Tool customization in cybersecurity involves modifying existing security tools or payloads to better suit specific testing environments, enhance capabilities, or adapt to evolving threats.
Ethical customization helps security professionals tailor solutions for unique scenarios, optimize effectiveness, and overcome limitations of generic tools.
This practice requires a balanced approach prioritizing responsible use, legal compliance, and transparency while maximizing the benefits of personalization.
Modifying Payloads: Customizing Attack Vectors
Payloads are codes or scripts delivered by exploits to execute specific actions like opening shells or executing commands.
Reasons for Payload Modification:
1. Bypassing Defense Mechanisms: Modify payloads to evade antivirus, intrusion prevention systems (IPS), or sandbox detections.
2. Target-Specific Adjustments: Adapt payloads to target operating system architectures, user environments, or network configurations.
3. Payload Size and Complexity Optimization: Simplify or extend payload functionality based on constraints or goals.
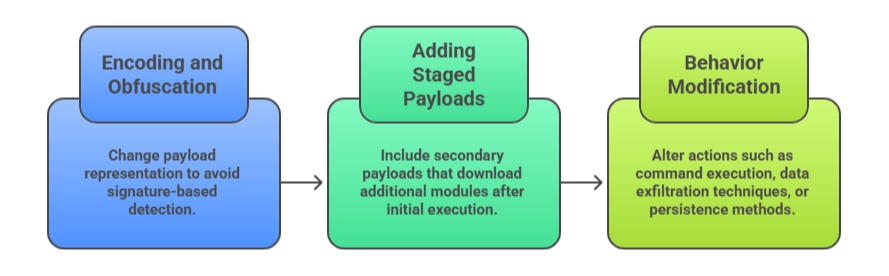
Common Payload Customizations:
Tools Used for Payload Modification: Include Metasploit Framework’s msfvenom, which enables customizable payload generation tailored to specific targets or evasion needs.
Shellcode sandbox environments are also used to safely test and analyze payload behavior. Additionally, custom scripting languages such as Python or Assembly allow precise crafting and fine‑tuning of payloads for more controlled and advanced modifications.
Extending Existing Tools Ethically
Ethical extension of tools involves enhancing features, functionalities, or integrations of established security tools.
Why Extend Tools: To address gaps or missing features in existing solutions, ensuring that all required functionality is available for security operations.
It also allows automation of repetitive or complex workflows, improving efficiency and consistency, and enables integration with organizational systems such as SIEM, ticketing, or orchestration platforms to streamline overall processes.
Ethical Considerations:
1. Ensure all modifications comply with software licenses and usage terms.
2. Avoid creating tools or functions intended for malicious purposes.
3. Maintain transparency and document changes for auditability.
4. Share improvements with the community when possible to aid collective defense.
Examples of Common Extensions:
1. Writing plugins or modules for frameworks such as Burp Suite, Metasploit, or Nmap.
2. Creating wrappers or scripts to automate chaining of security tools.
3. Developing customized scanners or fuzzers based on open-source tools.
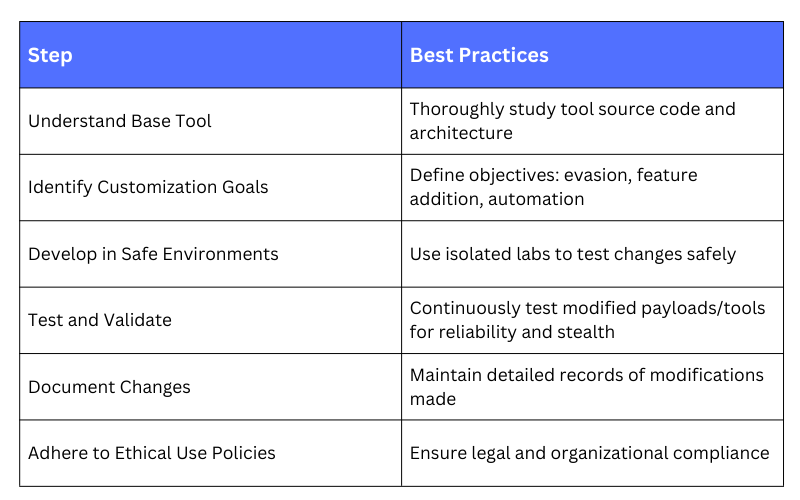
Practical Guidelines for Tool Customization