Cloud computing has revolutionized how organizations deploy applications, store data, and scale infrastructure. The three dominant cloud providers—Amazon Web Services (AWS), Microsoft Azure, and Google Cloud Platform (GCP)—offer diverse service models designed to meet varying business needs.
Understanding cloud service models (Infrastructure as a Service, Platform as a Service, and Software as a Service) and the shared responsibility model is essential for implementing secure cloud environments.
The shared responsibility model delineates security obligations between cloud providers and customers, ensuring clarity on who secures what components.
Cloud Service Models
Cloud services are categorized into three primary models, each offering different levels of control and management responsibilities.
1. Infrastructure as a Service (IaaS)
IaaS provides virtualized computing resources over the internet, including virtual machines, storage, and networking components.
Characteristics:
1. Users manage operating systems, applications, and data.
2. Providers manage physical infrastructure (servers, storage, networking hardware).
3. High flexibility and control for custom configurations.
Examples:
AWS: EC2 (Elastic Compute Cloud), S3 (Simple Storage Service)
Azure: Virtual Machines, Blob Storage
GCP: Compute Engine, Cloud Storage
Use Cases: Development and testing environments, hosting websites, big data analytics, backup and disaster recovery.
2. Platform as a Service (PaaS)
PaaS provides a platform allowing developers to build, deploy, and manage applications without managing underlying infrastructure.
 - visual selection-Picsart-CropImage.png)
Examples:
AWS: Elastic Beanstalk, Lambda
Azure: App Service, Azure Functions
GCP: App Engine, Cloud Functions
Use Cases: Application development, API management, microservices deployment, serverless computing.
3. Software as a Service (SaaS)
SaaS delivers fully functional applications over the internet, managed entirely by the provider.
Characteristics:
1. Providers manage everything: infrastructure, platform, and application.
2. Users access applications via web browsers or APIs.
3. Minimal user management responsibilities.
Examples:
AWS: Amazon WorkSpaces, Amazon Chime
Azure: Office 365, Dynamics 365
GCP: Google Workspace (Gmail, Drive, Docs)
Use Cases: Email, collaboration tools, customer relationship management (CRM), enterprise resource planning (ERP).
The Shared Responsibility Model
The shared responsibility model defines the division of security and compliance obligations between cloud providers and customers.
Core Principle: Cloud providers secure the infrastructure ("security of the cloud"), while customers secure their data, applications, and configurations ("security in the cloud").
Provider Responsibilities (Security OF the Cloud)
Providers are responsible for the security of the cloud, which includes safeguarding the physical data centers where infrastructure resides.
They must ensure the integrity and protection of hardware and network components, as well as the hypervisor and virtualization layers that support multiple tenants.
Additionally, cloud providers are accountable for the security of managed services and platform components, maintaining robust controls to prevent unauthorized access and ensure reliable operation.
Customer Responsibilities (Security IN the Cloud)
Customers are responsible for security in the cloud, which involves protecting their data through encryption and implementing strict access controls.
They must manage identities and permissions using Identity and Access Management (IAM) policies, as well as ensure the security of operating systems and applications running on cloud resources.
Additionally, customers are accountable for network configurations, such as firewalls and security groups, and for maintaining compliance with regulatory requirements and proper data governance practices.
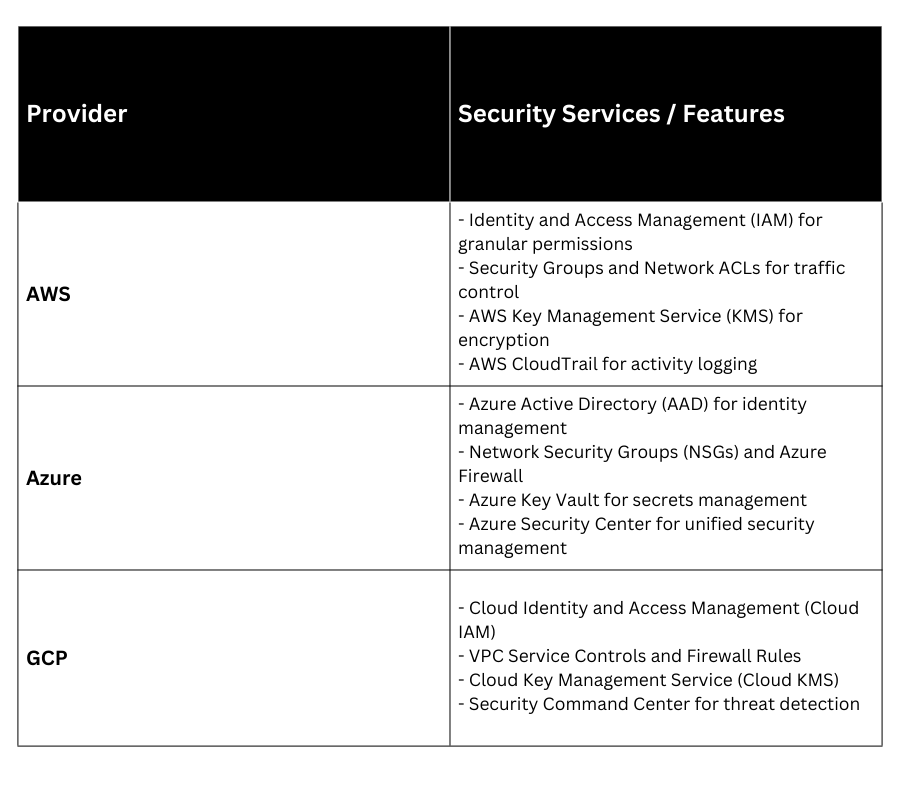
AWS, Azure, and GCP: Key Security Features
 Best Practices for Cloud Security
Best Practices for Cloud Security
1. Implement least privilege access using IAM policies.
2. Enable multi-factor authentication (MFA) for all accounts.
3. Encrypt data at rest and in transit using provider-managed or customer-managed keys.
4. Regularly audit configurations and access logs.
5. Use automated tools for continuous compliance monitoring.
6. Segment networks using Virtual Private Clouds (VPCs) and security groups.
7. Conduct regular penetration testing and vulnerability assessments.
