Identifying attack surface gaps is a critical element in cybersecurity and ethical hacking, as these gaps represent unprotected or vulnerable points within an organization’s digital infrastructure that adversaries might exploit. Traditionally, uncovering these gaps involved manual analysis and static scanning, which are often time-consuming and prone to oversight.
Artificial intelligence (AI) pattern analysis now offers a revolutionary approach by automatically sifting through vast volumes of data to detect discrepancies, anomalies, and overlooked assets that represent attack surface gaps.
By leveraging AI-driven pattern recognition, security professionals can gain early, actionable insights into vulnerabilities and exposures that might otherwise remain hidden, enabling proactive risk mitigation.
Understanding Attack Surface Gaps
An attack surface encompasses all possible points—hardware, software, network interfaces, user access—that an attacker can use to infiltrate or affect a system. Attack surface gaps are essentially blind spots or weaknesses not adequately secured or monitored, including:
Identifying these gaps accurately and continuously is paramount for effective cybersecurity posture management.
Role of AI Pattern Analysis in Detection
AI pattern analysis uses machine learning algorithms and statistical models to analyze data collected from network traffic, logs, asset inventories, vulnerability scans, and external threat intelligence to highlight inconsistencies indicative of attack surface gaps:
1. Anomaly Detection: AI models learn normal behavior patterns and flag deviations such as unexpected network flows, unusual user behavior, or atypical system calls that may signal exposed resources or breaches.
2. Correlation of Disparate Data: AI integrates heterogeneous data sources (asset databases, configuration files, access logs) to detect overlapping vulnerabilities or missing controls that manual methods might miss.
3. Trend Analysis: Temporal analysis helps discover emerging attack surface gaps caused by recent changes, software updates, or configuration drift.
4. Risk Prioritization: AI ranks identified gaps by exploitability and business impact using predictive analytics, helping allocate remediation resources effectively.
5. Graph-Based Analysis: AI constructs attack graphs mapping permissible access paths and identifies weak links within network topology or cloud infrastructure.
Techniques Used in AI Pattern Analysis for Attack Surface Gaps
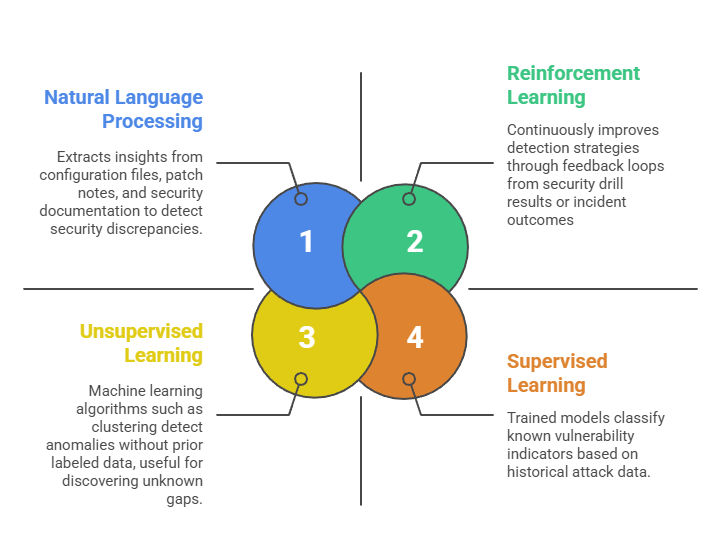
By applying diverse machine learning and NLP approaches, AI can reveal both known and unknown vulnerabilities. Below are some of the primary techniques that power AI-driven pattern analysis.
Benefits of AI in Identifying Attack Surface Gaps
AI-driven analysis helps organizations detect, prioritize, and respond to vulnerabilities with greater accuracy. The following points outline the primary benefits of using AI for attack surface gap identification.
1. Comprehensive Visibility: Identifies hidden and dynamic attack surfaces across on-premises, cloud, and hybrid environments.
2. Improved Detection Accuracy: Reduces false positives and missed vulnerabilities via continuous learning and multi-source correlation.
3. Proactive Risk Management: Detects emerging gaps early, enabling timely patching and reconfiguration before exploitation.
4. Resource Optimization: Focuses security operations on critical gaps prioritized by potential impact.
5. Scalability: Handles large and complex IT environments beyond human analytical capacity.
Challenges and Best Practices
While AI brings powerful insights, its success depends on maintaining data integrity, transparency, and ethical handling. Here’s a list of important considerations and recommended practices to keep in mind.
.png)
