Tunneling and port forwarding are powerful network techniques that enable secure and indirect communication between clients and servers by encapsulating traffic within standardized or encrypted channels.
These mechanisms are widely used for legitimate purposes such as securely accessing remote resources or bypassing network restrictions.
However, they also play a critical role in ethical hacking and penetration testing by allowing attackers or testers to pivot through compromised systems, evade firewalls, and maintain stealthy communication channels.
Common tunneling methods include SOCKS proxies, SSH tunnels, and specialized tools like Chisel, each offering unique capabilities to facilitate flexible and encrypted data transmission.
Understanding Tunneling and Port Forwarding
Tunneling refers to encapsulating one network protocol within another, allowing data to be securely transmitted across incompatible or restricted networks. The tunnel acts as a secure pathway, often encrypting traffic and hiding its true destination.
Port forwarding redirects network traffic from one IP address and port to another, often used to expose services behind firewalls or NATs or to create proxy connections through intermediate hosts.
SOCKS Proxy: Versatile Traffic Forwarding
SOCKS (Socket Secure) is an internet protocol that routes network packets between client and server through a proxy server.
Functionality: Operates at layer 5 (session layer) and proxies TCP and UDP traffic, allowing clients to use it without knowledge of the proxy.
Use Cases in Ethical Hacking
1. Redirecting attacker’s tools or browsers through compromised systems.
2. Bypassing firewall restrictions by relaying traffic through SOCKS proxy chains.
3. Enabling multi-protocol tunneling since SOCKS supports any kind of traffic.
Implementation: Common implementations include Dante on Linux or SOCKS proxies through SSH (ssh -D).
SSH Tunnels: Secure Encrypted Channels
SSH (Secure Shell) tunnels use the SSH protocol to securely forward traffic between hosts.
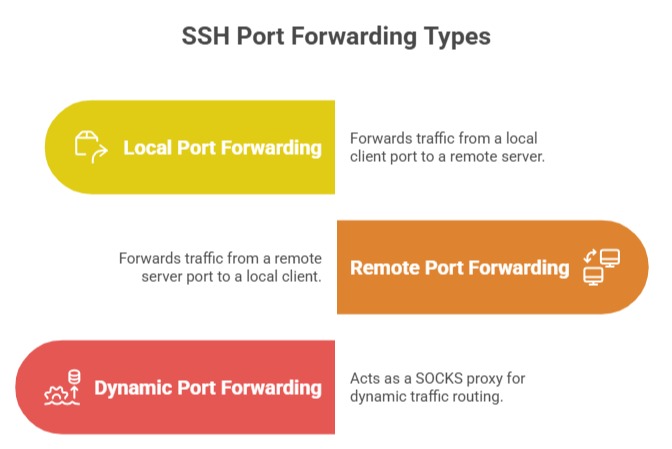
Benefits: Strong encryption that protects data as it travels across networks, ensuring confidentiality and integrity. It can also bypass firewalls by routing traffic through standard SSH ports, typically port 22, allowing secure access even in restricted environments.
Additionally, SSH supports flexible authentication methods and multiple tunnel configurations, making it a versatile solution for secure connectivity.
Usage Examples
1. Accessing internal company resources securely from outside the network.
2. Facilitating stealthy command and control communication for penetration testers.
Chisel: Lightweight TCP/UDP Tunnel
Chisel is a fast TCP/UDP tunnel over HTTP, designed for use in restricted and monitored environments.
Key Features
1. Cross-platform support (Windows, Linux, macOS).
2. Operates over HTTP traffic to bypass network restrictions.
3. Simple client-server architecture for rapid setup.
4. Supports UDP tunneling alongside TCP.
Typical Use Cases: Quickly deploying tunnels in environments where SSH is blocked or unavailable, allowing secure communication despite restrictions.
These tunnels are also useful for pivoting within networks that enforce strict egress controls, enabling deeper internal access.
Additionally, they support port forwarding and proxying, making them valuable tools during penetration testing operations for routing traffic securely and efficiently.
Basic Operation: The chisel client connects to a chisel server running within a target network, forwarding ports and enabling remote access through an HTTP tunnel.
Best Practices and Considerations
1. Security: Always use encrypted tunnels (e.g., SSH) to protect sensitive data.
2. Authentication: Employ strong authentication mechanisms to prevent unauthorized access.
3. Monitoring: Detect and restrict unauthorized tunnels using network monitoring and firewall rules.
4. Stealth: For ethical hacking, tunnels allow stealthy lateral movement without triggering alerts.
5. Performance: Consider latency and bandwidth overhead introduced by tunneling.
