Reverse engineering is a systematic process in cybersecurity and software analysis used to understand the structure, functionality, and behavior of compiled or binary software without access to its source code.
It plays a crucial role in vulnerability research, malware analysis, software debugging, and interoperability. Central to reverse engineering are techniques such as string analysis, disassembly, and understanding program logic flow.
Strings Analysis: The Starting Point
Strings are sequences of readable characters embedded within binary files, often revealing valuable contextual information like file paths, error messages, URLs, or commands.
Purpose of Strings Analysis: To uncover useful clues about a software program’s functionality and intent by examining readable text embedded within the binary.
It can reveal hardcoded information such as usernames, URLs, or API keys that may indicate configuration details or hidden behaviors, and it often exposes embedded error messages or debugging data that further aids in understanding how the software operates.
Tools and Techniques:
1. Utilities such as strings (Linux/Windows) extract printable text from binaries.
2. Manual inspection of strings aids hypothesis building before deeper analysis.
Limitations: Obfuscated or encrypted strings cannot be easily interpreted without additional decoding, reducing the usefulness of direct extraction.
Additionally, some binaries contain very few or no meaningful strings, which limits the amount of actionable information that can be gathered through this method alone.
Disassembly: Translating Machine Code to Human-Readable Instructions
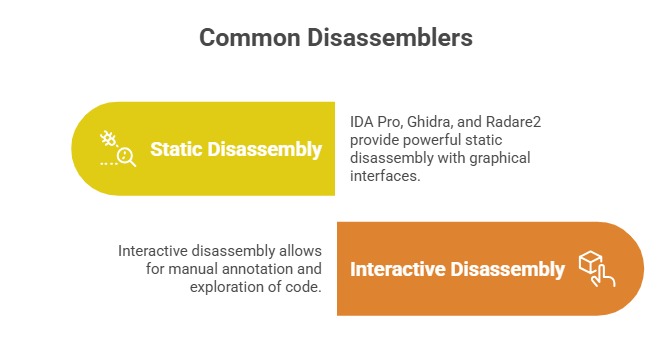
Disassembly converts machine-level binary code into assembly instructions that a human can analyze.
Core Concepts:
1. Assembly language corresponds closely to CPU instructions, revealing program behavior.
2. Disassemblers generate mnemonics and operands from binary instructions without altering execution.
Applications: Locating program entry points and function boundaries to understand the structure and flow of execution.
It also helps identify suspicious machine instructions associated with buffer overflows, system calls, or cryptographic operations, while supporting integrity verification by detecting tampered or injected code within the binary.
Logic Flow Understanding: Mapping Program Execution
Understanding the control flow and logic structure helps reverse engineers comprehend the software’s operational flow.
Control Flow Analysis: Identify the sequence and branching of instructions within a program, including loops, conditionals, and function calls, providing insight into its execution logic.
Control Flow Graphs (CFGs) are often used to visualize these paths, making it easier to conceptualize program flow and understand potential execution scenarios.
Data Flow Analysis: Tracks how data moves and transforms within a program, allowing analysts to identify dependencies and critical variables.
This technique is particularly useful for understanding how inputs influence outputs and for pinpointing areas where sensitive data is handled, which can help in detecting vulnerabilities or potential security risks.
Reverse Engineering Steps for Logic Understanding:
1. Analyze function prologues and epilogues to segment code into logical units.
2. Identify and categorize function calls and jumps.
3. Interpret conditional branches to determine decision-making logic.
4. Correlate data manipulations to high-level program behavior.
-Picsart-CropImage.png)
