Automated scenario simulation and behavioral analysis represent advanced methodologies in cybersecurity used to mimic real-world attack scenarios and evaluate system responses. These techniques leverage artificial intelligence (AI) and machine learning to model adversary behavior continuously and at scale, providing organizations with deeper insights into potential vulnerabilities and defense effectiveness.
Scenario simulation automates the creation and execution of attack sequences based on threat intelligence, while behavioral analysis monitors system and user activities to detect deviations indicative of security incidents. Integrating these approaches helps cybersecurity teams proactively identify risks, validate controls, and improve incident response strategies.
Automated Scenario Simulation: Emulating Real-World Attacks
Automated scenario simulation involves creating repeatable, realistic attack simulations that replicate adversary techniques to test cybersecurity postures:
1. Attack Path Modeling: AI generates multi-step attack scenarios by chaining known tactics and techniques, such as those documented in MITRE ATT&CK, reflecting real adversary behavior.
2. Threat Intelligence Integration: Scenario parameters adapt dynamically based on current threat landscape data, tailoring simulations to the organization’s risk context.
3. Red Teaming at Scale: Automated red teaming tools emulate attacker behaviors without manual intervention, enabling frequent and comprehensive testing.
4. Penetration Testing Augmentation: Scenarios simulate exploits, lateral movement, privilege escalation, and data exfiltration paths.
5. Scenario Diversity: Varies attack vectors, entry points, and payloads to uncover diverse vulnerabilities.
This automation enhances the scope, repeatability, and coverage of traditional security assessments.
Behavioral Analysis: Monitoring and Interpreting Activity Patterns
Behavioral analysis focuses on understanding typical user, device, and system behaviors to detect anomalies or threatening activities:
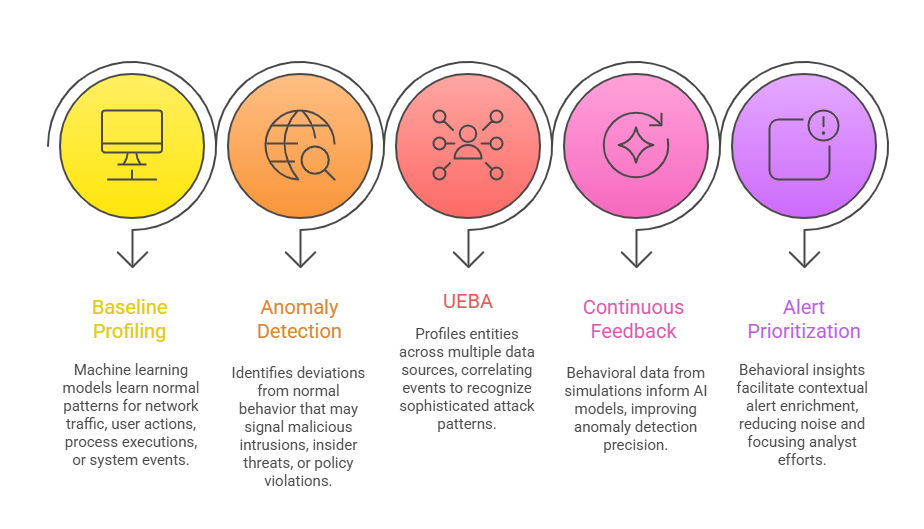
Combining behavioral analysis with scenario simulation creates a powerful feedback mechanism to refine threat understanding.
Benefits of Automated Scenario Simulation and Behavioral Analysis
Outlined below are the major benefits of using automated attack simulations and behavioral models. Together, they enable more realistic testing and scalable threat identification.
1. Proactive Risk Identification: Simulates attacks before adversaries act, identifying weak points in defenses.
2. Realistic Validation: Tests controls against complex, multi-step attack paths reflective of actual threats.
3. Enhanced Detection: Behavioral models improve visibility into subtle or unknown malicious activities.
4. Efficiency and Scalability: Automation allows frequent, wide-ranging security assessments.
5. Improved Incident Response: Contextual behavioral data accelerates threat hunting and forensic investigations.
6. Integration with SIEM and SOAR: Enriches security orchestration with actionable insights.
Challenges and Considerations
The list below highlights essential challenges that organizations must navigate to achieve accurate and scalable behavioral analytics. These considerations reflect both technical and operational dependencies.

