Real-time incident response is critical in today’s rapidly evolving cyber threat landscape where timely detection, analysis, and mitigation of security incidents can significantly reduce damage and operational disruption.
Traditional incident response relies heavily on human expertise, manual processes, and static playbooks, which may delay decision-making and action during high-pressure security events.
Artificial Intelligence (AI) offers transformative potential to enhance real-time incident response by providing intelligent, data-driven recommendations that guide analysts through complex investigations and dynamic threat environments efficiently and accurately.
AI systems analyze security data streams, correlate events, and apply learned knowledge to suggest next best actions, accelerating response times and improving defense postures.
AI Techniques for Real-Time Incident Response Recommendations
The techniques outlined below demonstrate how AI assists in active incident management. They integrate detection, orchestration, and recommendation capabilities to accelerate response.
1. Data Aggregation and Correlation: AI ingests and consolidates logs, alerts, threat intelligence, and contextual information from varied sources to create a comprehensive incident picture.
2. Anomaly and Threat Detection: Machine learning models detect suspicious activities and classify incidents based on severity and type, triggering timely response workflows.
3. Decision Support Systems: AI-driven recommendation engines provide analysts with prioritized response actions based on incident context, attack type, and organizational policies.
4. Automated Playbooks and Orchestration: Integration with Security Orchestration, Automation and Response (SOAR) platforms enables AI to execute or suggest automated remediation steps while allowing human oversight.
5. Predictive Analytics: AI forecasts potential incident impacts, attack progression, and propagation, helping teams prepare and mitigate proactively.
6. Natural Language Processing (NLP): Assists in interpreting complex security data and generating easy-to-understand recommendations and reports for analysts.
These techniques collectively support dynamic, informed, and accelerated decision-making in active incident scenarios.
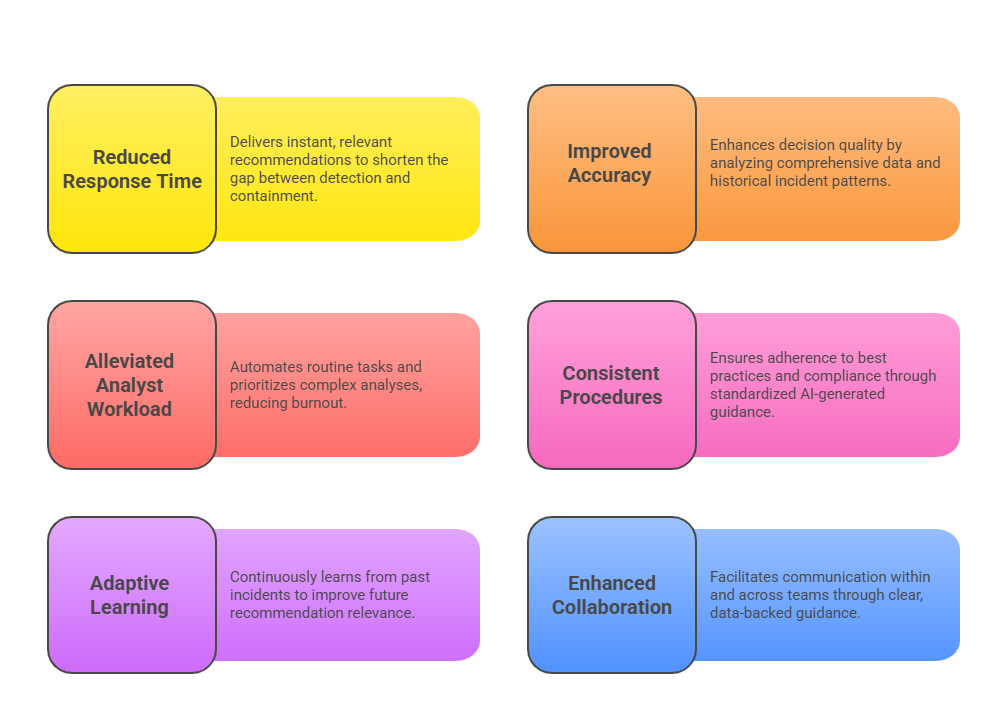
Benefits of AI-Driven Real-Time Incident Response
Below are notable gains organizations achieve by implementing AI for incident response. These include faster containment, reduced human error, and continuous learning for evolving threats.
Challenges in AI-Enabled Incident Response
Implementing AI in incident response presents several challenges that organizations must address. Below are key obstacles and considerations for effective, trustworthy deployment.
1. Trust and Explainability: Analysts require transparent reasoning behind AI recommendations to trust and act upon them confidently.
2. Data Privacy and Security: Ensuring sensitive incident data is securely processed within AI systems.
3. Integration Complexity: Seamless interoperability with existing SIEM, SOAR, and IT infrastructure is essential.
4. Handling Novel Threats: AI models must adapt rapidly to emerging attack techniques and zero-day threats.
5. Human Oversight: Maintaining a balance between automation and human judgment for ethical and effective incident management.
