Man-in-the-Middle (MITM) attacks are a prevalent cybersecurity threat where an attacker secretly intercepts and potentially alters communication between two unsuspecting parties who believe they are directly communicating.
This attack compromises confidentiality and integrity, allowing attackers to steal sensitive data, inject malicious content, or impersonate one of the parties.
Two of the most commonly employed MITM techniques are ARP spoofing and DNS manipulation, which exploit vulnerabilities in network protocols to redirect or intercept traffic.
ARP Spoofing: Hijacking Local Network Traffic
The Address Resolution Protocol (ARP) is fundamental in local area networks (LANs) for mapping IP addresses to MAC (hardware) addresses, enabling proper routing of packets within a subnet.
ARP spoofing (or ARP poisoning) is an attack where the attacker sends forged ARP messages into the network, associating their MAC address with the IP address of a legitimate device—usually the default gateway or another trusted host.
How ARP Spoofing Works: By poisoning victim machines’ ARP tables with incorrect MAC-IP mappings, the attacker intercepts traffic intended for another device.
In this way, data packets flow through the attacker’s machine, allowing eavesdropping, data modification, or session hijacking. This type of MITM is particularly effective in switched Ethernet networks.
Consequences: Attackers can capture sensitive data like login credentials, inject malicious code, redirect traffic for phishing, or disrupt communications entirely.
Detection and Prevention: Techniques include static ARP entries, dynamic ARP inspection on managed switches, and using encryption to prevent unencrypted data interception.
DNS Manipulation: Redirecting Domain Name Resolutions
Domain Name System (DNS) is the internet’s directory service translating domain names into IP addresses.
DNS manipulation (including DNS spoofing or cache poisoning) is a MITM attack where attackers alter DNS resolution responses, leading victims to visit fraudulent or malicious websites without their knowledge.
How DNS Manipulation Works: Attackers inject false DNS records into a resolver’s cache or control responses in DNS proxying environments. When users attempt to visit a genuine website, they are redirected to attacker-controlled IP addresses or fake websites designed to steal credentials or distribute malware.
Types: DNS cache poisoning, DNS hijacking, rogue DNS servers, and DNS tunneling.
Impact: Enables phishing attacks, data theft, malware distribution, and circumvention of security controls.
Mitigation: Using DNSSEC to authenticate DNS responses, secure DNS resolvers, regular DNS cache flushing, and monitoring for unusual DNS traffic.
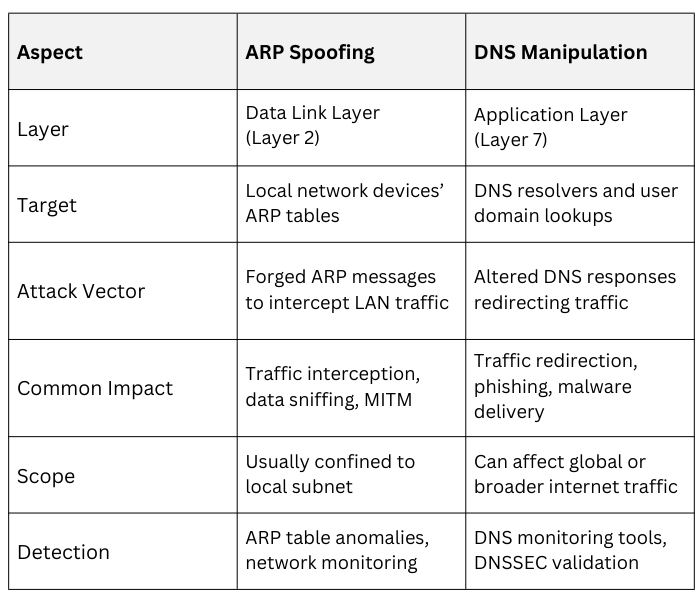
ARP Spoofing vs DNS Manipulation
Real-World Attack Examples
Real-world attacks often demonstrate how network manipulation techniques are used to compromise users.
In session hijacking through ARP spoofing, attackers intercept login sessions on local Wi-Fi networks, allowing them to capture sensitive information such as usernames and passwords.
Similarly, phishing attacks conducted through DNS spoofing redirect victims to fraudulent banking websites even when they enter the correct URL, resulting in the theft of account credentials.
These examples show how subtle network-level tampering can lead to severe security breaches.
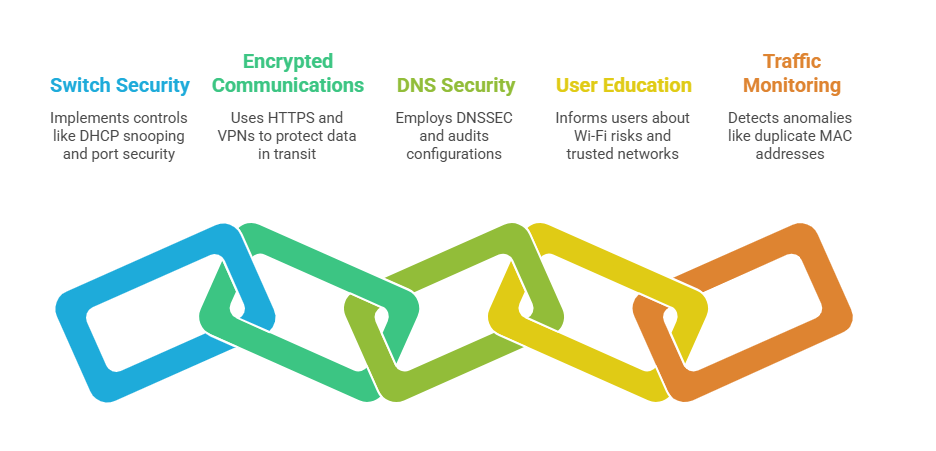
Defense Best Practices
Class Sessions
Sales Campaign

We have a sales campaign on our promoted courses and products. You can purchase 1 products at a discounted price up to 15% discount.