Misconfigurations and improper file or service permissions are common vulnerabilities that significantly weaken the security posture of both Windows and Linux systems.
Attackers leverage these weaknesses to gain unauthorized access, escalate privileges, or persist within target environments.
Exploiting misconfigurations involves identifying incorrectly set parameters, default settings, or insecure services that expose critical data or control.
File and service permission abuse relates to exploiting overly permissive access rights, enabling attackers to modify, execute, or access sensitive files and services beyond their legitimate scope.
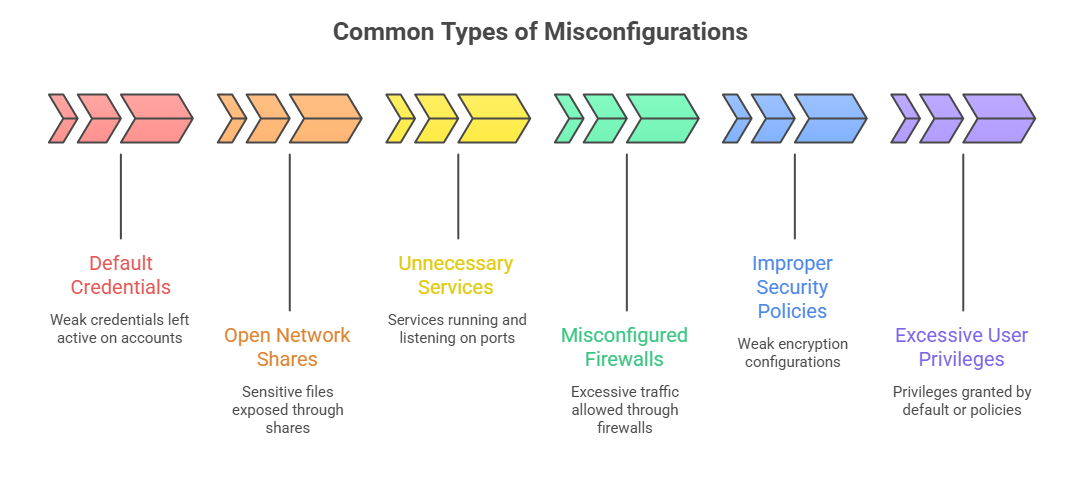
Misconfigurations: The Hidden Threats
Misconfigurations arise when systems, services, or applications are set up without proper security considerations, either due to oversight, complexity, or inadequate policies.
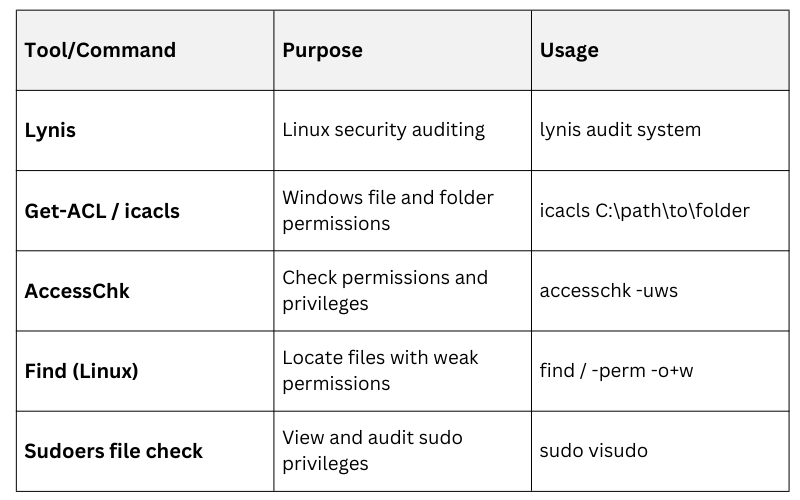
Detection & Enumeration: Security testers employ configuration auditing tools (e.g., Lynis for Linux, Microsoft Baseline Security Analyzer for Windows) and manual inspection to identify deviations from best practices or standards.
File and Service Permission Abuse
File and service permission abuse targets systems where access control mechanisms are weak, allowing users or attackers to perform unauthorized actions.
1. File Permissions Abuse
Files or directories with world-writable permissions can be modified or replaced with malicious content.
Sensitive configuration files exposed to non-privileged users enable them to extract secrets or change system behavior.
Backup files or logs left accessible can leak confidential information.
2. Service Permissions Abuse
Services running with elevated privileges may be exploited through configuration flaws or injection vulnerabilities.
Executable files owned or writable by low-privilege users lead to privilege escalation via code replacement.
Misconfigured sudo privileges allowing unintended command execution.
Examples of Exploitation Techniques
The following examples show how exploitation often stems from overlooked configuration issues. Understanding these actions provides insight into preventing escalation and unauthorized persistence.
1. Exploiting Weak File Permissions: Attackers modify scripts or configuration files with weak permissions to inject malicious commands executed by privileged processes.
2. Service Hijacking: Restarting or replacing service executables that are owned or writable by non-admin users to run arbitrary code with elevated rights.
3. Scheduled Task Manipulation: Changing task configurations or scripts that run with high privileges.
4. Configuration Injection: Altering files with critical configuration details (e.g., SSH authorized_keys) to gain persistent access.
Tools & Commands for Detection
Mitigation and Best Practices
Here is a list of recommended steps to secure systems and prevent privilege misuse. These practices help ensure proper permissions, updates, and monitoring.
1. Least Privilege Principle: Grant users and services the minimal permissions required for their role.
2. Regular Audits: Perform periodic configuration and permission reviews to detect drift from security baselines.
3. Secure Defaults: Change default passwords and disable unnecessary services.
4. File Integrity Monitoring: Implement systems to alert on unauthorized permission changes or file modifications.
5. Segmentation of Duties: Separate critical functions and permissions among different users to limit damage.
6. Patch Management: Keep systems and services updated to reduce exploitation of known configuration vulnerabilities.
Class Sessions
Sales Campaign

We have a sales campaign on our promoted courses and products. You can purchase 1 products at a discounted price up to 15% discount.
