Artificial Intelligence (AI) is rapidly transforming cybersecurity, bringing both new capabilities and challenges to the field of ethical hacking. AI enhances traditional cybersecurity techniques by enabling faster, more accurate detection of threats, improved analysis of large data sets, and automation of routine security tasks.
In ethical hacking, AI tools support penetration testing by automating reconnaissance, vulnerability identification, and threat simulations, thus helping security professionals proactively defend systems against evolving cyber threats.
However, AI also introduces new attack surfaces and malicious AI-powered threats, making it crucial to understand both defensive and offensive AI applications in cybersecurity.
AI in cybersecurity works by analyzing vast amounts of data from network traffic, logs, and user behavior to identify anomalies and patterns that could indicate attacks.
Machine learning models enhance threat detection beyond signature-based methods by identifying new and unknown threats in real-time. AI also supports tailored responses to incidents, automates repetitive tasks, and enables predictive threat intelligence.
Generative AI algorithms further empower analysts by automating complex analyses and generating threat scenarios, improving the efficiency and effectiveness of cybersecurity defenses.
Benefits of AI in Cybersecurity
With evolving digital threats, AI brings advanced capabilities to detect, prevent, and respond to attacks. Here’s a list of the major ways AI enhances cybersecurity operations.
1. Real-time threat detection and automated response reduce breach damage and speeds mitigation.
2. Anomaly detection identifies insider threats and sophisticated cyberattacks.
3. AI accelerates penetration testing and red team exercises by automating vulnerability mapping and attack path simulation.
4. Enhances security operations with AI-assisted log analysis, event correlation, and behavioral analytics.
5. AI-powered zero trust and adaptive access control improve authorization decisions based on context and behavior.
6. Supports continuous learning and adaptation against emerging threats for evolving cyber defense strategies.
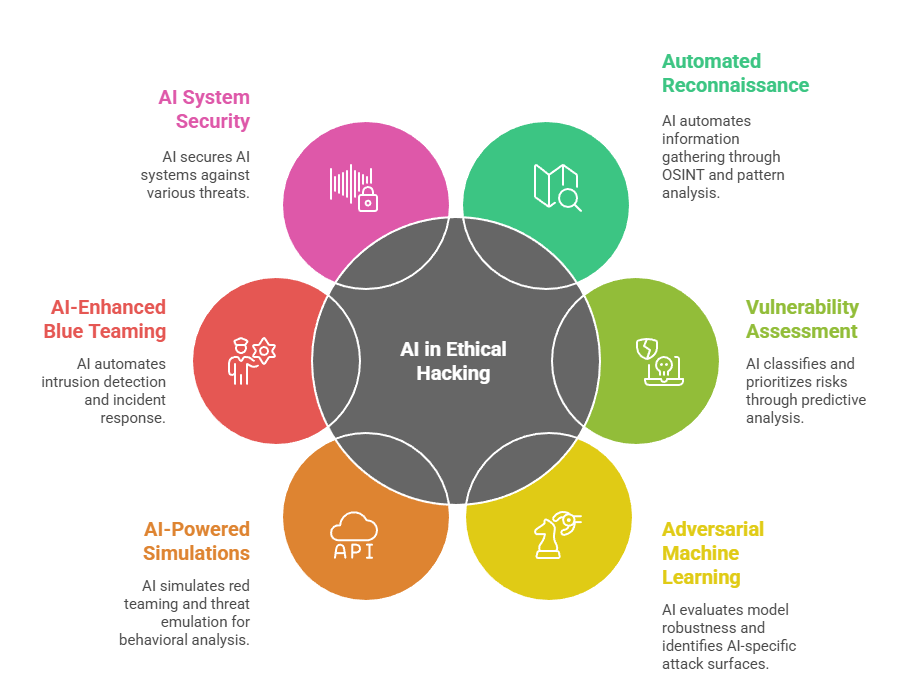
Applications of AI in Ethical Hacking
AI is redefining ethical hacking by automating complex tasks and uncovering hidden security gaps. Below are key applications showing how AI supports modern offensive and defensive security practices.
Challenges and Ethical Considerations
While AI strengthens cybersecurity defenses, it also expands the attack surface and can be leveraged by adversaries to launch sophisticated AI-driven attacks. Ethical hackers must understand AI limitations, risks, and responsible AI guidelines to prevent misuse.
Transparency, bias reduction, and adherence to compliance standards are crucial when deploying AI-based security tools. Safe adversarial testing and continuous monitoring help ensure AI systems remain secure and trustworthy.
