Detecting application weaknesses is a crucial aspect of cybersecurity that involves identifying vulnerabilities, misconfigurations, and coding flaws which can be exploited by attackers to compromise systems. Traditional vulnerability detection methods often rely on manual code reviews, signature-based tools, and static analysis, which may miss complex, subtle, or evolving weaknesses.
AI-powered pattern recognition has emerged as a transformative approach, leveraging machine learning and advanced analytics to automatically analyze application code, runtime behavior, and system interactions.
By recognizing known and previously unseen patterns of vulnerabilities, AI enhances the accuracy, speed, and scope of application security assessments, enabling organizations to proactively detect and remediate weaknesses before exploitation occurs.
How AI-Powered Pattern Recognition Works
AI applies pattern recognition techniques at various stages of the application security lifecycle:
1. Static Code Analysis: AI models analyze source code or binaries to identify patterns matching known vulnerability signatures such as buffer overflows, injection flaws, broken authentication, and insecure API usage.
2. Dynamic Analysis: Pattern recognition techniques monitor application behavior during execution, detecting anomalous input/output sequences, memory usage anomalies, or unexpected network calls indicative of security flaws.
3. Machine Learning-Based Anomaly Detection: Leveraging supervised or unsupervised learning, AI identifies deviations from normal programming or runtime patterns that may signal vulnerabilities or exploits.
4. Natural Language Processing (NLP): Applied to documentation, code comments, and vulnerability reports to extract security-related insights and map them to code segments.
5. Automated Pattern Mining: AI discovers novel vulnerability patterns by mining large datasets of codebases, vulnerability databases, and historical attack data.
These combined AI approaches enable comprehensive and continuous scanning for weaknesses within applications.
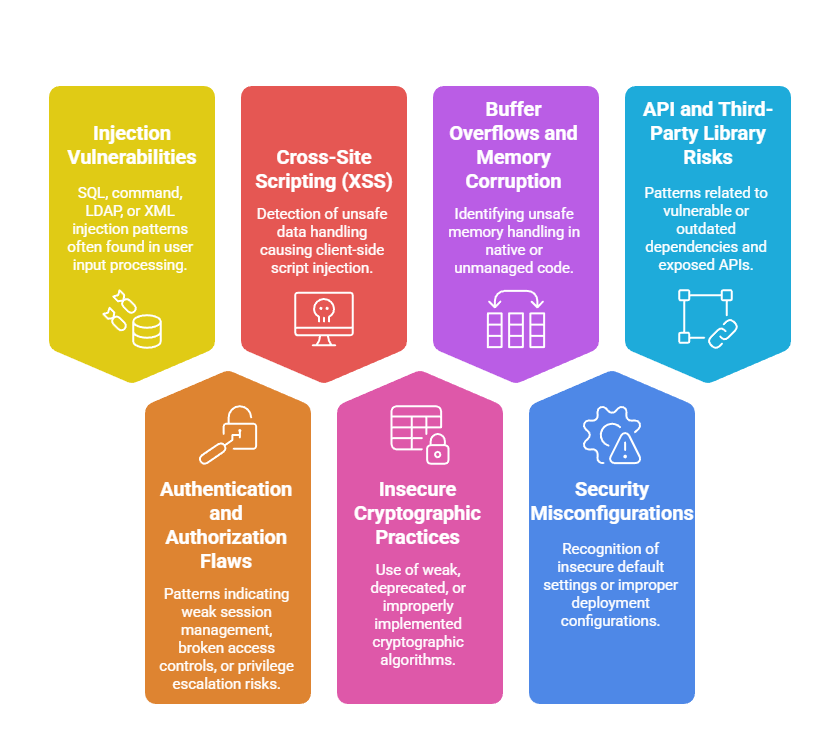
Key Application Weaknesses Detected
AI pattern recognition targets a wide range of common and advanced application security weaknesses:
Benefits of Using AI for Application Weakness Detection
From real-time monitoring to intelligent alerting, AI helps developers and security teams uncover hidden application flaws. Here’s a list of major advantages of AI-assisted application weakness detection.
1. Higher Accuracy and Coverage: Identifies complex patterns and zero-day weaknesses beyond conventional rule-based tools.
2. Speed and Scalability: Processes large codebases and application telemetry efficiently without human bottlenecks.
3. Continuous Monitoring: Supports real-time detection during development and production phases (DevSecOps integration).
4. Reduced False Positives: Learns from historical data to improve alert relevance and reduce noise.
5. Context Awareness: Understands application logic and flow to accurately identify exploitable issues.
6. Integration with Security Workflows: Seamlessly connects with IDEs, CI/CD pipelines, and security orchestration platforms.
Challenges and Practical Considerations
Integrating AI into application security introduces technical, operational, and interpretability challenges that must be addressed. Below are the core challenges and considerations to ensure effective use of AI.
1. Data and Model Quality: Effective detection requires well-trained AI models with diverse, high-quality training data covering various languages and frameworks.
2. Interpretability: Security teams need transparent AI decision-making to trust findings and prioritize remediation.
3. Complexity of Modern Applications: Microservices, containerized environments, and serverless architectures add detection complexity.
4. Keeping Pace with Threats: Regular model updates and continuous learning are necessary to capture emerging vulnerabilities.
5. Human Expertise: AI assists but does not replace skilled security analysts for validation, tuning, and contextual assessment.
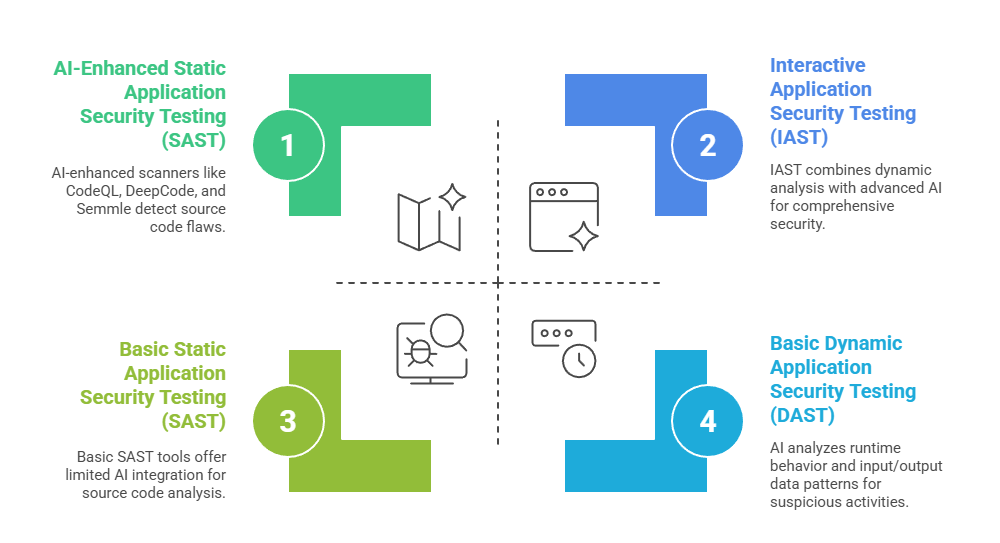
Tools and Technologies
By leveraging static, dynamic, and interactive testing along with threat intelligence, AI strengthens application security coverage. The following points highlight the main tools and technologies used in AI-based application vulnerability detection.
Class Sessions
Sales Campaign

We have a sales campaign on our promoted courses and products. You can purchase 1 products at a discounted price up to 15% discount.
