A professional penetration test report is a vital document that effectively communicates the findings, risks, and recommendations derived from an organization’s security assessment.
While technical details are essential for the security team, the report must also be accessible to executive management, compliance officers, and stakeholders without technical backgrounds.
A well-structured report not only provides clarity but also facilitates actionable insights that can drive security improvements.
Essentials of Penetration Test Reports
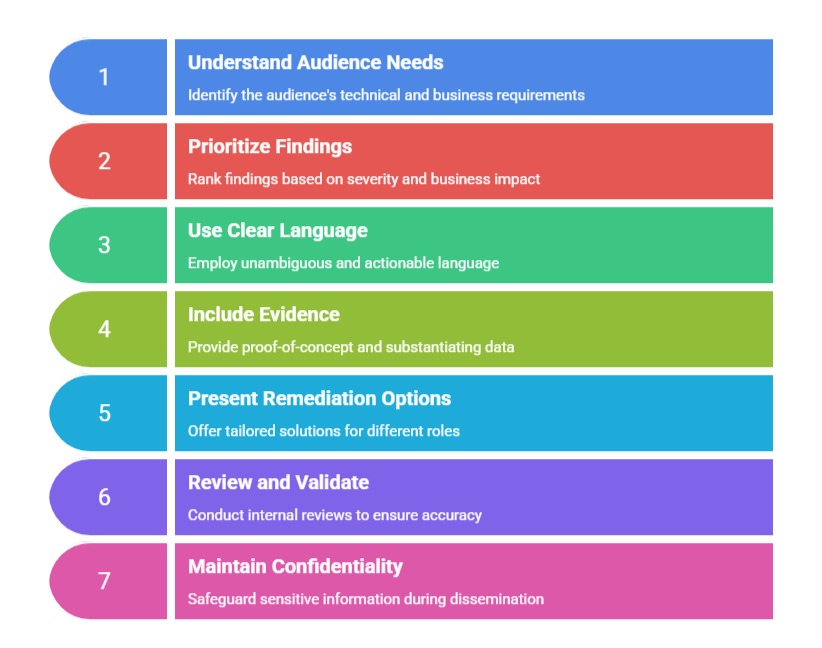
To support remediation, governance, and compliance, pen test reports must be both detailed and accessible. Below are the key essentials that guide their structure and purpose.
Key Objectives:
1. Communicate vulnerabilities clearly and accurately.
2. Explain risks and potential impacts in understandable language.
3. Offer prioritized mitigation strategies.
4. Maintain transparency, traceability, and reproducibility.
Audience:
1. Technical teams: Require detailed findings, technical details, and proof-of-concept.
2. Management: Focus on high-level risks, business impacts, and strategic recommendations.
3. Auditors and compliance bodies: Need documented scope, methodology, and evidence for validation.
Core Components of a Penetration Test Report
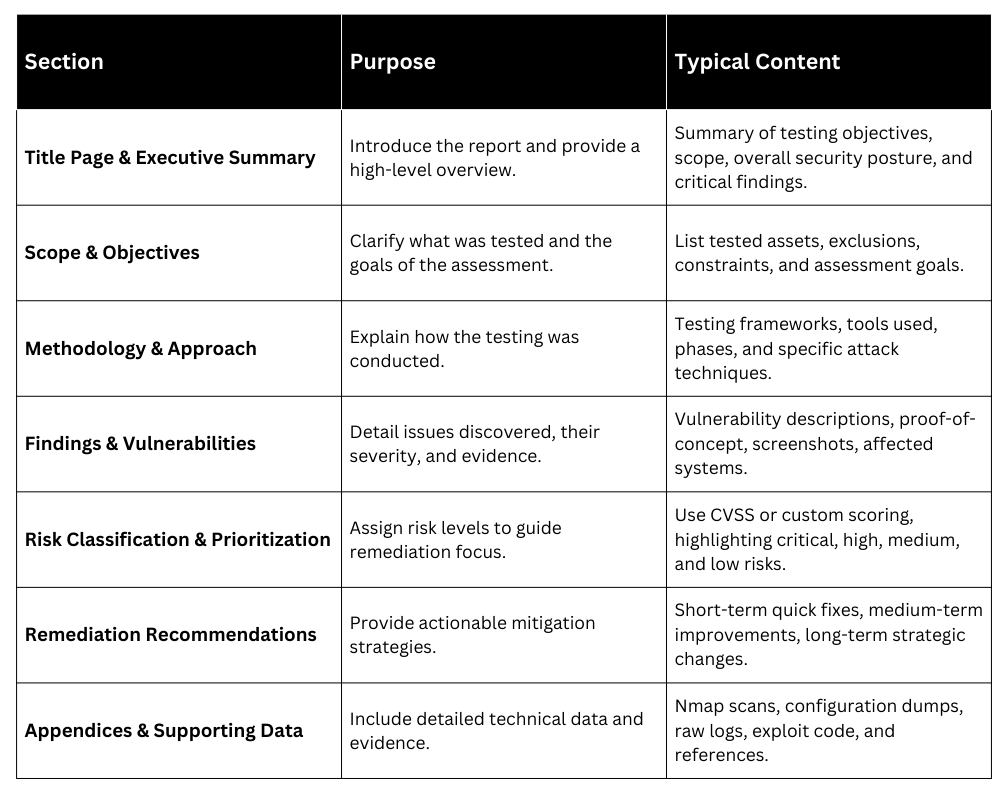
Note: Keep each section concise but detailed enough for the target audience. Use high-level summaries for management and detailed technical descriptions for engineers.
Formatting Best Practices
Well-structured formatting enhances communication and supports accurate analysis. Below are the essential practices that help create polished, reliable security documents.
1. Consistency: Use a clear, uniform template with consistent headers, numbering, and font styles.
2. Clarity: Write in plain language; avoid jargon unless explaining technical terms.
3. Visual Aids: Incorporate tables, charts, and diagrams to illustrate complex points.
4. Reproducibility: Include detailed steps, commands, and tools used to allow verification and follow-up testing.
5. Traceability: Reference findings back to vulnerability identifiers, CVEs, or framework mappings like MITRE ATT&CK.
Industry-Standard Templates & Examples
Many organizations adopt templates from reputable sources such as OWASP and NIST to structure their security assessments. These templates typically include sections covering scope, methodology, findings, risk evaluation, and recommendations.
A variety of open-source and commercial templates are also available—either free or for purchase—and can be customized to align with specific organizational policies and requirements.
Sample Resources:
1. OWASP Penetration Test Reporting Standard (OPTRS) – a structured, machine-readable format.
2. TERASORT or TCM Security templates available online in LaTeX, Word, or Markdown formats.
3. GitHub repositories with example reports (e.g., h0tPlug1n's GitHub repo).