Mobile applications on Android and iOS platforms are integral to daily life and business operations but present unique security challenges due to diverse hardware, software environments, and user behaviors.
Securing mobile apps requires understanding their broad attack surfaces, including operating system vulnerabilities, application design flaws, and communication protocols.
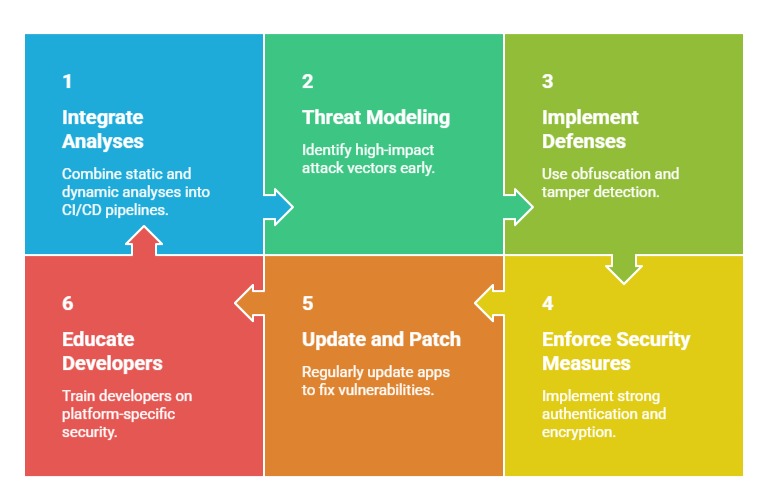
Security testing of mobile apps encompasses static and dynamic analysis techniques aimed at identifying vulnerabilities during development and runtime.
Mobile App Attack Surface: Android & iOS
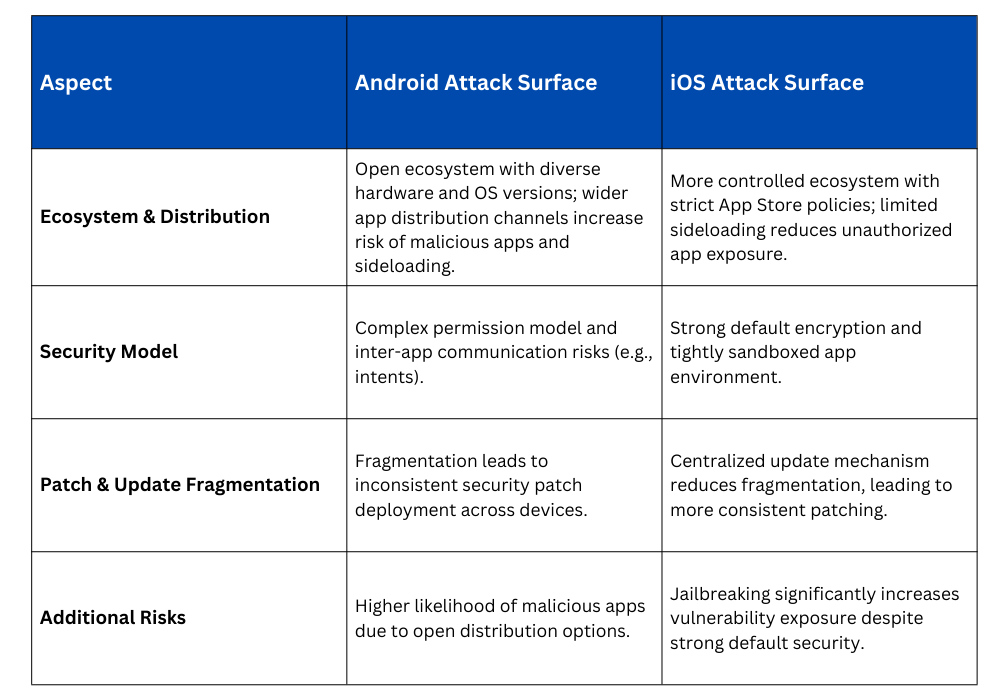
Common Mobile Attack Vectors
1. Insecure data storage (e.g., unencrypted local databases)
2. Inadequate authentication and session management
3. Weak encryption or poor cryptographic implementation
4. Improper platform security control usage (e.g., permissions, keychain)
5. API and backend vulnerabilities exploited via the app
6. Code tampering and reverse engineering
7. Network traffic interception and manipulation
Static Analysis of Mobile Apps
Static testing involves examining the app’s source code, bytecode, or binary without executing it, providing early vulnerability detection opportunities.
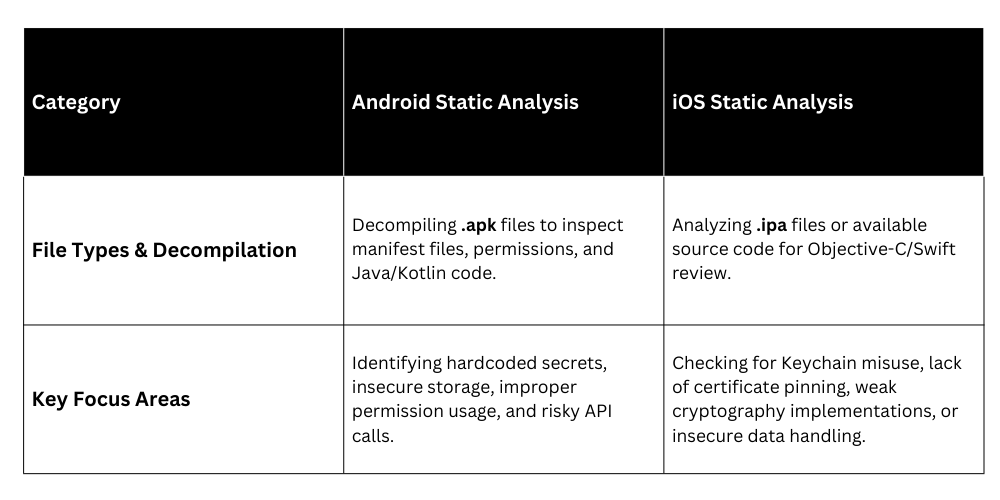
Tools Used:
Android: MobSF, JADX, FindBugs Android
iOS: MobSF, Otool, Hopper Disassembler
Dynamic Analysis of Mobile Apps
Dynamic testing evaluates app behavior during runtime to identify operational vulnerabilities.
Key Focus Areas:
1. Monitoring data flow to detect leakage or insecure transmissions.
2. Intercepting network traffic to assess encryption and API security.
3. Testing authentication flows under various conditions.
4. Exploiting logic errors, session management weaknesses, or input validation failures in live scenarios.
Instrumentation Techniques: The use of debuggers, emulators, and device simulators to closely observe how an application behaves during execution.
Additionally, proxy tools such as Burp Suite and OWASP ZAP are commonly employed to intercept, analyze, and manipulate network traffic, enabling deeper inspection of app communication and potential vulnerabilities.
Tool Examples:
Frida, Xposed Framework (Android runtime manipulation)
LLDB and Proxy Man (iOS dynamic instrumentation)