Enumeration forms a critical phase in cybersecurity assessments, serving as the bridge between discovery and exploitation by gathering detailed information about targets such as systems, services, users, and configurations.
While many tools exist, writing custom enumeration scripts empowers security professionals to tailor scans precisely to target environments, automate repetitive tasks, and extract specific data points essential for vulnerability analysis.
Custom scripts enhance flexibility and efficiency, especially in unique or complex environments where off-the-shelf tools may fall short.
Importance of Custom Enumeration Scripts
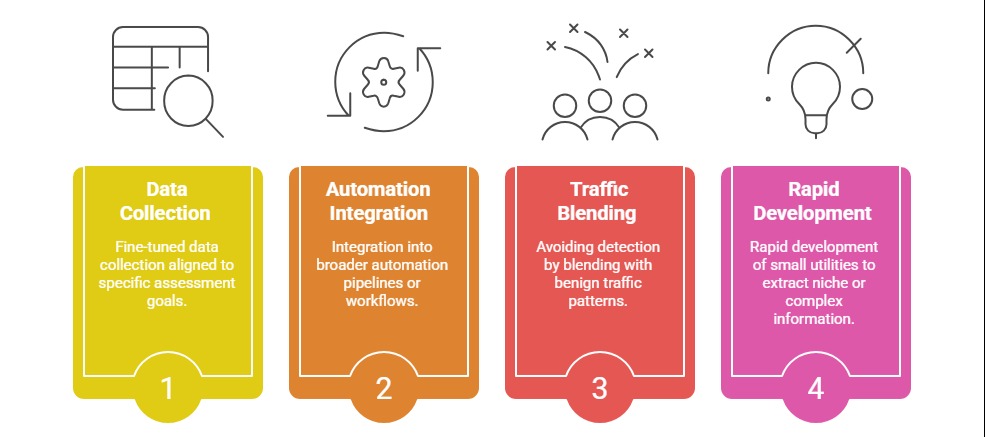
Pre-built tools can be limited by generic scope, detection by security mechanisms, or lack of specific tailored outputs. Custom scripts allow:
Core Components of Enumeration Scripts
To build a powerful enumeration script, several structural elements must be considered, ranging from target selection to reporting. These components ensure resilience, accuracy, and clarity throughout the entire process.
1. Target Identification: Focus your script on defining the enumeration target type such as IP ranges, hostnames, ports, or service endpoints.
2. Information Gathering: Implement functions to collect distinct information: user accounts, network shares, service banners, software versions, configurations, etc.
3. Data Parsing and Processing: Parse raw data outputs into structured formats for easier analysis—JSON, CSV, or log files.
4. Error Handling and Robustness: Ensure graceful handling of network errors, timeouts, or unexpected responses for reliable execution.
5. Output and Reporting: Generate concise logs or reports which highlight findings with clarity to inform remediation.
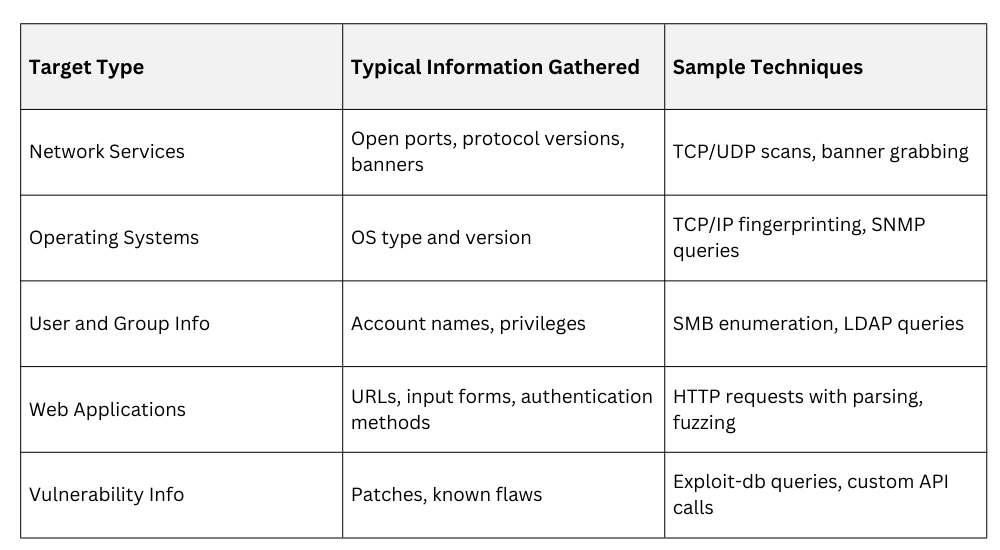
Common Enumeration Targets and Examples
Scripting Languages and Tools
Python: Very popular in security due to libraries like socket, scapy, requests, paramiko, and ldap3.
Bash: Ideal for simple network calls, command chaining, and automating system commands or existing tools.
PowerShell: Best suited for Windows environments for Active Directory, WMI, and advanced system enumeration.
Sample Python Snippet: Listing Open Ports
import socket
def scan_ports(target, ports):
for port in ports:
sock = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
sock.settimeout(1)
result = sock.connect_ex((target, port))
if result == 0:
print(f"Port {port} open on {target}")
sock.close()
target_ip = "192.168.1.1"
ports_to_scan = [22, 80, 443, 445]
scan_ports(target_ip, ports_to_scan)Best Practices for Custom Enumeration Scripts
1. Modular Design: Break your scripts into reusable functions for clarity and maintainability.
2. Documentation: Comment thoroughly and provide usage instructions for collaborators or future users.
3. Logging: Capture detailed logs with timestamps and error contexts.
4. Performance Optimization: Implement concurrency where appropriate to speed up scans.
5. Ethical Use and Authorization: Always ensure you have explicit permission and understand legal boundaries when enumerating targets.
Class Sessions
Sales Campaign

We have a sales campaign on our promoted courses and products. You can purchase 1 products at a discounted price up to 15% discount.
