Cloud computing offers unparalleled scalability, flexibility, and cost-efficiency, but it also introduces complex security challenges.
Cloud misconfigurations errors in settings and policies represent one of the most common and exploitable vulnerabilities in cloud environments.
These misconfigurations occur across Identity and Access Management (IAM), storage buckets, exposed services, and network settings, often resulting from human error, lack of knowledge, or inadequate security governance.
Attackers actively scan for misconfigured cloud resources to gain unauthorized access, exfiltrate data, or disrupt services.
Identity and Access Management (IAM) Misconfigurations
IAM controls who can access cloud resources and what actions they can perform. Misconfigurations in IAM policies create serious security gaps.
Common IAM Misconfigurations:
1. Overly Permissive Policies: Granting excessive permissions such as *:* (all actions on all resources) or administrative rights to users who don't require them.
2. Publicly Accessible IAM Roles: IAM roles configured with trust policies allowing anonymous or external accounts to assume them.
3. Weak Password Policies: Inadequate password complexity requirements or absence of multi-factor authentication (MFA).
4. Stale or Orphaned Credentials: Unused access keys, inactive accounts, or credentials left active after employees leave.
5. Service Account Abuse: Service accounts with elevated privileges used across multiple applications without proper isolation.
Impact: Unauthorized access, privilege escalation, lateral movement, data theft, and full account compromise.
Detection and Prevention
1. Apply the principle of least privilege.
2. Regularly audit IAM policies and access logs using tools like AWS IAM Access Analyzer, Azure Policy, or GCP Policy Analyzer.
3. Enforce MFA for all user accounts.
4. Rotate credentials regularly and remove unused keys.
5. Use automated scanning tools to detect overly permissive policies.
Storage Bucket Misconfigurations
Cloud storage services (AWS S3, Azure Blob Storage, GCP Cloud Storage) are frequently misconfigured, exposing sensitive data publicly.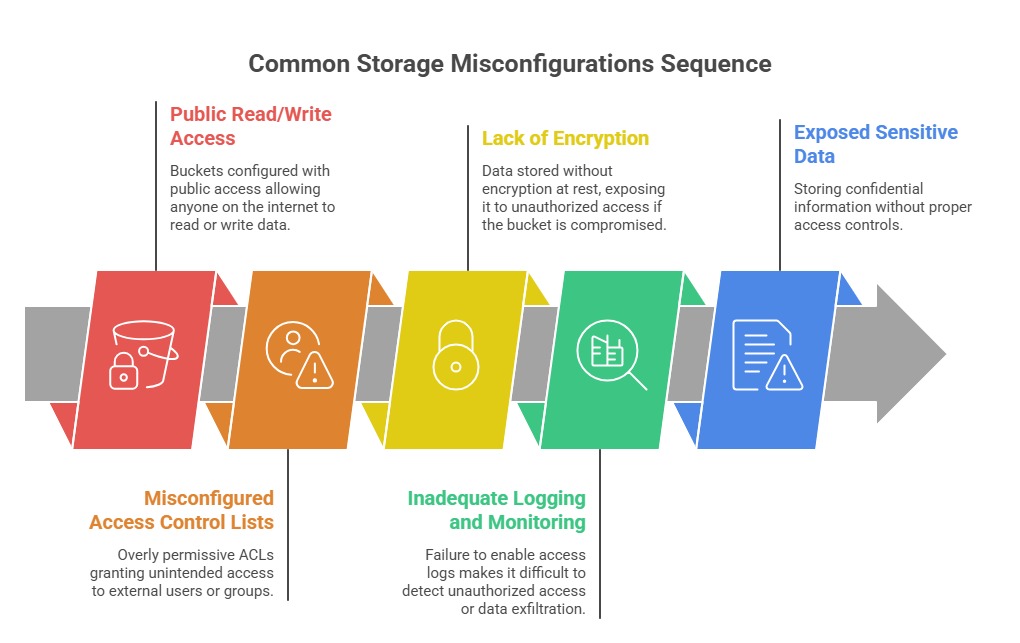
Real-World Examples: Numerous data breaches have resulted from publicly accessible S3 buckets containing customer data, financial records, or proprietary information.
Impact: Data breaches, regulatory fines, reputational damage, intellectual property theft.
Detection and Prevention:
1. Disable public access by default using bucket policies and block public access settings.
2. Implement encryption at rest and in transit.
3. Enable access logging and monitoring with alerts for suspicious activities.
4. Regularly scan buckets using tools like ScoutSuite, Prowler, or cloud-native security tools.
5. Classify data and apply appropriate access controls based on sensitivity.
Exposed Services and Network Misconfigurations
Cloud services and resources can be inadvertently exposed to the internet due to misconfigured network settings.
Common Exposures:
1. Open Security Groups/Firewall Rules: Security groups allowing inbound traffic from 0.0.0.0/0 (anywhere) on sensitive ports (SSH port 22, RDP port 3389, database ports).
2. Publicly Accessible Databases: Databases (RDS, Azure SQL, Cloud SQL) exposed to the internet without proper authentication or IP whitelisting.
3. Unsecured APIs and Endpoints: APIs deployed without authentication, rate limiting, or encryption.
4. Misconfigured Load Balancers: Load balancers exposing backend services directly to the internet.
5. Unpatched Services: Running outdated software or services with known vulnerabilities on publicly accessible instances.
Impact: Unauthorized access, data theft, service disruption, ransomware attacks, cryptomining abuse.
Detection and Prevention:
1. Implement principle of least exposure—restrict access to only necessary IP ranges.
2. Regularly audit security groups, network ACLs, and firewall rules.
3. Use Virtual Private Clouds (VPCs) with proper segmentation and private subnets.
4. Enable logging and intrusion detection systems (IDS) to monitor network traffic.
5. Conduct automated vulnerability scanning and penetration testing.
Class Sessions
Sales Campaign

We have a sales campaign on our promoted courses and products. You can purchase 1 products at a discounted price up to 15% discount.
