Wi-Fi networks are a critical component of modern connectivity, especially in enterprise environments where they support large numbers of devices and sensitive operations.
The increasing reliance on wireless communication brings inherent security challenges, as attackers continuously develop sophisticated methods to exploit vulnerabilities in Wi-Fi protocols and configurations.
WPA3, the latest Wi-Fi security standard, offers significant improvements over previous versions but also introduces new considerations and attack surfaces.
Understanding common Wi-Fi attacks, the security enhancements of WPA3, and the unique challenges in enterprise networks is essential for protecting wireless infrastructures.
Common Wi-Fi Security Attacks
Understanding common Wi-Fi attacks is essential for building strong defensive strategies and minimizing exposure. The list below highlights the most prevalent and dangerous methods used by attackers.
1. Evil Twin Attacks: Attackers set up rogue access points mimicking legitimate Wi-Fi networks to trick users into connecting, enabling data interception or credential theft.
2. Man-in-the-Middle (MITM) Attacks: Intercepting data between a client and access point to capture sensitive information or inject malicious content.
3. KRACK (Key Reinstallation Attacks): Targeting vulnerabilities in the WPA2 protocol’s four-way handshake to decrypt and manipulate traffic.
4. Brute Force and Dictionary Attacks: Attempting to crack Wi-Fi passwords, especially weak or pre-shared keys, by systematically trying numerous combinations.
5. Packet Sniffing and Replay Attacks: Capturing wireless traffic and replaying packets to cause disruption or unauthorized access.
6. Deauthentication Attacks: Forcing disconnection of clients from access points, creating denial-of-service or facilitating MITM setups.
WPA3 Security Enhancements and Considerations
WPA3 was engineered to mitigate common attack vectors and deliver higher assurance against wireless threats. The following sections summarize its major security advancements and practical considerations.
1. Improved Encryption and Authentication:
Simultaneous Authentication of Equals (SAE): WPA3 replaces Pre-Shared Key (PSK) exchange with SAE, a more secure handshake resistant to offline dictionary attacks.
Forward Secrecy: Protects past sessions even if credentials are compromised in the future.
2. Enterprise Mode Enhancements: 192-bit Security Suite: Provides stronger cryptographic algorithms for enterprise environments requiring higher security assurance.
3. Protected Management Frames (PMF): Mandatory in WPA3, PMF protects management frames to prevent spoofing and disconnection attacks.
4. Transition Mode: Allows coexistence of WPA2 and WPA3 devices to ensure compatibility but may reduce security until full WPA3 adoption.
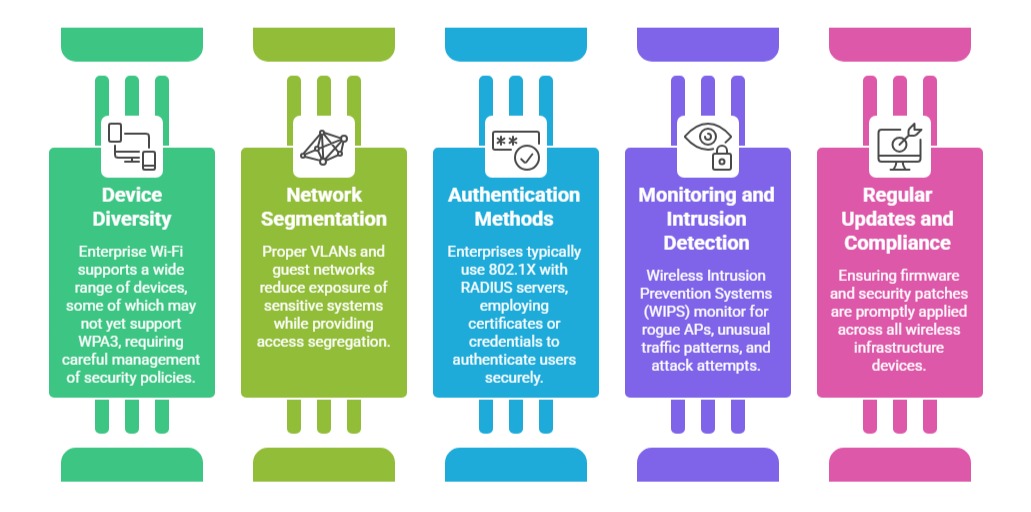
Enterprise Network Challenges and Strategies
Enterprise Wi-Fi infrastructures must accommodate diverse devices and evolving threats while maintaining strict compliance. The list below outlines key challenges and corresponding strategies.