Privilege escalation remains one of the most critical phases in penetration testing and cybersecurity assessments.
Once an initial foothold is achieved on a Windows or Linux system, attackers aim to elevate their privileges from limited user rights to full administrative or root access.
This escalation allows access to sensitive data, system configurations, and control over the entire environment.
Advanced privilege escalation involves detailed enumeration of system configurations, user privileges, and vulnerabilities, including kernel-level attack paths that exploit deep system components.
Windows Privilege Escalation: Advanced Enumeration & Kernel Exploits
Windows systems are prevalent in enterprise environments, making them a prime target for privilege escalation exploits. Attackers focus on identifying misconfigurations, vulnerable services, and kernel flaws to move from a standard user to an administrator level.
Key Enumeration Techniques in Windows
Below are essential enumeration techniques used to gather critical information from Windows systems. Understanding these methods helps identify misconfigurations and potential privilege escalation paths.
1. User Privilege Enumeration: Using tools like PowerView or Laconic to list current privileges, user groups, and account types, identifying misconfigurations such as users belonging to the Administrators or Domain Admins groups.
2. Service Enumeration: Checking for services running with SYSTEM or LOCAL SYSTEM privileges that can be exploited, especially services with weak or known vulnerabilities.
3. Scheduled Tasks and Automated Jobs: Identifying tasks that execute with high privileges, which attackers can manipulate to escalate privileges.
4. System Information Collection: Using commands like systeminfo, wmic, or PowerShell scripts to gather detailed OS version, patch level, and kernel information.
5. Credential Discovery: Extracting cached credentials, hashes, or plaintext credentials using tools like Mimikatz.
Kernel-Level Attack Paths
The following attack paths highlight how weaknesses in kernel components can be leveraged for privilege escalation. Awareness of these risks is essential for hardening system integrity.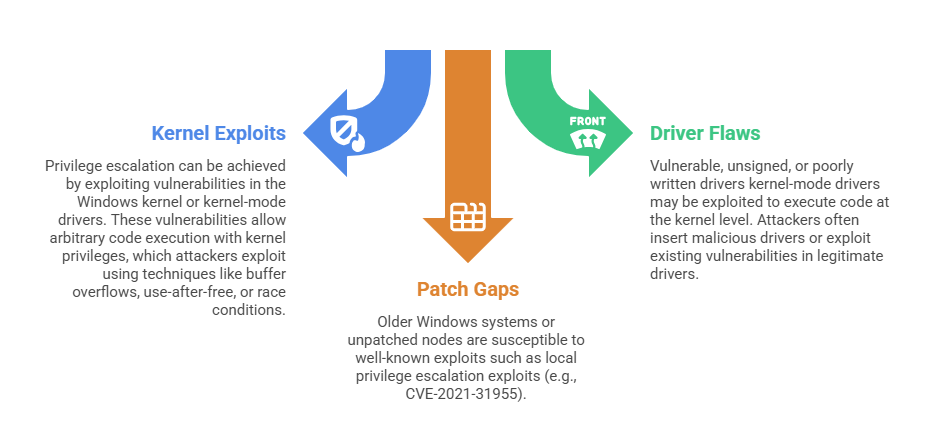
Linux Privilege Escalation: Advanced Enumeration & Kernel Pathways
Linux servers and workstations form the backbone of numerous infrastructures, making privilege escalation on Linux systems equally critical. Attackers leverage misconfigurations, vulnerable services, and kernel flaws to gain root access, enabling full control over the system.
Key Enumeration Techniques in Linux
Outlined below are practical Linux enumeration practices that reveal users, permissions, services, and kernel details. They are crucial for identifying potential escalation paths.
1. User and Group Enumeration: Listing users and groups with commands like id, groups, and cat /etc/passwd or /etc/shadow (if accessible). Identifying users with sudo privileges or weak passwords.
2. Service Enumeration: Checking running services with systemctl or ps, particularly services running as root or with insecure configurations.
3. Kernel Information Gathering: Running uname -a, cat /proc/version, or inspecting loaded modules to identify kernel versions and modules with known vulnerabilities.
4. Configuration Files: Reviewing sudoers (visudo), cron jobs, and startup scripts for misconfigurations that could allow privilege escalation.
5. Weak Permissions and SUID Binaries: Listing SUID/SGID files with find / -perm -4000 -type f -exec ls -la {} \; to find executables that can be exploited for privilege escalation.
Kernel-Level Attack Paths
The attack paths listed here show how kernel bugs, misconfigured SUID binaries, and weak module controls can lead to serious escalation. Evaluating these areas helps uncover foundational security gaps.
1. Kernel Exploits: Kernel bugs, such as buffer overflows or integer overflows, can allow privilege escalation when exploited via specially crafted inputs. Attackers often use known CVEs, like dirty cow (CVE-2016-5195), to escalate.
2. SUID Binaries and Setuid Bugs: SUID ('set user ID') binaries execute with elevated privileges, and vulnerabilities in these can be exploited to gain root access.
3. Kernel Module Loading: Malicious modules can be inserted if module loading is not restricted, providing root-level control.
4. Kernel Patching and Updates: Regular patching is critical, as many exploits target known vulnerabilities in older kernels.
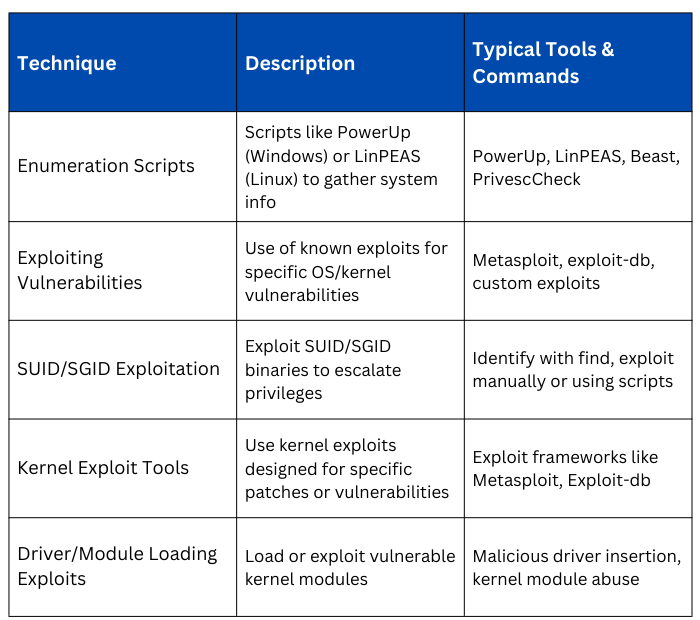
Techniques and Tools for Privilege Escalation
Best Practices for Defenders
1. Keep systems up-to-date with the latest security patches, especially kernel updates.
2. Regularly audit user privileges and restrict SUDO to minimal necessary users.
3. Use endpoint detection and response tools (EDR) to monitor suspicious activities.
4. Employ secure configurations: disable unused services, enforce strong password policies.
5. Harden kernel modules and use kernel parameter security settings.
6. Conduct periodic vulnerability assessments and penetration testing, focusing on privilege escalation vectors.
