Pivoting is a fundamental technique used by attackers and penetration testers to extend their reach within multi-layered networks after compromising an initial host.
Multi-layered networks consist of segmented zones controlled by firewalls, VLANs, or other security mechanisms designed to restrict lateral movement.
It allows an attacker to use the compromised system as a stepping stone or proxy to access and control additional devices or systems in otherwise restricted parts of the network.
Understanding the Concept of Pivoting
Pivoting involves leveraging control over one system to route traffic, commands, or exploits to other systems in different network segments not directly accessible from the attacker’s original location.
This process is crucial for gaining deeper access beyond initial footholds, enabling attacks on critical infrastructure, data centers, or segmented zones.
Types of Pivoting
Below are the primary pivoting techniques attackers and testers use to move deeper into restricted network environments. Each method enables traffic redirection through compromised hosts in different ways.

Multi-Layered Networks and Segmentation
Multi-layered networks enforce multiple security boundaries such as external firewalls, internal segmentation firewalls, VLANs, and subnet isolation.
1. They are designed to limit lateral movement by restricting direct access between segments.
2. Common segmentation examples include separating user workstations, servers, and sensitive data stores.
3. Effective segmentation reduces the blast radius of compromises by containing attackers within specific zones.
Pivoting Techniques in Multi-Layered Networks
Here are some commonly used pivoting techniques for operating within multi‑layered enterprise networks. These approaches allow attackers and testers to traverse restricted segments effectively.
1. Local Proxy Pivoting: Tools like ProxyChains, Metasploit’s SOCKS proxy, or Chisel tunnels enable attackers to direct traffic through compromised hosts, creating a local proxy environment to scan and connect within restricted network segments.
2. Remote Port Forwarding: Establishing remote tunnels to forward traffic from an external port to a target internal host port behind firewalls, effectively bypassing access controls.
3. VPN Pivoting: Setting up VPN connections from compromised hosts which provide broader network access as if the attacker was physically inside the network.
4. SSH Pivoting: Using SSH’s local, remote, or dynamic port forwarding to route traffic securely through compromised systems.
5. Double Pivoting and Pivot Chains: Sequentially using multiple compromised hosts in different layers to chain pivots into deeply isolated network zones.
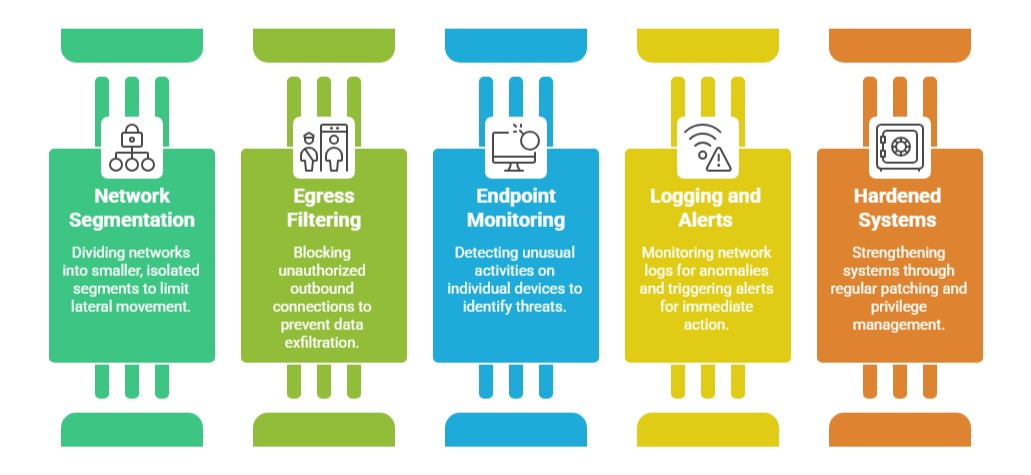
Detecting and Defending Against Pivoting
Outlined below are strategies to defend networks from pivoting attacks and suspicious internal movement. These practices combine access control, monitoring, and alerting mechanisms.