In the realm of cybersecurity and ethical hacking, advanced network mapping and host discovery are crucial activities that help security professionals understand the structure of a target network.
These techniques enable auditors and penetration testers to identify active devices, their roles, and how they connect within the network. Properly mapping the network assists in pinpointing exposure points, resource allocation, and potential vulnerabilities.
This process often involves detailed analysis and reconnaissance methods that go beyond simple ping sweeps or basic scans, aiming to uncover hidden or obscure hosts that might otherwise remain unnoticed in traditional assessments.
Understanding Network Mapping and Host Discovery
Network mapping involves creating a visual or logical representation of a network's topology, showing devices, connections, and data flow patterns.
Host discovery, meanwhile, focuses on identifying live hosts that are active and reachable within that mapped environment. These activities form the foundation for deeper vulnerability analysis and security auditing.
Key Techniques in Advanced Network Mapping
The following techniques form the foundation of advanced network discovery and topology analysis. They enable security teams to uncover devices, services, and communication routes with accuracy.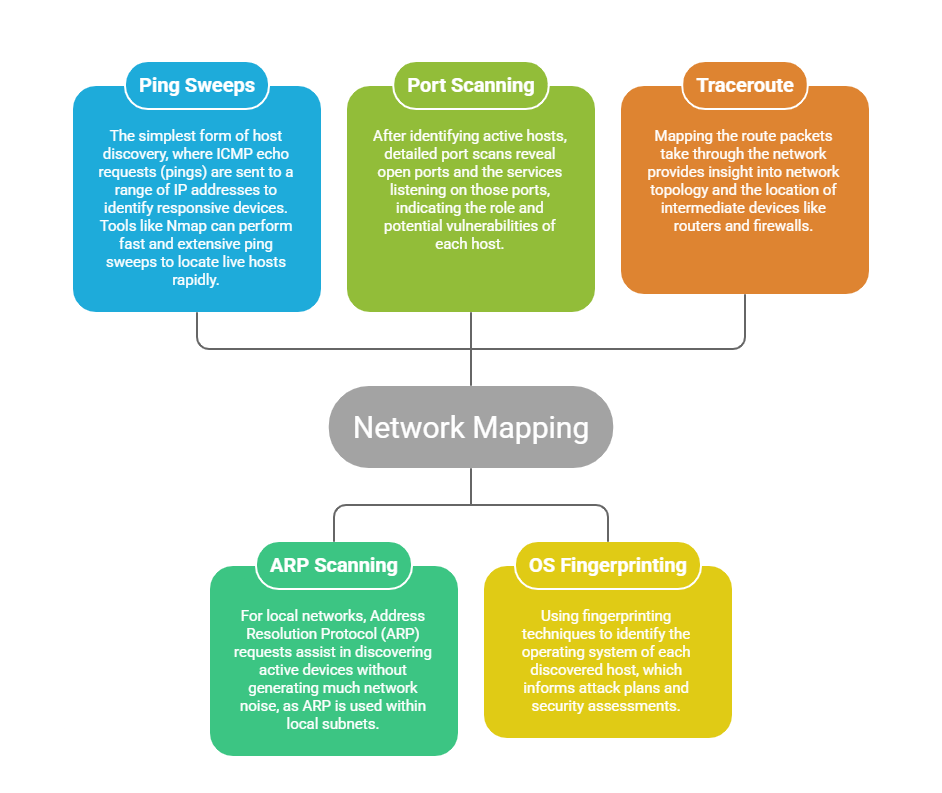
Host Discovery Techniques
Here is a list of common techniques used to find and analyze hosts on a network. They support both active probing and passive observation for complete discovery.
1. Active Scanning: Sending specific packets (TCP SYN, ACK, or connection attempts) to discover and identify hosts and services actively.
2. Passive Monitoring: Analyzing network traffic without directly interacting with hosts, which is less detectable but may not offer as comprehensive information.
3. Service Version Detection: Techniques that involve probing open ports to determine the exact versions of services and applications, helping identify specific vulnerabilities.
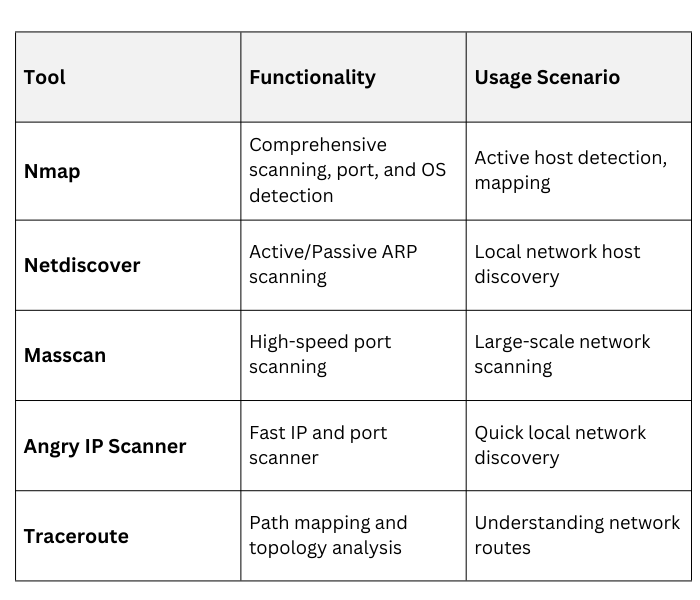
Tools for Advanced Network Mapping & Host Discovery
Best Practices
Outlined below are key practices designed to enhance the quality and safety of network mapping. They promote smarter scanning, better accuracy, and proper adherence to permissions.
1. Limit Scan Speed: To avoid detection or network disruption, adjust scan timing and rate.
2. Use Multiple Techniques: Combining active and passive methods increases accuracy and stealth.
3. Automate and Schedule: Regular network scanning ensures updated maps for ongoing security management.
4. Respect Privacy and Permissions: Only conduct network mapping with explicit authorization.
Practical Applications
In vulnerability assessments, it helps security teams identify unpatched, outdated, or misconfigured hosts that could introduce weaknesses into the environment.
During penetration testing, recognizing the roles and behaviors of different devices enables testers to map potential attack vectors and understand how an attacker might exploit them.
For network management, maintaining an accurate and updated inventory of all active devices ensures smooth operations, better visibility, and efficient troubleshooting.
In incident response, rapid device identification is crucial for pinpointing affected systems, containing threats, and restoring normal operations as quickly as possible.
