Credential dumping and token/key abuse represent critical attacks within cybersecurity that enable adversaries to harvest authentication data and misuse access tokens or cryptographic keys to escalate privileges, move laterally, and maintain persistence within compromised environments.
It refers to extracting stored credentials such as hashed passwords, plaintext credentials, or secrets from operating systems or applications.
Token and key abuse involve exploiting access tokens or cryptographic keys issued during authentication to impersonate users or services without needing to know their passwords.
Credential Dumping: Extracting Sensitive Authentication Data
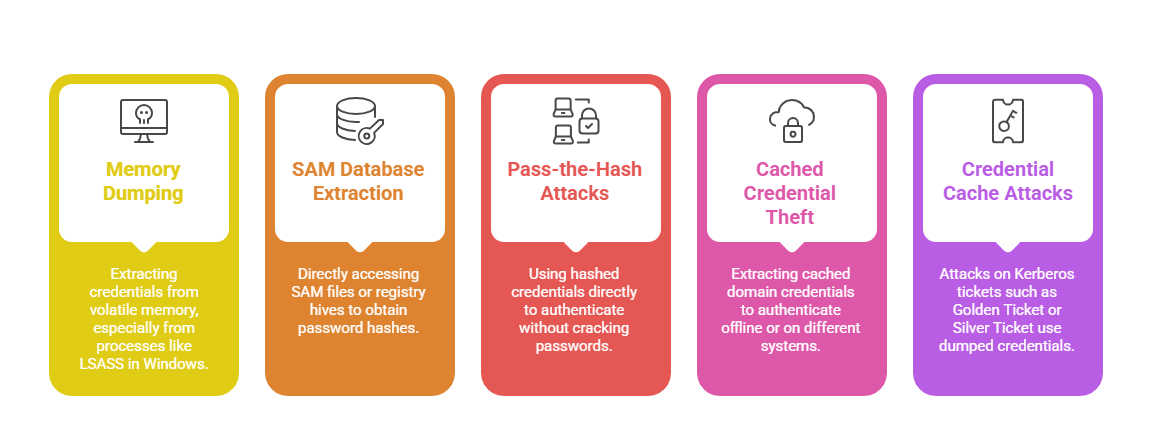
Credential dumping encompasses techniques used to retrieve credentials stored on a system. These credentials can be leveraged to gain unauthorized access to other systems or services, thereby facilitating lateral movement and privilege escalation.
Common Targets for Credential Dumping
1. Windows Security Accounts Manager (SAM) database
2. Local Security Authority Subsystem Service (LSASS) memory
3. Cached domain credentials and password hashes
4. Kerberos tickets and tokens stored in memory
5. Linux /etc/shadow and other authentication-related files
Techniques and Tools
Token and Key Abuse: Leveraging Authentication Artifacts
After successful authentication, systems often issue tokens or keys (e.g., Kerberos tickets, OAuth tokens, API keys) to maintain session continuity.
Attackers who steal these tokens or keys can impersonate users or services to interact with systems with their permissions, bypassing direct credential usage.
Types of Tokens and Keys:
1. Kerberos Tickets: Tickets that authenticate users and services in Active Directory environments.
2. OAuth Tokens: Used for delegated access in cloud services and APIs.
3. JWT (JSON Web Tokens): Used in modern web applications for stateless authentication.
4. API Keys and Secrets: Access credentials for automated and application integrations.
Abuse Techniques:
1. Pass-the-Ticket (PtT): Using stolen Kerberos tickets to gain access to resources as the legitimate user or admin.
2. Token Replay or Theft: Capturing valid tokens from memory or network traffic and reusing them.
3. Token Forgery: Creating or modifying tokens to escalate privileges or extend access.
4. Key Extraction & Use: Extracting keys from insecure storage or memory to gain unauthorized service or API access.
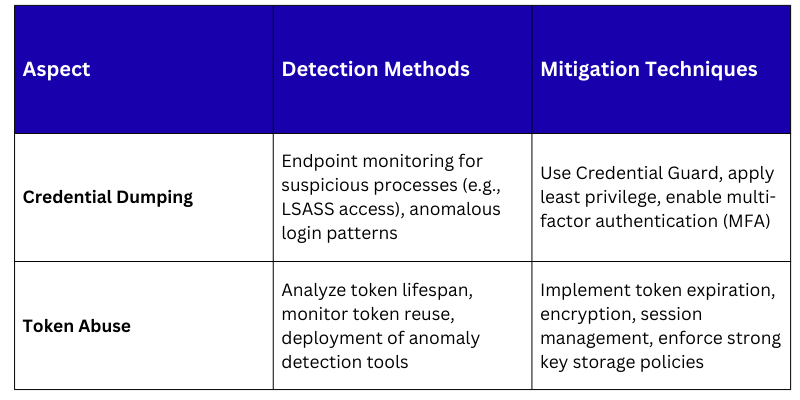
Detection and Mitigation Strategies
Best Practices
1. Employ endpoint security solutions capable of detecting credential dumping activities.
2. Restrict access to critical system processes like LSASS and monitor abnormal access attempts.
3. Implement token binding and short token lifetimes to reduce replay risks.
4. Force re-authentication and token revocation in case of artifacts compromise.
5. Educate users and administrators about phishing and social engineering mitigation.
