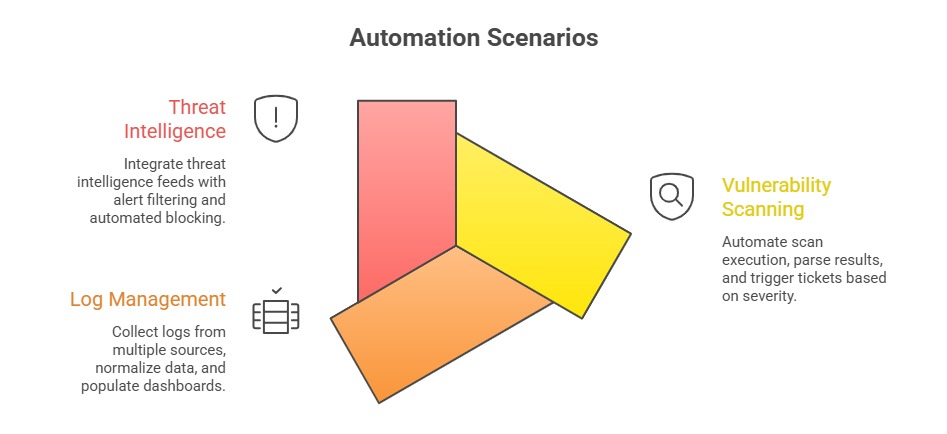
Workflow automation connects parsing, scanning, reporting, and alerting components to establish unified processes that operate with minimal human intervention.
Benefits: Increased operational speed and consistency, enabling tasks to be executed quickly and uniformly. It also reduces human errors and fatigue while improving reproducibility and scalability across processes.
As a result, organizations achieve faster incident detection and response, strengthening their overall security posture.
Automation Tools:
1. Orchestration platforms (Ansible, SaltStack).
2. Workflow engines (Apache Airflow, Jenkins pipelines).
3. Scripting languages with libraries for API integration (Python Requests, PowerShell Web Cmdlets).
4. Cloud-native automation (AWS Lambda, Azure Logic Apps).
