Data exfiltration refers to the unauthorized or unintentional transfer of data from a trusted environment to an external or untrusted destination. In cybersecurity, it is often associated with malicious activities such as cyberattacks or insider threats.
However, the concept of data exfiltration also applies in non-malicious contexts, such as penetration testing, red teaming, or data migration exercises, where controlled and ethical exfiltration is crucial for assessing organizational security.
Operational Security (OPSEC) considerations revolve around maintaining the confidentiality of the test, minimizing detection, and ensuring that actions do not disrupt normal business functions.
This dual focus on exfiltration methods and OPSEC principles is essential to conducting assessments safely and effectively.
Understanding Data Exfiltration Concepts
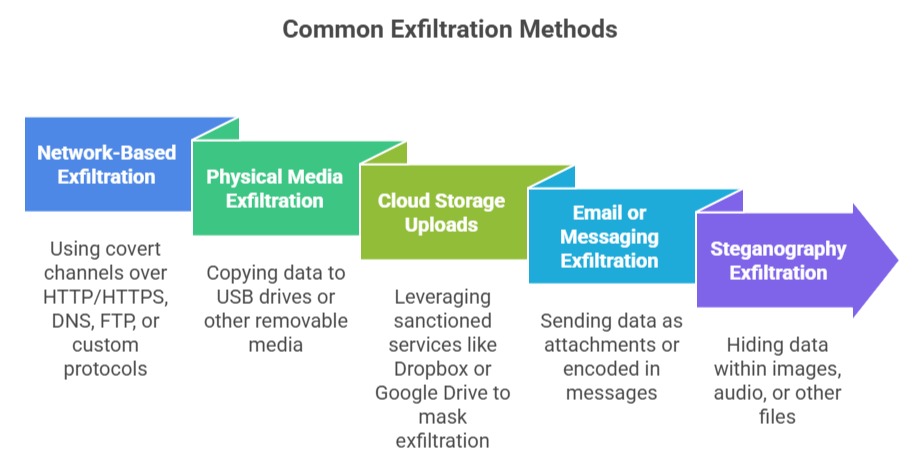
Data exfiltration involves several stages and methods, each with specific challenges and execution tactics.
Stages of Data Exfiltration:
1. Collection: Identifying, locating, and gathering target data within systems or networks.
2. Staging: Preparing data for exfiltration, such as compressing or encrypting to reduce size and avoid detection.
3. Extraction: Transmitting data out via chosen communication channels.
4. Receipt: Successfully receiving and storing exfiltrated data securely.
OPSEC Considerations in Non-Malicious Data Exfiltration
OPSEC (Operational Security) ensures that red teams, penetration testers, or IT administrators maintain confidentiality, avoid alerting defenders prematurely, and minimize operational impact.
1. Planning and Authorization: Clearly define scope, objectives, and permissible data types with stakeholders before exfiltration activities begin.
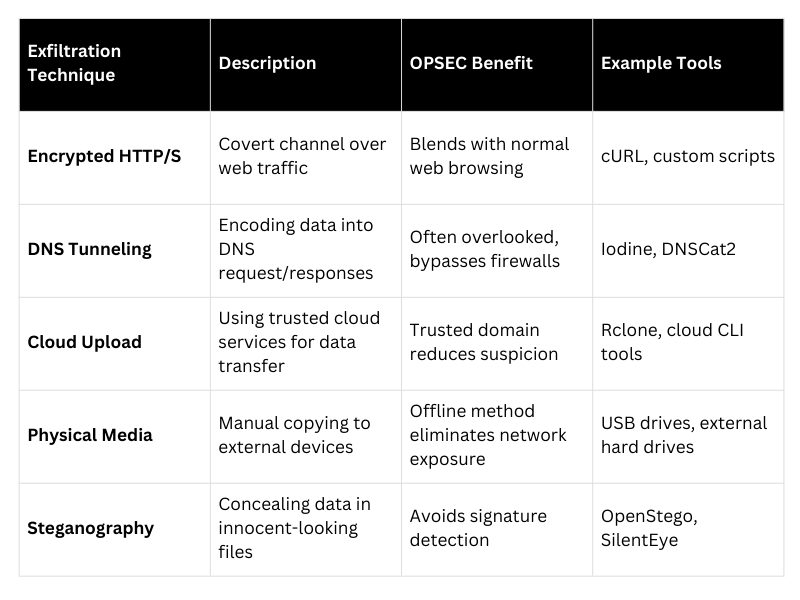
2. Stealth and Cover Channels: Utilize low-and-slow transfer methods or disguise exfiltration within normal traffic to avoid detection by IDS/IPS or SIEM systems.
3. Data Integrity and Confidentiality: Ensure any sensitive or personal data handled during exfiltration complies with privacy regulations and is protected using encryption.
4. Avoiding Disruption: Exfiltration activities should not degrade network performance or system availability.
5. Logging and Evidence Management: Document methods and outcomes meticulously to support reporting and post-assessment reviews while preserving test confidentiality.
Tactical Approaches for Safe Data Exfiltration