In cybersecurity defense, the primary goal for Blue Teams (defenders) is to detect, prevent, and respond to malicious activities.
However, adversaries often attempt to evade detection through various techniques, which include operational security (OPSEC) measures and log evasion tactics.
While offensive tactics focus on concealment, Blue Team operators must also understand these evasion strategies to improve detection, strengthen defenses, and maintain operational integrity.
OPSEC in Cyber Defense
Operational Security (OPSEC) in cybersecurity refers to deliberate measures taken to conceal operational details, attack strategies, or vulnerabilities from adversaries, thereby reducing the risk of detection and exploitation.
Why OPSEC Matters for Blue Teams: It prevents adversaries from gathering intelligence about defensive measures, detection mechanisms, and potential gaps that could be exploited.
It also safeguards sensitive information related to security protocols, internal logs, and incident response plans.
By protecting these details, organizations maintain a strategic advantage against advanced persistent threats (APTs) and reduce the likelihood of targeted attacks.
Key OPSEC Strategies for Defense:
1. Limit Exposure: Only share information within the organization on a need-to-know basis.
2. Minimize Attack Surface: Secure endpoints, services, and network segments to reduce available targets.
3. Obfuscate Detection Signatures: Regularly update signatures, patterns, and behaviors to prevent attackers from identifying detection signatures.
4. Secure Communications: Use encrypted channels and strong authentication practices internally.
Log Evasion Principles
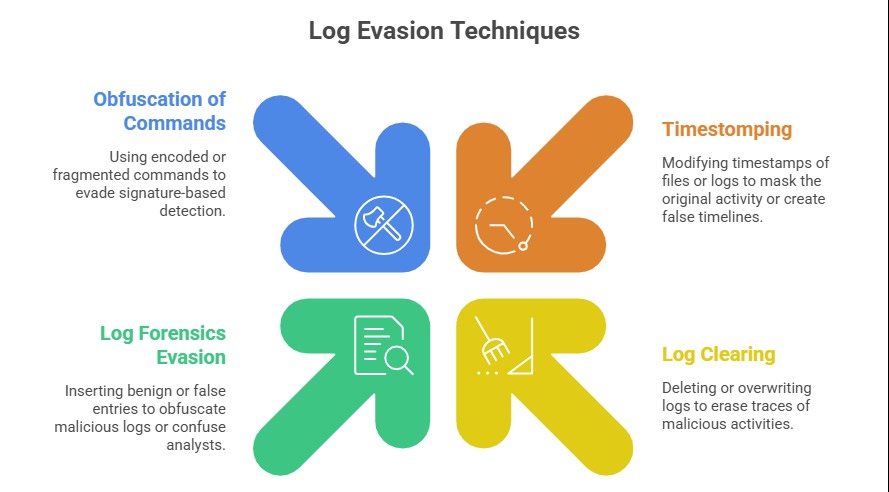
Attackers aiming to remain undetected try to evade detection by hiding activity, manipulating logs, or generating stealthy footprints that bypass security monitoring.
Counteracting Log Evasion
1. Centralized Logging: Use log aggregation and forwarding (e.g., SIEM solutions) to detect tampering or deletions.
2. Immutable Log Storage: Implement write-once-read-many (WORM) storage or append-only logs to prevent alteration.
3. Regular Validation: Periodically verify log integrity using checksums, hashes, or digital signatures.
4. Anomaly Detection: Use behavioral analytics and machine learning to flag unusual activity patterns, even if internal logs are tampered.
Advanced OPSEC and Log Evasion Tactics
Attackers continue to evolve their OPSEC and log evasion methods to remain undetected. Below are the primary techniques used to hide malicious footprints across systems and monitoring tools.
1. Encrypted Logs: Attackers may try to decrypt logs or exfiltrate encrypted logs for later decryption outside the environment.
2. Encrypted Channels: Use covert channels or obfuscate log data sent over encrypted channels to hinder inspection.
3. Splitting Activity: Spread malicious actions across different time frames or systems to avoid creating distinct, suspicious patterns.
4. Tampering with System Integrity: Alter or disable Security Information and Event Management (SIEM) rules to mask detection triggers.
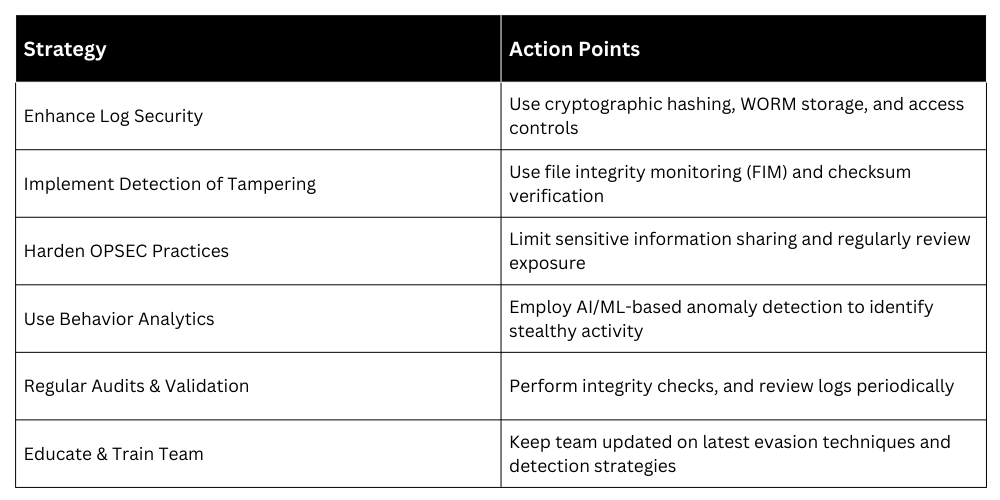
Best Practices for Blue Teams to Counter Evasion