Social engineering campaigns simulate real-world psychological manipulation techniques that attackers use to deceive people into divulging confidential information or performing actions that compromise security.
Ethical social engineering campaigns serve as controlled exercises designed to test and improve an organization’s human security defenses by mimicking adversary tactics.
Planning these campaigns requires careful consideration of legal, ethical, and organizational boundaries to ensure respect, privacy, and safety.
Successful social engineering campaigns provide valuable insights into vulnerabilities in security awareness while promoting a culture of vigilance through realistic training and feedback.
Foundations of Social Engineering Campaign Planning
Effective social engineering campaigns rely on thoughtful planning and ethical execution. The following foundational elements ensure the process remains safe, compliant, and aligned with organizational objectives.
1. Define Clear Objectives: Establish the scope and goals—whether to test phishing susceptibility, physical access controls, or phone-based attacks.
2. Stakeholder Engagement: Secure buy-in from organizational leadership, legal, HR, and IT teams to ensure compliance and coordinated response management.
3. Ethical Boundaries:
Respect employee privacy and dignity—avoid harassment or coercion.
Avoid sensitive scenarios causing undue stress or harm.
Ensure transparent policies about social engineering assessments exist.
Protect personal and sensitive data collected during the campaign.
4. Compliance and Legal Considerations
Adhere to data protection laws (e.g., GDPR, HIPAA).
Obtain documented consent where applicable.
Follow contractual or regulatory requirements.
Designing Social Engineering Simulations
To design strong social engineering simulations, organizations must consider multiple dimensions such as scenario realism, target profiling, and timing. The points below outline the core steps involved.
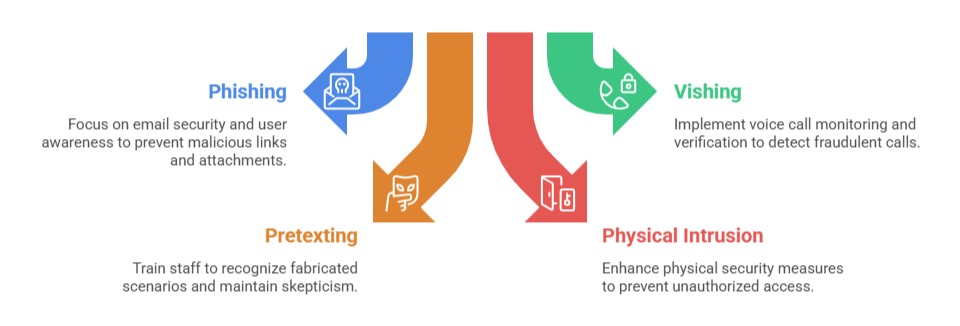
1. Attack Vector Selection
2. Target Profiling: Customize campaign content based on employee roles and potential exposure. Tailored messages increase realism and effectiveness.
3. Crafting Realistic Scenarios: Use believable narratives, appropriate branding, and contextual details consistent with organizational communication style.
4. Channel and Timing: Choose communication channels widely used internally (email, intranet, phone) and time campaigns to avoid busy periods or sensitive events.
Measuring and Reporting Outcomes
Effective outcome measurement requires tracking meaningful metrics, gathering feedback, and applying lessons learned. The points below outline the essential steps for reporting results and strengthening future campaigns.
1. Metrics to Track
Engagement rates (clicks, responses).
Data disclosure incidents.
Physical access violations.
User reports of suspicious activity.
2. Post-Campaign Feedback
It involves immediately notifying and educating participants who fall for the simulation, ensuring they understand the mistakes made and how to avoid them in the future.
It also includes organization-wide training based on commonly observed weaknesses to strengthen overall awareness. Additionally, it reinforces reporting mechanisms and security policies, helping employees confidently recognize and respond to potential threats.
3. Continual Improvement: Incorporate lessons learned into future campaigns and broader awareness strategies.
