Firewalls and Intrusion Detection/Prevention Systems (IDS/IPS) are cornerstone technologies in network security, acting as gatekeepers that monitor, filter, and block malicious traffic to protect organizational assets.
However, skilled ethical hackers and attackers alike seek to bypass these defenses to access protected resources or conduct stealthy attacks.
Bypassing firewalls and IDS/IPS involves using evasion strategies designed to avoid detection, either by manipulating packet contents, altering attack signatures, or exploiting weaknesses in security device configurations.
Understanding Firewalls and IDS/IPS
Firewalls: Enforce network access policies by inspecting incoming and outgoing traffic based on predefined security rules such as IP addresses, ports, and protocols. They may function at different layers (packet filtering, stateful inspection, application layer).
IDS (Intrusion Detection Systems): Monitor network traffic for suspicious patterns or known attack signatures and alert administrators of potential threats.
IPS (Intrusion Prevention Systems): Like IDS but can actively block or reject malicious traffic based on detection.
While these systems are effective, their detection capabilities rely on known signatures, traffic anomalies, and protocol expectations, all of which can be circumvented through clever techniques.
Common Evasion Strategies for Firewalls and IDS/IPS
Presented here are common evasion approaches used against firewall and IDS/IPS technologies. These methods reveal how threat actors try to bypass traditional security layers.
1. Fragmentation: Splitting traffic into smaller packet fragments to evade signature-based detection since some IDS/IPS fail to properly reassemble packets before inspection.
2. Encryption and Tunneling: Using VPNs, SSL/TLS encryption, or protocols like SSH tunneling to hide the true payload from inspection systems.
3. Protocol Obfuscation: Altering protocol behaviors (e.g., executing commands in non-standard order or using uncommon protocol flags) to bypass protocol-specific detection rules.
4. Polymorphic Payloads: Employing payloads that change their signatures dynamically (e.g., using polymorphic malware or custom encryption) to avoid matching known malicious patterns.
5. Traffic Timing and Rate Manipulation: Slowing down attack traffic or sending it sporadically to avoid threshold-triggered alerts or anomaly detection.
6. Encoding and Encryption of Payloads: Transporting payloads encoded in formats like Base64 or using layered encryption to hide attack content.
7. IP Spoofing: Using forged source IP addresses to evade IP-based filtering or tracking.
8. Bypassing with Allowed Traffic: Leveraging permitted protocols or ports (such as HTTP/HTTPS) to tunnel malicious payloads, commonly called “living off the land.”
9. Evasion via Decoys or Noise: Sending benign traffic interspersed with malicious packets to confuse detection mechanisms.
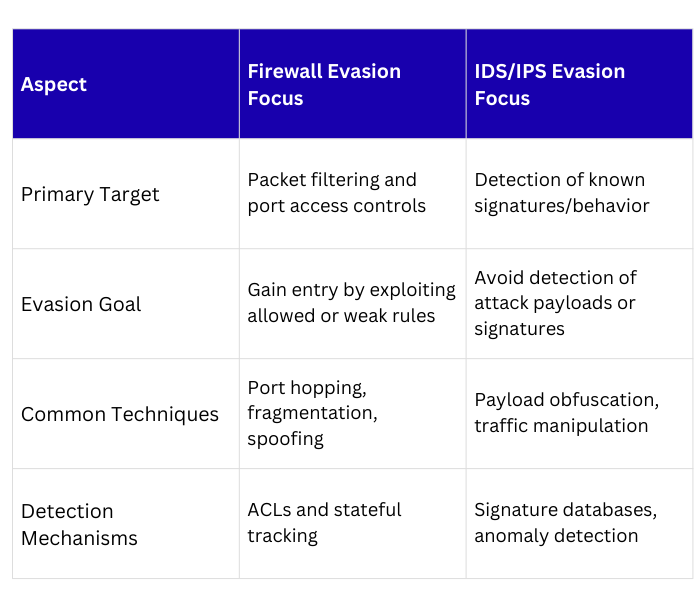
Bypassing Firewalls vs IDS/IPS
Best Practices for Defenders
1. Deploy deep packet inspection (DPI) capable firewalls and IDS/IPS.
2. Regularly update signature databases and detection rules.
3. Implement behavioral anomaly detection alongside signature-based methods.
4. Use SSL/TLS inspection to decrypt and inspect encrypted traffic.
5. Monitor network traffic for unusual fragmentation or tunneling patterns.
6. Maintain strict access controls and multi-layered defense strategies.
Ethical and Operational Considerations
Ethical hackers use these evasion techniques within authorized penetration tests to expose weaknesses, enabling organizations to implement effective countermeasures.
All evasion testing must follow strict legal and ethical guidelines, ensuring no harm or unauthorized access.
