Active reconnaissance is a vital phase in penetration testing where the tester directly interacts with the target system to gather real-time, detailed information about its network and services.
Unlike passive reconnaissance, which collects data from publicly available resources without alerting the target, active recon involves probing the target through scans and tests that may be detected but provide more precise and actionable insights.
This proactive approach helps ethical hackers understand the target’s architecture, identify open ports, services running, and potential vulnerabilities, laying the groundwork for subsequent exploitation efforts.
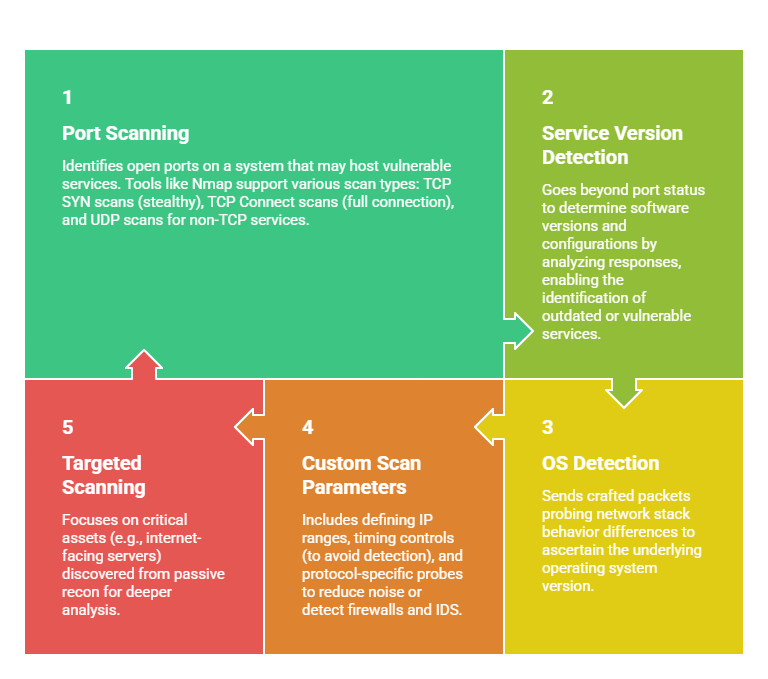
Custom Scanning Techniques
Custom scans tailor the probing process to the target’s environment and assessment goals, allowing penetration testers to gather focused intelligence efficiently. This involves adjusting scan types, timing, and scope for accuracy and stealth.
Service Fingerprinting
Service fingerprinting is the process of identifying the software applications and versions running on open ports discovered during scanning. This information is critical to assess known vulnerabilities and attack vectors specific to those services.
1. Banner Grabbing: Captures welcome messages or banners sent by services upon connection, which often disclose software type and version information.
2. Protocol Analysis: Analyzes network protocols’ nuances during handshake or data exchange phases to uniquely identify services running on a port.
3. Active Probing: Sends specific queries or malformed packets to elicit distinguishable reactions from different services or versions.
4. Machine Learning Approaches: Some advanced tools leverage machine learning models to improve fingerprinting accuracy based on traffic patterns.
Popular Tools for Active Reconnaissance
A variety of active scanning tools support the discovery of open ports, configurations, and vulnerabilities. The following tools are among the most widely utilized.
1. Nmap: Comprehensive scanner for port scanning, service/OS detection, and scriptable probes.
2. Nessus & OpenVAS: Vulnerability scanners combining active probing with vulnerability databases.
3. Netcat: Flexible utility for banner grabbing and manual probing.
4. Masscan: High-speed port scanner useful for large network sweeps.
5. Nikto: Web server scanner checking for vulnerabilities and misconfigurations.
Considerations and Best Practices
Ensuring proper execution during active reconnaissance starts with following the right guidelines. Here are the essential considerations every practitioner should review.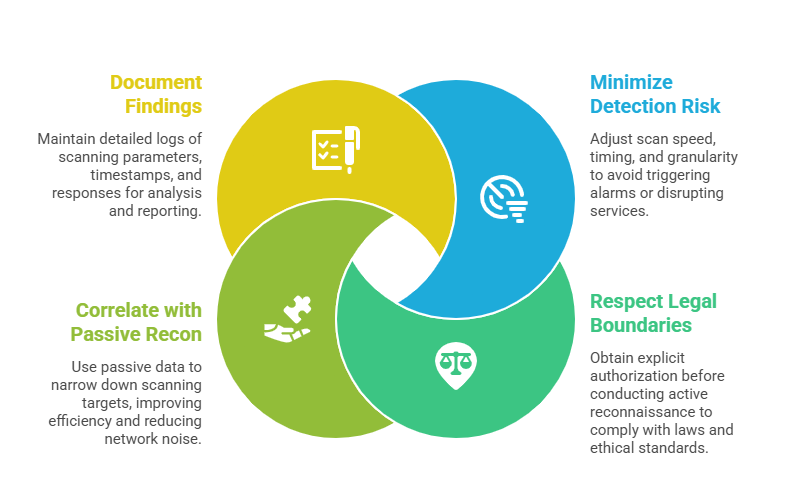
Practical Application in Penetration Testing
Active reconnaissance forms the backbone of practical penetration testing, enabling testers to find real-time weaknesses in network defense.
Custom scans and fingerprinting help validate passive intelligence and uncover hidden attack surfaces such as unauthorized services or misconfigurations.
When combined with later exploitation and post-exploitation phases, active recon techniques maximize the tester’s understanding of the target environment and risk.
Class Sessions
Sales Campaign

We have a sales campaign on our promoted courses and products. You can purchase 1 products at a discounted price up to 15% discount.
