Malware behavior analysis is a fundamental practice in cybersecurity aimed at understanding the functionality, impact, and indicators of compromise of malicious software.
Effective malware analysis supports threat detection, incident response, and the development of mitigation strategies.
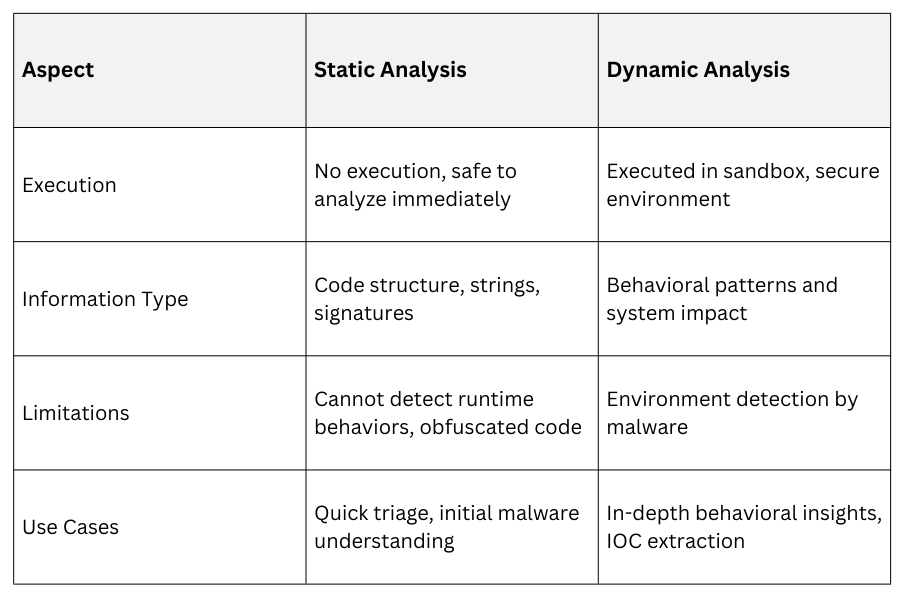
Two primary approaches dominate malware analysis: static and dynamic. Static analysis involves examining the malware without executing it, focusing on code and structure.
Dynamic analysis involves running the malware in a controlled environment to observe its behavior.
Static Malware Analysis
Static analysis inspects malware artifacts without execution, offering a safe and quick method to extract insights.
Key Aspects of Static Analysis:
1. File Examination: Analyze executable files, scripts, or binaries.
2. Disassembly and Decompilation: Use tools to convert binary code into assembly or higher-level language for inspection.
3. Signature and Hash Matching: Compare files against known malware databases to identify variants.
4. String Analysis: Extract readable text strings within binaries that may reveal URLs, commands, or payload details.
5. Structure and Header Analysis: Inspect file headers, PE (Portable Executable) sections, and embedded resources.
6. Code Flow and Pattern Recognition: Analyze control flow graphs to understand program structure and suspicious patterns.
Benefits: Absence of any risk of system infection, allowing safe examination of potentially harmful files. This approach also enables early intelligence generation before a full sandbox environment is set up, making it especially useful for processing and analyzing large batches of samples efficiently.
Tools:
1. IDA Pro, Ghidra (disassemblers)
2. Strings utility
3. YARA rules (pattern matching)
4. PEStudio (file metadata analysis)
Dynamic Malware Analysis
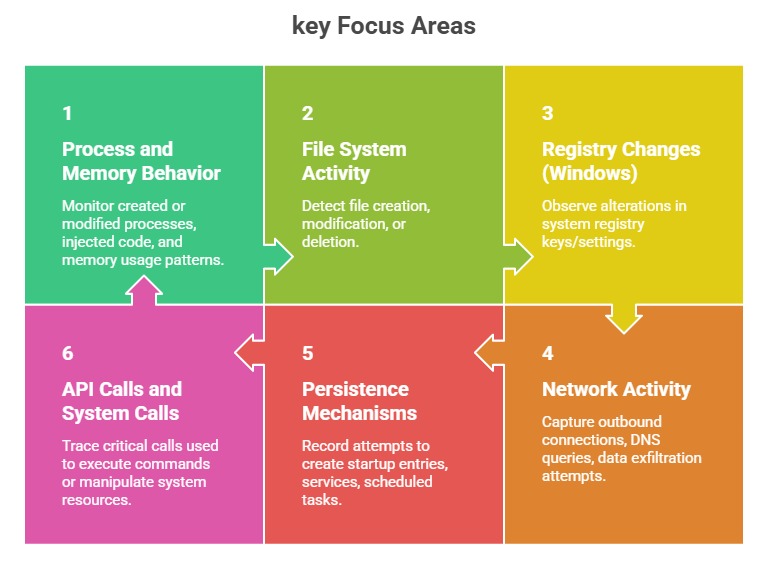
Dynamic analysis involves executing malware within a controlled, instrumented environment (sandbox) to observe its real-time behavior.
 or
or
Benefits: Uncovering runtime behavior and tactics that may be hidden through code obfuscation, offering deeper visibility into how malware actually operates. It also helps detect payloads that execute only under specific environmental conditions and provides rich indicators of compromise (IOCs), enabling stronger detection and response efforts.
Tools:
1. Cuckoo Sandbox, Any.Run
2. Process Monitor, Wireshark
3. Sysinternals Suite
4. Frida for live instrumentation
Complementary Nature of Static and Dynamic Analysis
Best Practices for Malware Analysis
1. Combine static and dynamic methods to gain comprehensive understanding.
2. Use isolated, instrumented environments for dynamic analysis to prevent spread.
3. Automate with sandbox technologies for scalability.
4. Archive analysis artifacts and reports for threat intelligence sharing.
5. Continuously update analysis tools to cope with evolving malware techniques.
