Wireless networks are vital for enterprises, public spaces, and personal use due to their convenience and mobility. However, the wireless medium's openness also creates significant security vulnerabilities, notably the threat posed by rogue access points and evil twin attacks.
Rogue access points are unauthorized devices that connect to or are introduced into a network without approval. Evil twin attacks are a sophisticated subset, where attackers deliberately set up malicious access points that mimic legitimate networks to deceive users.
These techniques can lead to data interception, credential theft, malware distribution, and unauthorized network access. Recognizing how such attacks work, their techniques, and prevention methods is critical for maintaining a secure wireless environment.
Rogue Access Points
A rogue access point (AP) is an unauthorized wireless device connected to a network, either maliciously installed by an insider or attacker or accidentally by employees.
Rogue APs can pose severe security risks, mainly because they can act as entry points for attackers, intercept traffic, or facilitate lateral movement within an organization.
 Detection Challenges: Rogue APs often resemble legitimate access points, using similar SSID names or MAC addresses. They can be easily overlooked without proper wireless network monitoring.
Detection Challenges: Rogue APs often resemble legitimate access points, using similar SSID names or MAC addresses. They can be easily overlooked without proper wireless network monitoring.
Techniques of Rogue Access Points
1. Unsanctioned Deployment: Rogue APs are physically connected or placed in proximity to the network without approval, often in areas with weak monitoring.
2. Evil Twin Setup: Attackers create rogue APs that replicate the SSID (network name) and security settings of legitimate networks, making it difficult for users to distinguish.
Why Rogue APs Matter: They can be used to launch Man-in-the-Middle (MitM) attacks, steal credentials, or inject malware. Rogue APs can facilitate lateral movement inside corporate networks. They cam also create vulnerabilities that can be exploited for broader attacks.
An Evil Twin Attack
An evil twin is a malicious wireless access point that mimics a trusted, legitimate Wi-Fi network to deceive users into connecting to it.
Once connected, attackers can intercept data, steal credentials, or inject malicious content. Evil twin attacks leverage deception by cloning SSID names and sometimes copying the encryption settings of the original network.
Operational Steps:
1. Setup: Attackers deploy a rogue AP with the same SSID and security settings as the legitimate network, often with a stronger signal.
2. Luring Users: As users search for the trusted network, their devices automatically connect to the fake AP.
3. Interception & Exploitation: Once connected, attackers intercept data, capture login credentials, or redirect victims to malicious sites.
Tactics to Increase Success: Using high-powered antennas or devices to broadcast a stronger signal than the legitimate access point. Attackers may also disable or disrupt the real AP through denial-of-service techniques, forcing users to reconnect to the rogue network.
Additionally, rotating MAC addresses or adjusting beacon intervals helps the malicious access point evade detection by security tools and network monitoring systems.
-Picsart-CropImage.png)
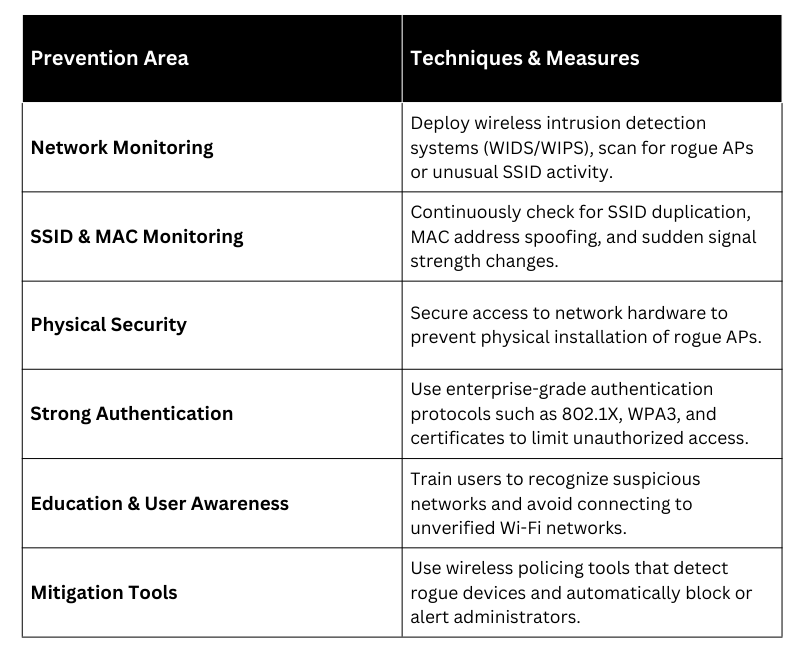
Detection and Prevention Strategies
Examples of Real-World Incidents
1. Corporate Espionage: Attackers set up evil twins near corporate offices to capture insider credentials or sensitive communications.
2. Public Wi-Fi Attacks: Rogue APs in coffee shops or airports intercept customer data or perform phishing attacks.
3. Healthcare Risks: Rogue APs in medical facilities intercept patient data or manipulate medical device communications.
