Exploit development is a cornerstone skill in cybersecurity, enabling professionals to understand and demonstrate how vulnerabilities in software can be manipulated to execute arbitrary code or gain unauthorized access.
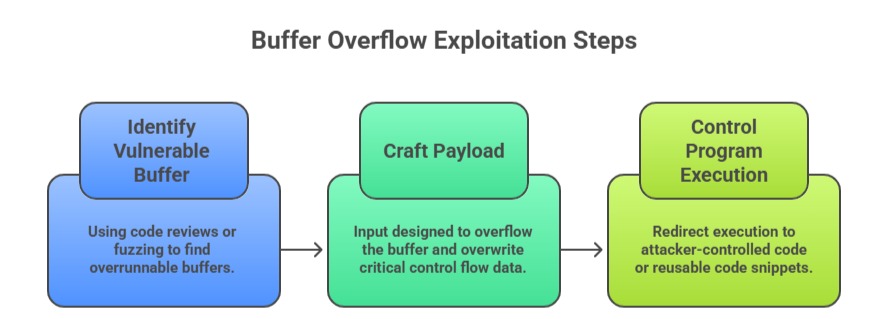
Two fundamental concepts in exploit development are buffer overflow attacks and shellcode development. Buffer overflows occur when a program writes more data to a buffer than it can hold, overwriting adjacent memory and potentially redirecting control flow.
Shellcode is the payload code executed after successful exploitation, often granting control over the compromised system.
Buffer Overflow Fundamentals
A buffer overflow happens when a program writes data beyond the boundaries of pre-allocated fixed-size memory buffers. This leads to memory corruption, which attackers exploit to overwrite control data structures like program counters or return addresses.
Key Concepts:
1. Stack Buffer Overflow: Overflows buffers located in the stack frame of a function, potentially overwriting the return address on the call stack.
2. Heap Buffer Overflow: Overflows buffers allocated in the heap area, affecting dynamic memory and object metadata.
3. Off-by-One Errors: Circumvent protections by writing one byte beyond buffer limits.
4. Return-Oriented Programming (ROP): Technique to bypass modern mitigations by chaining small code snippets ("gadgets") instead of injecting code.
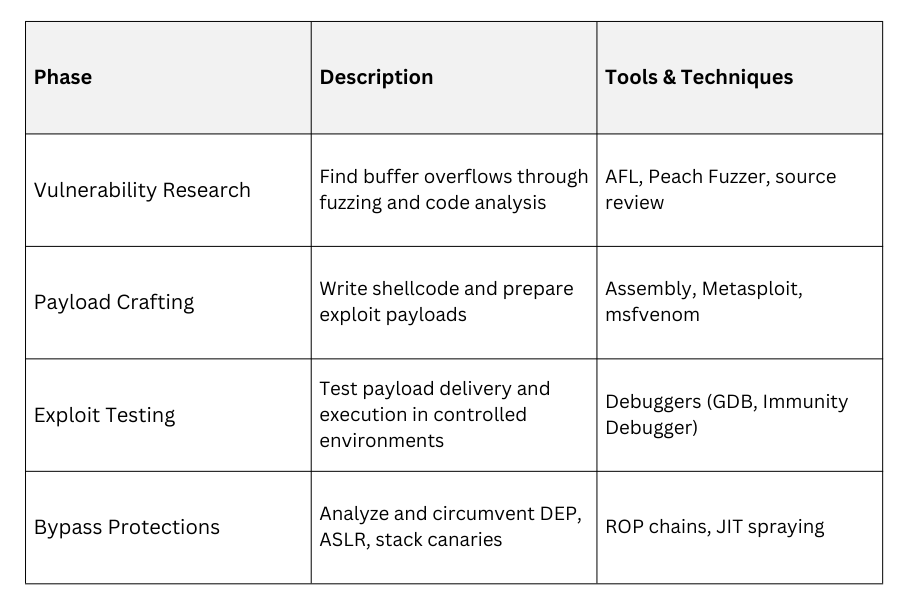
Protections Against Buffer Overflows: The use of stack canaries or guard values, which detect memory overwrites before a function returns and helps prevent stack-based attacks.
Data Execution Prevention (DEP) strengthens security by marking certain memory regions as non-executable, blocking injected code from running.
Additionally, Address Space Layout Randomization (ASLR) introduces randomness to memory layout, making it significantly harder for attackers to predict memory addresses and craft reliable exploits.
Shellcode Basics
Shellcode is a small piece of executable machine code used as the payload in software exploits. The term originates from early examples where code opened a shell, granting command-line access, but modern shellcode performs a variety of malicious tasks.
Types of Shellcode:
1. Bind Shell: Opens a network port, allowing an attacker to connect and control the system.
2. Reverse Shell: Connects back to the attacker's system, bypassing inbound firewall rules.
3. Download & Execute: Fetches and runs additional malware.
4. Staged & Stageless Shellcode: Staged shellcode downloads payloads in parts; stageless contains all payloads at once.
Shellcode Development Principles:
1. Must be small and position-independent.
2. Avoids null bytes or bad characters that break exploit input processing.
3. Employs system calls directly to interact with the OS.
Common Shellcode Tools:
1. Metasploit Framework: Generates diverse shellcode types.
2. msfvenom: Standalone payload generator.
3. Manual assembly coding for custom payloads.
Exploit Development Workflow
Class Sessions
Sales Campaign

We have a sales campaign on our promoted courses and products. You can purchase 1 products at a discounted price up to 15% discount.
