The proliferation of Internet of Things (IoT) devices across industries and homes has introduced new security challenges. IoT devices range from simple sensors to complex embedded systems interconnected via various networks.
Many of these devices are susceptible to unique security weaknesses due to constrained hardware, limited security features, and often rushed development cycles.
Key vulnerabilities include firmware flaws, usage of insecure protocols, and hardcoded credentials, all of which can expose IoT ecosystems to cyberattacks.
Firmware Analysis Basics
Firmware is the low-level software embedded in hardware devices responsible for controlling their functions. In IoT devices, it includes operating systems, drivers, and vendor-specific applications.
Importance of Firmware Security: Firmware vulnerabilities allow attackers to gain persistent, low-level access to a device, often bypassing traditional security controls.
Firmware Analysis Process:
1. Firmware Extraction: Obtain firmware images from device manufacturers, public sources, or raw dumps from devices.
2. Static Analysis: Reverse engineering binaries using tools such as IDA Pro, Ghidra, or Binwalk to identify code vulnerabilities, backdoors, or hardcoded secrets.
3. Dynamic Analysis: Emulating firmware in sandbox environments to observe behaviors or running tests for fuzzing and vulnerability discovery.
4. Configuration and Update Analysis: Inspect update mechanisms and configuration files for security weaknesses such as lack of signature verification.
Common Findings in Firmware: Unpatched vulnerabilities within the embedded operating system or software components, leaving devices exposed to known exploits. In many cases, developers unintentionally leave debug code enabled, which can provide unauthorized access pathways.
Additionally, hardcoded usernames, passwords, or cryptographic keys are frequently discovered, creating significant security risks if attackers gain access to the firmware.
Insecure Protocols in IoT
IoT devices communicate using various protocols, some of which lack adequate security.
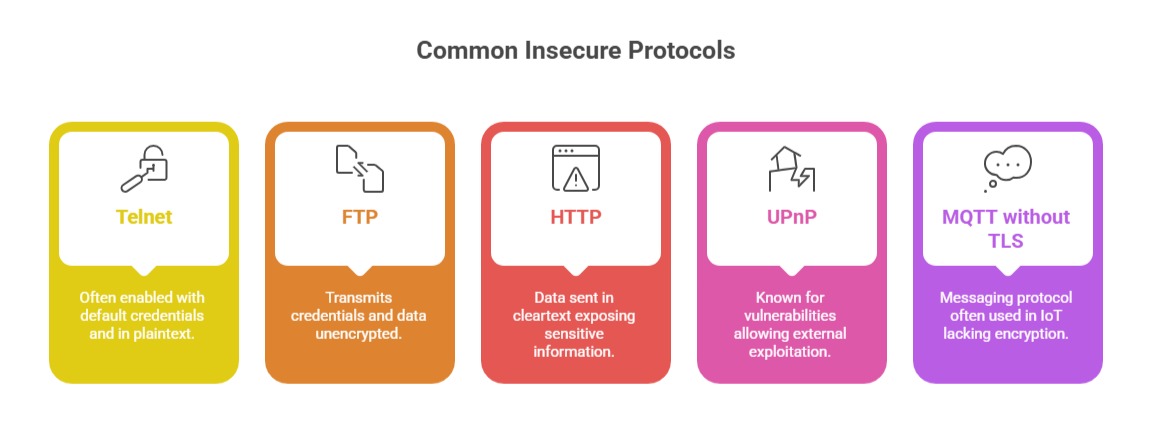 Risks of Insecure Protocols: Attackers can easily eavesdrop on transmitted information, intercepting sensitive or confidential data. These weaknesses also enable replay and man-in-the-middle attacks, allowing adversaries to modify or inject malicious content.
Risks of Insecure Protocols: Attackers can easily eavesdrop on transmitted information, intercepting sensitive or confidential data. These weaknesses also enable replay and man-in-the-middle attacks, allowing adversaries to modify or inject malicious content.
Furthermore, insecure protocols may permit unauthorized device control and manipulation, threatening both system integrity and user safety.
Mitigation: Adopt secure alternatives (SSH, SFTP, HTTPS, MQTT over TLS), enforce strong encryption, and disable unused services.
Hardcoded Credentials
Hardcoded credentials are pre-set usernames and passwords embedded directly into device firmware or software code.
Why Hardcoded Credentials are Dangerous: They cannot be modified by users, leaving devices permanently exposed once discovered. These fixed credentials are often reused across large numbers of devices, enabling attackers to compromise many systems with a single leaked password.
Additionally, they can be easily extracted through firmware analysis, giving adversaries straightforward access to sensitive functionality or full device control.
Examples:
1. Devices shipped with factory-default root/admin accounts and passwords.
2. Hardcoded API keys or encryption keys used for communication or updates.
Consequences: Attackers gain straightforward access to device controls, networks, or cloud services.
Detection and Mitigation:
1. Scan firmware for known default credentials and keys.
2. Use of automated tools to identify credential patterns in binaries.
3. Encourage or mandate credential randomization during device provisioning.
4. Use unique credentials or certificates per device.
