VLANs (Virtual Local Area Networks) play a key role in logically segmenting networks to improve performance and security by isolating traffic into different broadcast domains.
Despite being designed to enhance security, VLAN configurations can have inherent weaknesses if not implemented correctly.
Among these vulnerabilities, VLAN hopping is a significant attack vector that allows malicious actors to bypass VLAN isolation and gain unauthorized access to multiple network segments.
Recognizing VLAN hopping risks, understanding port security weaknesses, and conducting thorough network segmentation testing are critical for maintaining robust network defenses.
VLAN Hopping
VLAN hopping enables attackers to send packets to VLANs they are not authorized to access by exploiting weaknesses in switch configurations. The two primary VLAN hopping techniques include:
1. Switch Spoofing: The attacker crafts frames to trick a switch into treating a host port as a trunk port by using protocols like Dynamic Trunking Protocol (DTP). Once the port is treated as a trunk, attackers can send tagged traffic to multiple VLANs, bypassing isolation.
2. Double Tagging: In this method, attackers send packets with two VLAN tags. The first tag matches the attacker’s current VLAN, which is stripped by the first switch making the packet appear as if it belongs to the next VLAN tag, allowing traversal into a different VLAN, provided native VLANs are misconfigured or unsegmented.
Key Misconfigurations Leading to VLAN Hopping
The misconfigurations listed here highlight structural weaknesses in VLAN deployments. Reviewing these problem areas enables more resilient and controlled segmentation.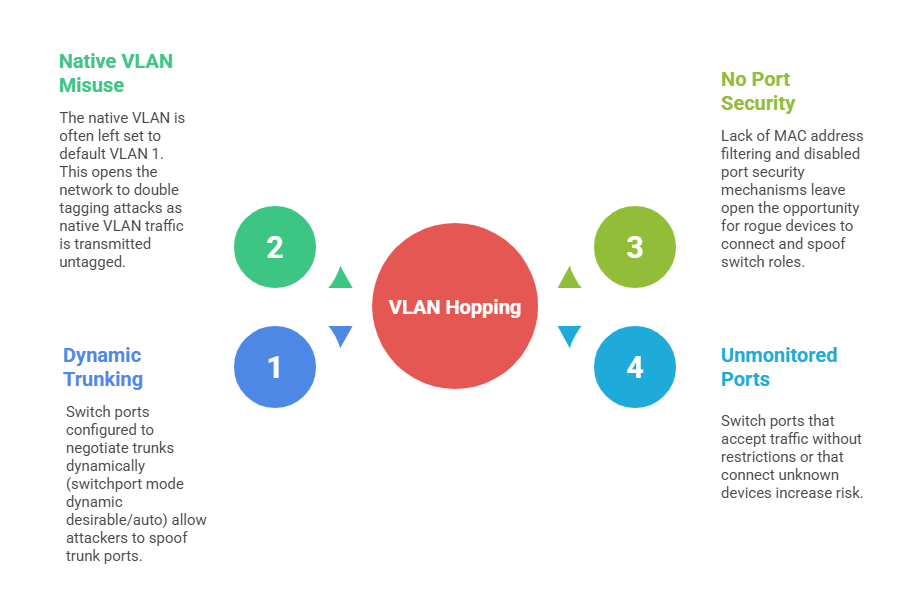
Port Security Weaknesses
Port security mechanisms limit unauthorized access by restricting the number and types of devices that can use a switch port. Common weaknesses include:
1. Disabled Port Security: Without port security, rogue devices can connect unseen.
2. Insufficient MAC Address Limits: Setting limits too high negates the purpose of port security.
3. Failure to Enable Violation Modes: Ports should be set to shut down or restrict traffic when violations occur.
4. No Monitoring or Alerts: Lack of logging means attacks or misconfigurations go unnoticed.
Network Segmentation Testing
Network segmentation separates systems and resources into isolated zones to prevent lateral movement by attackers. Testing segmentation involves:
1. Mapping VLANs and Subnets: Understanding how segmentation is implemented at Layer 2 and Layer 3.
2. Verifying Firewall Rules: Ensuring access control lists (ACLs) restrict traffic appropriately between segments.
3. Simulating VLAN Hopping: Using tools (e.g., yersinia) to attempt switch spoofing and double tagging attacks.
4. Validating Port Security: Testing that ports restrict unauthorized MAC addresses and respond correctly to violations.
5. Assessing Isolation Effectiveness: Checking that critical devices and sensitive data are adequately isolated.
Best Practices to Prevent VLAN Hopping and Secure Segmentation
Presented below are standard practices used to maintain secure VLAN segmentation. They help prevent unauthorized trunking, tagging abuse, and lateral movement.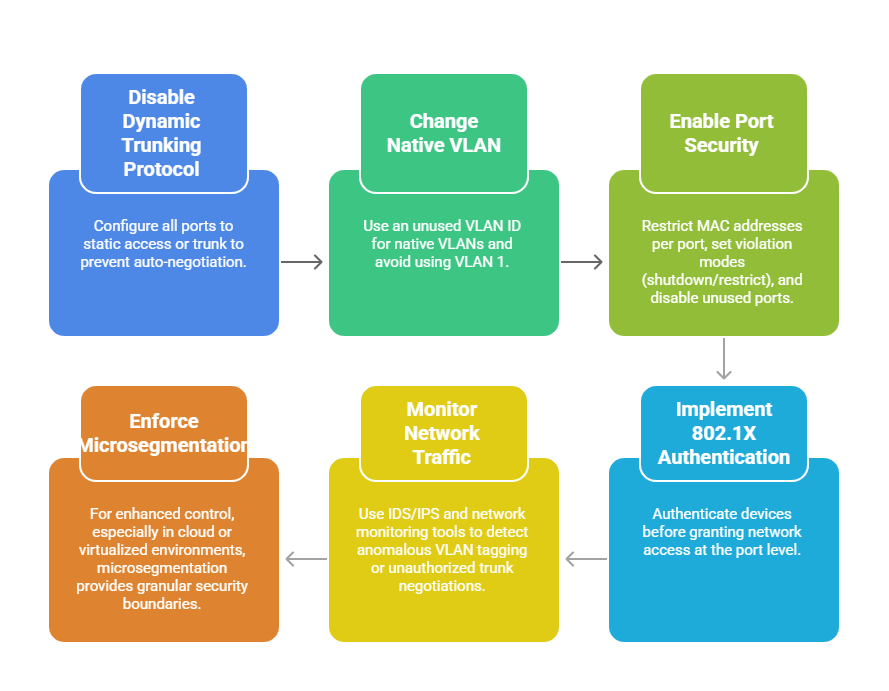
Class Sessions
Sales Campaign

We have a sales campaign on our promoted courses and products. You can purchase 1 products at a discounted price up to 15% discount.
