In cybersecurity, accurately assessing and prioritizing vulnerabilities is essential for effective risk management. Once a security assessment or vulnerability scan uncovers potential issues, organizations need a systematic way to evaluate their severity and potential impact.
This process involves mapping findings to established risk rating frameworks such as the Common Vulnerability Scoring System (CVSS) and conducting impact assessments.
These methods facilitate consistent, objective, and quantifiable evaluations, enabling teams to prioritize remediation efforts efficiently and allocate resources wisely.
Role of Risk Ratings in Security
Risk rating is important because it helps prioritize vulnerabilities based on their severity, potential impact, and likelihood of exploitation.
It guides strategic resource allocation by ensuring that high-risk issues are addressed first and communicates risk levels clearly to stakeholders and decision-makers.
Additionally, risk rating promotes consistency in evaluating vulnerabilities across different assessments, systems, and teams, supporting a more structured and effective security management approach.
Overview of the CVSS Framework
The Common Vulnerability Scoring System (CVSS) provides a standardized method to quantify the severity of vulnerabilities discovered in systems and applications.
CVSS Version 3.1 Components:
1. Base Metrics: Intrinsic features of a vulnerability, including:
2. Exploitability Sub-score: Attack vector, complexity, privileges required, user interaction.
3. Impact Sub-score: Confidentiality, integrity, and availability impacts.
4. Temporal Metrics: Changes over time (e.g., exploit code maturity).
5. Environmental Metrics: Customization based on organizational environment and specific impact.
CVSS Score Range:
1. Scores from 0.0 (no risk) to 10.0 (critical risk).
2. Classifications: Low (0-3.9), Medium (4.0-6.9), High (7.0-8.9), Critical (9.0-10).
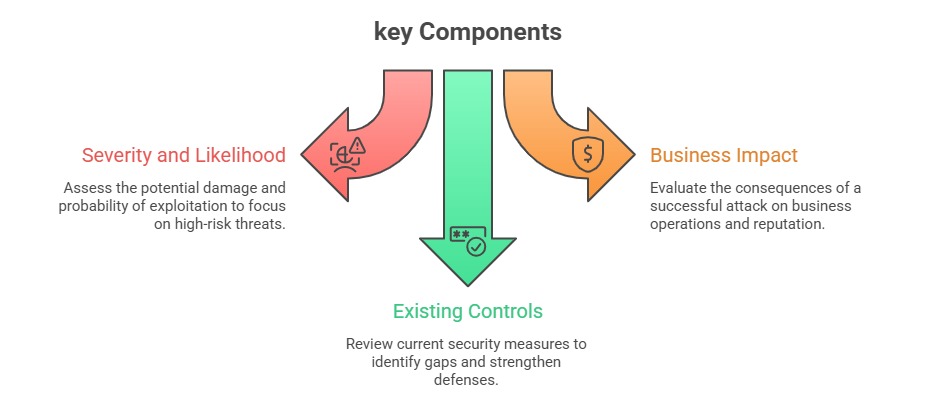
Impact Assessment in Risk Mapping
Impact assessment involves evaluating potential consequences of a vulnerability being exploited, considering both technical and business perspectives.
Key Impact Areas:
1. Confidentiality: Leaking sensitive data or secrets.
2. Integrity: Unauthorized modification of data or systems.
3. Availability: Disruption or denial of service.
4. Business Impact: Financial loss, legal/regulatory penalties, reputation damage.
Assessment Methods
Include consulting governance and compliance standards to ensure alignment with regulatory requirements.
Quantitative approaches, such as assigning monetary value to data or processes, provide measurable insights, while qualitative judgment leverages threat intelligence and organizational context to assess potential impact.
Additionally, scenario analysis can be used to simulate attack outcomes, helping organizations anticipate risks and prioritize mitigation strategies effectively.
Mapping Technical Findings to Risk Ratings
To turn technical findings into actionable insights, it is important to map vulnerabilities to risk ratings accurately. The points below provide a clear methodology for scoring, contextualizing, and prioritizing remediation efforts.
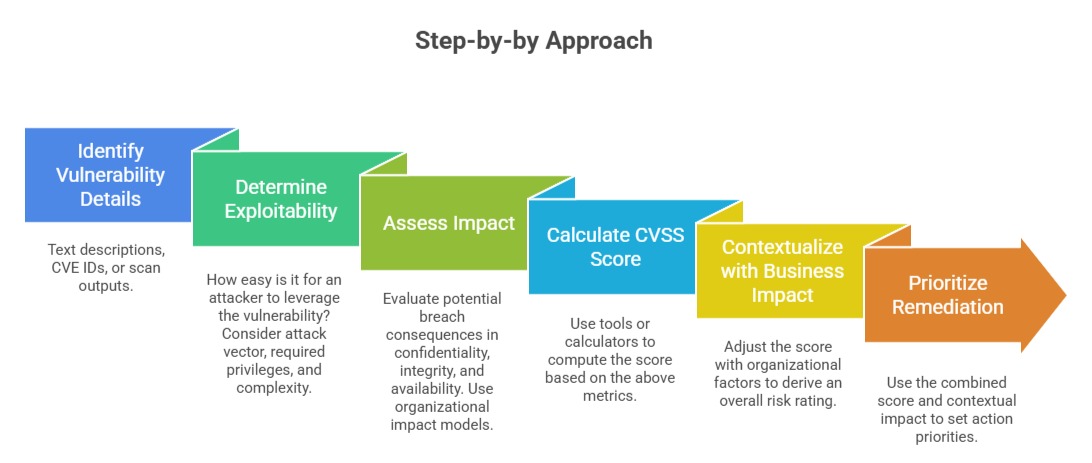
Tools and Resources:
1. CVSS calculators provided by NIST, FIRST, or CVSS Python libraries.
2. Custom risk matrices aligning CVSS scores with organizational impact levels.
3. Incident logs, threat intelligence, and historical data for context.
Practical Application: Example
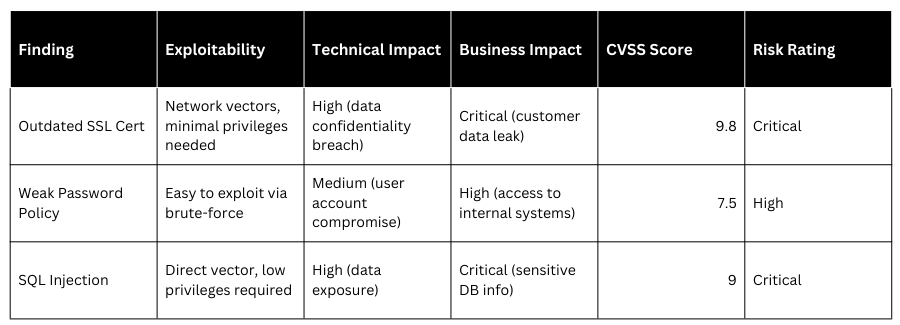
Best Practices for Effective Risk Mapping
1. Use Standard Frameworks: CVSS, NIST, or organization-specific methodologies.
2. Collaborate Across Teams: Include technical, business, and management perspectives.
3. Align Scores with Business Context: Adjust scores based on asset criticality and organizational priorities.
4. Document Assumptions & Justifications: Maintain transparency and reproducibility.
5. Review & Update Regularly: Reassess as threat landscapes evolve and remediation efforts progress.
