Server-side attacks target vulnerabilities in the backend infrastructure of web applications and services, aiming to manipulate or exploit the server’s behavior to gain unauthorized access, extract sensitive data, or execute arbitrary code.
Among these, advanced SQL Injection (SQLi), template injection, and server-side template injection (SSTI) are particularly dangerous due to their potential impact and difficulty to detect.
These attacks exploit flaws in how servers process data, templates, or queries, leading to security breaches, data leakage, or server compromise.
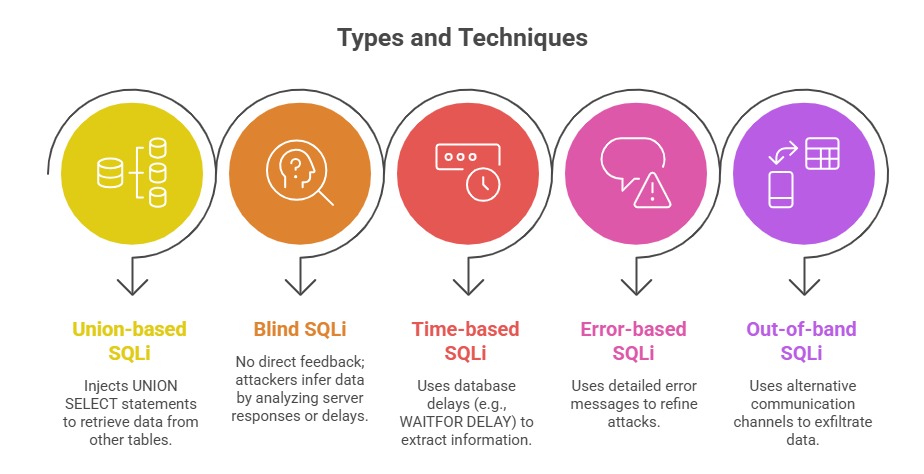
Advanced SQL Injection (SQLi)
SQL Injection occurs when an attacker supplies malicious input that is improperly sanitized, allowing manipulation of database queries.
Advanced SQLi extends beyond straightforward injection; it includes blind SQLi, time-based attacks, stacked queries, and out-of-band techniques.
Impacts: Data theft or corruption when attackers manipulate or extract sensitive information. They may also bypass authentication controls to gain unauthorized access.
In more advanced cases, attackers can achieve remote code execution (RCE) through database functionalities. Additionally, SQL injection flaws can be abused to cause Denial of Service (DoS), disrupting application and database availability.
Detection & Prevention: It is essential to use parameterized queries or prepared statements, which separate code from user input and prevent malicious injections.
Employing thorough input validation and sanitization further reduces the risk by ensuring only expected data is processed.
Regularly updating and patching database software addresses known vulnerabilities, while implementing Web Application Firewalls (WAF) helps block suspicious queries in real time.
Additionally, conducting periodic security testing and code reviews ensures that vulnerabilities are identified and mitigated before they can be exploited.
Template Injection
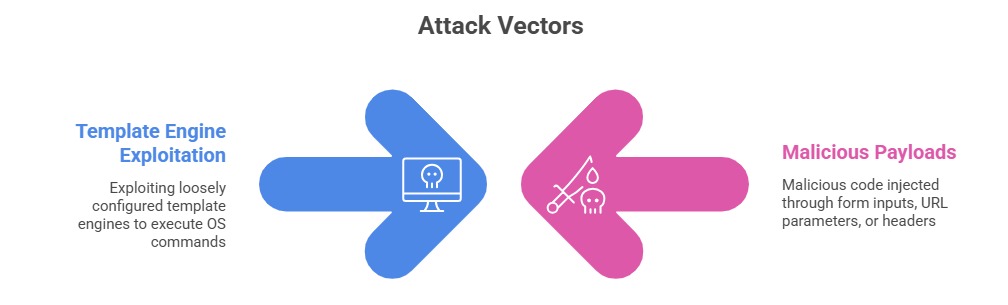
Template injection happens when user inputs are embedded directly into templates rendered on the server without proper sanitization, enabling attackers to manipulate or re-define template logic.
-Picsart-CropImage.png)
How Template Injection Works: Attackers inject template syntax that gets executed by the server’s template engine, leading to data exposure, code execution, or denial of service.
Common Engines Vulnerable to SSTI: Jinja2 (Python), Twig (PHP), FreeMarker (Java), Velocity (Java).
Examples of Attacks:
1. Command execution by injecting system calls in template syntax.
2. Data theft from server-side environment variables.
Detection & Prevention: It is important to avoid rendering user input directly within templates, which can allow attackers to execute arbitrary code.
Using sandboxed or restricted template engines adds an additional layer of security by limiting the capabilities of template execution.
Employing strict input validation and escaping ensures that only safe data is processed within templates. Additionally, monitoring templates and reviewing logs for suspicious syntax patterns helps identify potential attacks early and allows for timely remediation.
Server-Side Template Injection (SSTI)
SSTI is a subset of template injection where the server-side rendering engine executes injected template code, potentially leading to arbitrary code execution.
Consequences: Insecure deserialization can be severe, often leading to full system compromise when attackers inject malicious objects that execute arbitrary code.
This vulnerability can also enable data exfiltration, allowing sensitive information to be stolen without detection.
In more advanced scenarios, attackers may use insecure deserialization as a foothold to pivot deeper into internal systems, expanding their access and escalating the overall impact of the breach.
Mitigation Techniques: Disabling or restricting any template features that could permit arbitrary code execution, thereby limiting the attack surface.
It is equally important to sanitize all inputs and rely on safe, vetted template functions to prevent malicious payloads from being processed.
Additionally, deploying runtime application self-protection (RASP) and intrusion detection solutions helps identify and block suspicious template behavior in real time, strengthening overall application security.
