Modern web applications are complex systems composed of multiple interconnected components that interact through data exchanges, XML processing, serialization, and business logic workflows.
Security vulnerabilities such as Server-Side Request Forgery (SSRF), XML External Entity (XXE) injection, insecure deserialization, and logical flaws in application design pose significant risks.
These weaknesses can lead to unauthorized internal network access, information disclosure, remote code execution, or bypassing intended access controls.
Server-Side Request Forgery (SSRF)
SSRF occurs when an attacker manipulates a vulnerable server to make unintended HTTP or other network requests to internal or external resources. Since requests originate from the server, they bypass external firewalls or IP-based restrictions.
 - visual selection-Picsart-CropImage.png)
Detection: Look for input fields or parameters that accept URLs or IP addresses, and analyze how server-side requests handle them.
Mitigation: Strict input validation, whitelist allowed domains/IPs, disable unnecessary protocols, and use network-level segmentation.
XML External Entity (XXE) Injection
XXE is an injection attack targeting XML parsers that improperly process external entity references, allowing attackers to read files, perform SSRF, or execute denial of service attacks.
Attack Vectors:
1. Disclosure of sensitive files from the server.
2. SSRF or port scanning via crafted XML inputs.
3. Billion laughs denial of service attacks through recursive entities.
Prevention: Configure XML parsers to disable external entity processing, validate input strictly, or use safer data formats such as JSON.
Insecure Deserialization
Deserialization is the process of converting data streams back into objects. Insecure deserialization happens when untrusted or manipulated data is deserialized without proper validation, potentially enabling code execution, data tampering, or denial of service.
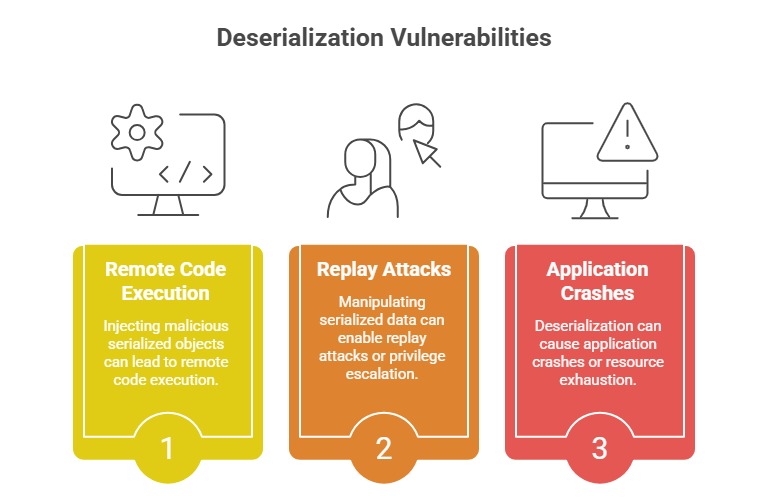
Detection and Prevention: Avoid accepting serialized objects from untrusted or unauthenticated sources. Implementing integrity checks or digital signatures on serialized data helps ensure that objects have not been tampered with before processing.
Additionally, enforcing strict type constraints and thorough validation during deserialization significantly reduces the risk of malicious payloads being executed.
Logic Flaw Identification
Logic flaws occur when the application's business rules or workflows contain security weaknesses not due to coding bugs but flawed logic or assumptions.
Examples:
1. Bypassing multi-step processes.
2. Circumventing payment or authorization flows.
3. Race conditions enabling privilege escalation.
Detection: Manual code reviews, threat modeling, and scenario-based testing are effective in uncovering logic flaws.
Mitigation: Implement robust business rule validations, conduct peer reviews, and incorporate unit and integration tests focusing on logical correctness.
