Containers and orchestration platforms like Kubernetes have transformed how organizations deploy, scale, and manage applications in cloud and on-premises environments.
While containers offer portability, efficiency, and consistency, they also introduce unique security challenges.
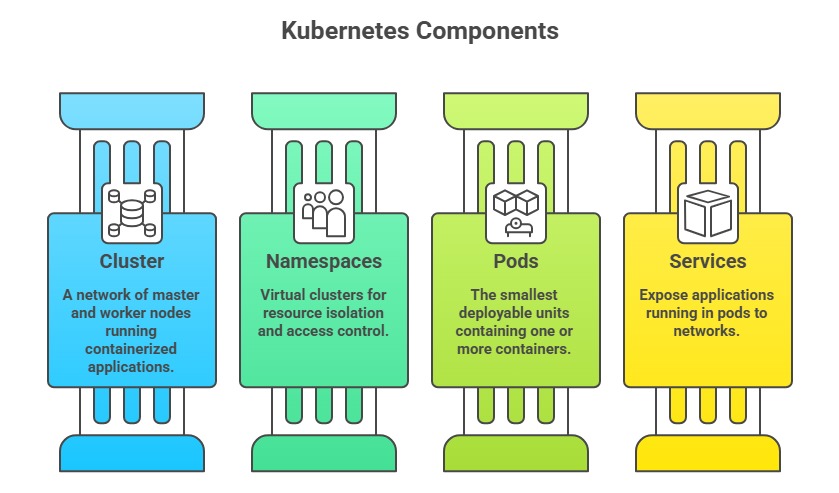
Kubernetes, the most popular container orchestration platform, adds complexity through its multi-layered architecture involving clusters, nodes, pods, and services.
Security vulnerabilities in containers and Kubernetes often stem from misconfigurations, inadequate isolation, privilege escalation opportunities, and weak access controls.
Container Security Fundamentals
Containers are lightweight, standalone packages containing application code, runtime, libraries, and dependencies, enabling consistent execution across different computing environments.
Common Container Security Risks:
1. Vulnerable Base Images: Using outdated or unpatched base images containing known vulnerabilities.
2. Insecure Container Runtime: Misconfigured runtime settings allowing privilege escalation or breakout to the host system.
3. Exposed Secrets: Hardcoding credentials, API keys, or certificates in container images or environment variables.
4. Weak Network Isolation: Lack of proper network segmentation between containers, allowing lateral movement.
5. Insufficient Monitoring: Absence of logging and runtime security monitoring to detect malicious activities.
Container Security Best Practices:
1. Use minimal, trusted base images from verified sources.
2. Scan images for vulnerabilities regularly using tools like Trivy, Clair, or Anchore.
3. Avoid running containers as root; use non-privileged users.
4. Implement secrets management solutions (HashiCorp Vault, Kubernetes Secrets with encryption).
5. Apply resource limits and quotas to prevent resource exhaustion attacks.
Kubernetes Security Architecture
Kubernetes orchestrates containers across clusters of nodes, introducing additional security considerations at cluster, namespace, pod, and network levels.
Namespace Isolation and Security
Namespaces provide logical separation of resources within a Kubernetes cluster, enabling multi-tenancy and access control.
Security Benefits of Namespaces: They allow workloads from different teams, projects, or environments to be isolated, reducing the risk of accidental or malicious interference.
Namespaces also enable the application of role-based access control (RBAC) policies on a per-namespace basis, ensuring that users and services only have the permissions they require.
Additionally, they support enforcement of resource quotas and limit ranges, preventing any single workload from monopolizing cluster resources and maintaining overall system stability.
Common Namespace Misconfigurations:
1. Lack of Network Policies: Allowing unrestricted communication between namespaces.
2. Overly Permissive RBAC: Granting excessive permissions across namespaces.
3. Weak Resource Limits: Not enforcing quotas, leading to denial-of-service risks.
Best Practices:
1. Create separate namespaces for production, staging, and development environments.
2. Implement NetworkPolicies to control traffic flow between namespaces.
3. Apply least privilege RBAC rules specific to each namespace.
4. Define and enforce resource quotas and limit ranges.
Privilege Escalation in Kubernetes
Privilege escalation occurs when attackers exploit misconfigurations or vulnerabilities to gain elevated access within a cluster.
Common Privilege Escalation Vectors:
1. Privileged Pods: Pods running with elevated privileges (privileged: true) can access host resources and escape container isolation.
2. Host Path Mounts: Mounting host directories into containers allows access to sensitive host files and configurations.
3. Excessive RBAC Permissions: Service accounts with cluster-admin or excessive permissions enable attackers to control the entire cluster.
4. Kubernetes API Exploitation: Misconfigured API server access allows unauthorized users to create, modify, or delete resources.
5. Container Breakout: Exploiting vulnerabilities in container runtime (Docker, containerd) to escape to the host system.
Mitigation Strategies
Focus on reducing privilege, tightening access controls, and enforcing strong security baselines. Privileged containers should be avoided unless absolutely necessary, as they pose significant risks by granting extensive host-level access.
Host path mounts must be restricted, with safer alternatives such as ConfigMaps and Secrets used to store configuration and sensitive data.
Strict RBAC policies should be implemented following the principle of least privilege to ensure users and services only access what they truly need.
The Kubernetes API server must also be secured with robust authentication, authorization, and TLS encryption to protect cluster communication.
Additionally, enforcing Pod Security Policies (PSPs) or Pod Security Standards helps maintain consistent security baselines and reduce exposure to misconfigurations or unsafe workloads.
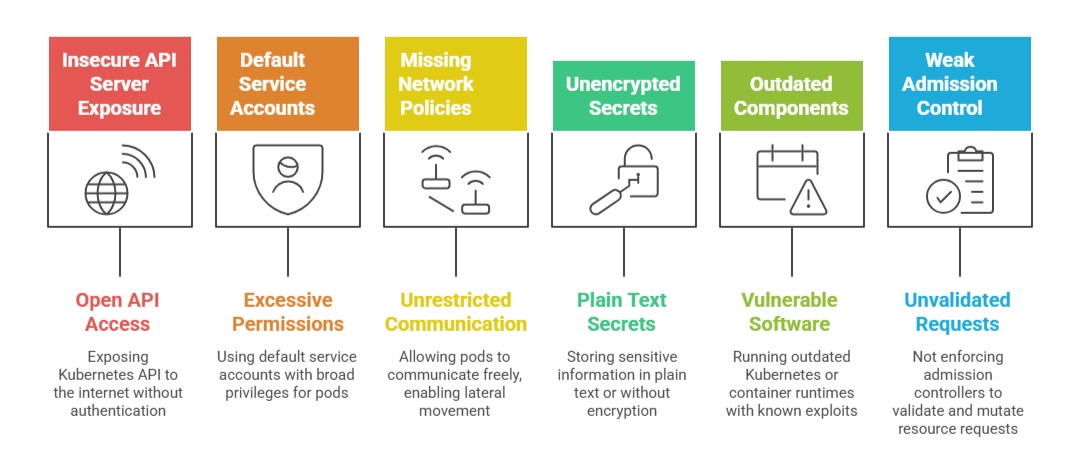
Common Kubernetes Misconfigurations
Many Kubernetes security gaps arise from simple configuration oversights. Here is a list of common pitfalls that can compromise cluster integrity.