In cybersecurity and IT operations, identifying the root cause of an incident swiftly and accurately is crucial for effective remediation and prevention. Traditional approaches often involve manual analysis, which can be time-consuming, error-prone, and limited in scope, especially in complex environments with vast amounts of data.
Automated root cause identification leverages advances in artificial intelligence (AI) and machine learning (ML) to streamline this process by analyzing large volumes of system logs, network traffic, configurations, and event data to pinpoint the underlying source of issues quickly and reliably.
This automation not only accelerates incident response but also enhances diagnostic accuracy, reducing downtime and operational costs.
Understanding the Need for Automation in Root Cause Analysis
In complex IT systems, incidents often manifest through multiple, seemingly unrelated symptoms across different systems and layers. Traditional manual analysis involves tracing logs, configurations, and alerts, which can be exceedingly difficult: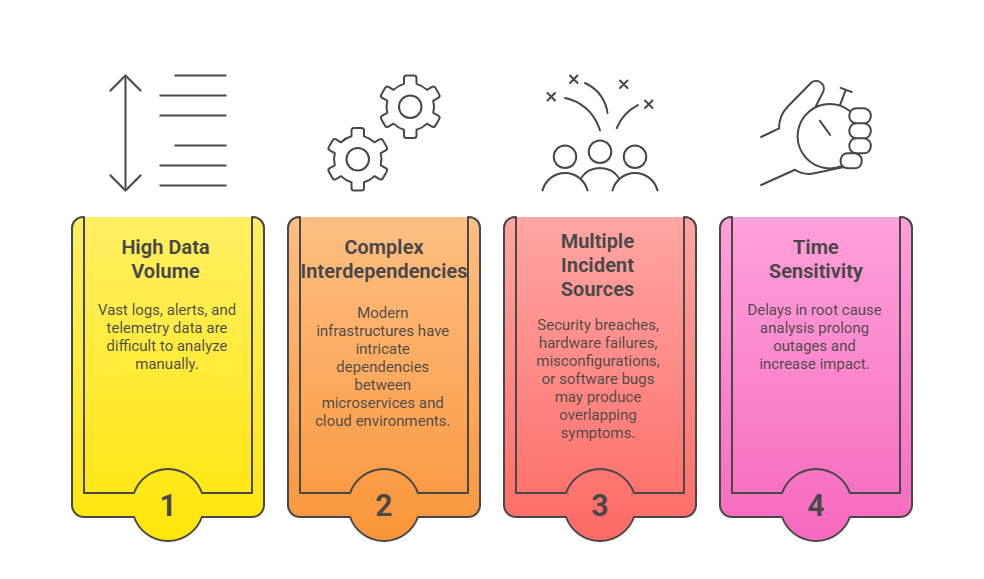
AI-based automation offers a scalable solution capable of handling these complexities efficiently.
Methods and Technologies in Automated Root Cause Identification
These are the key approaches used in modern automated RCA solutions. Together, they enable rapid detection of causal paths and system failures through advanced analytics.
1. Data Collection and Integration: Aggregating logs, network flows, application traces, and configuration data from disparate sources.
2. Pattern Recognition and Correlation: Machine learning models analyze data streams to identify patterns, anomalies, and relationships indicating potential root causes.
3. Causal Inference Models: Using probabilistic reasoning and causal analysis techniques to determine the most likely source of the incident.
4. Anomaly Detection: Highlighting unusual behavior or deviations from normal system patterns that may point to underlying issues.
5. Sequence and Dependency Analysis: Tracing the sequence of events and dependencies to pinpoint the initial trigger that set off the incident chain.
6. Knowledge Graphs and Visualization: Mapping causal relationships and system components to visualize and interpret root causes.
The integration of these techniques enables fast, accurate, and automated analysis of complex incident data.
Benefits of Automated Root Cause Identification
The following points summarize how automated root cause detection transforms incident management. It ensures rapid, precise, and scalable problem-solving across complex systems.
1. Speed: Reduces time-to-resolution by rapidly pinpointing the underlying issue, minimizing system downtime.
2. Accuracy: Employs ML and causal inference to increase diagnosis precision and remove biases inherent in manual analysis.
3. Consistency: Provides repeatable analysis, reducing variability and ensuring standardized incident handling.
4. Scalability: Well-suited for large and dynamic environments, including cloud, IoT, and distributed systems.
5. Cost Efficiency: Cuts operational costs by decreasing manual investigation workload and streamlining incident management.
6. Proactive Prevention: Identifies systemic issues and configuration drift that increase vulnerability, supporting preventive measures.
Challenges and Best Practices
Several critical factors influence the success of automated root cause analysis. The following points highlight challenges organizations face and best practices to ensure trustworthy outcomes..png)
