In cybersecurity, sandboxing is a widely used defense technique where potentially malicious software is executed in a controlled, isolated environment to observe its behavior without risking harm to production systems.
However, sophisticated malware authors and attackers design their code to detect these sandboxes and evade analysis.
Role of Sandboxes in Malware Detection
Sandboxes enable dynamic analysis of unknown files by simulating operating system environments and monitoring runtime behavior such as file system activity, network communication, and system calls.
Detection depends on observing malicious behavior that wouldn't be visible in static analysis. Effective sandboxes employ hooks, instrumentation, and behavior logging to identify threats in near real-time.
Conceptual Sandbox Evasion Techniques
Malware creators embed logic to identify when their code runs within a sandbox to avoid execution or alter behavior, thereby bypassing detection.
1. Environment Artifacts Detection
Malware checks for artifacts typical of sandbox environments, such as:
Presence of virtualization drivers or software (VMware, VirtualBox logs).
Unusual process or service names running inside the sandbox.
Files, registry keys, or paths unique to sandboxes.
Specific MAC or IP address ranges associated with cloud sandbox providers.
2. Timing-based Techniques
Malware employs delays, sleeps, or loops to outlast the sandbox’s analysis time limit, as many sandboxes only run samples for brief periods. Variations include:
Long sleep intervals.
Measuring discrepancies in timer or CPU cycle counts to detect throttling.
Waiting for user activity or specific system event triggers not easily mimicked by automated sandboxes.
3. User Interaction Requirements: Malicious code may require user inputs or interactions such as mouse movement, keyboard input, or clicking buttons to proceed with payload execution, which sandboxes typically cannot simulate effectively.
4. Network Evasion and Conditional Payloads
Suppressing malicious network communication when run in sandbox networks or IP ranges.
Verifying reachability of command and control (C&C) servers before activation.
Using domain fluxing or fast-flux techniques to avoid sandbox domain reputation checks.
5. Hardware Fingerprinting: Malware inspects hardware characteristics including CPU details, available RAM, graphics card info, and peripherals to differentiate real machines from virtualized or sandboxed hosts.
6. API and System Call Generation Checks: Detecting inconsistencies or limited API implementations typical of simulation environments.
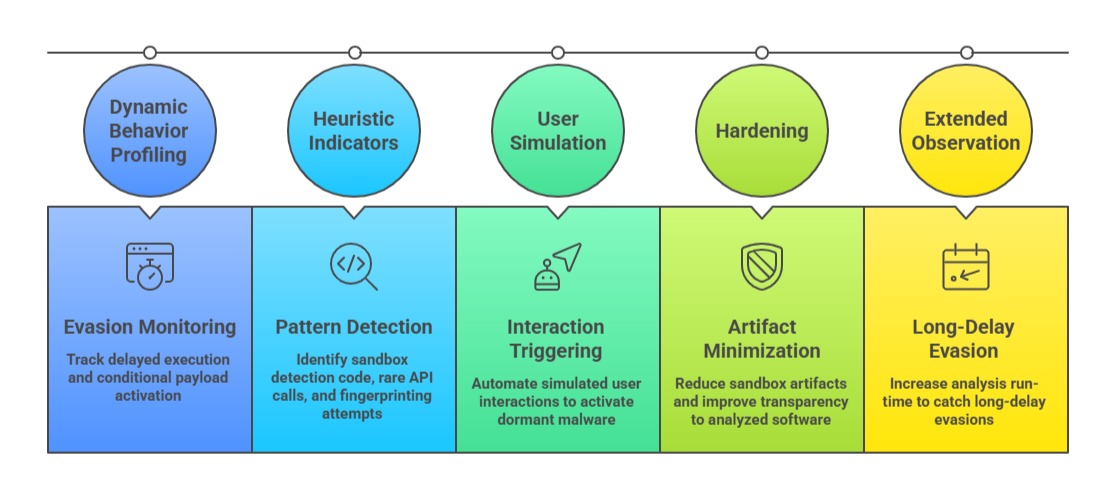
Conceptual Detection Strategies for Sandboxes
Conceptual sandbox strategies focus on exposing hidden or delayed malware behaviors. The points below highlight approaches that improve detection accuracy.