Intrusion Detection Systems (IDS) are critical components in cybersecurity frameworks designed to monitor and analyze network traffic for signs of malicious activities or policy violations. Traditional IDS solutions rely heavily on signature-based detection methods that identify known threats but often fail to detect novel or sophisticated attacks.
The explosion of network data combined with evolving threat landscapes has made manual analysis increasingly impractical. Artificial Intelligence (AI) has transformed intrusion detection by providing automated, intelligent, and adaptive capabilities, improving detection precision, reducing false positives, and accelerating security incident response through event correlation.
AI in Intrusion Detection: Enhancing Threat Identification
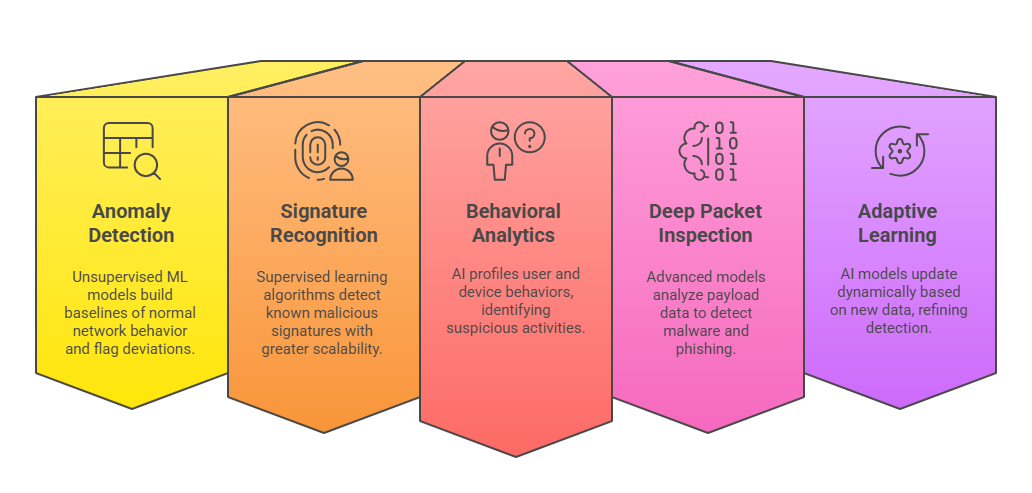
AI-powered IDS utilize machine learning (ML) and deep learning (DL) algorithms to analyze large volumes of network, system, and application logs in real time:
Expected outcomes include higher detection accuracy, faster threat identification, and reduced analyst fatigue.
Event Correlation: Connecting the Dots for Contextual Insight
Event correlation involves aggregating and analyzing discrete security events from multiple sources to identify meaningful patterns that indicate coordinated or ongoing attacks:
1. Multi-Source Integration: AI aggregates logs and alerts from firewalls, IDS/IPS, endpoints, applications, cloud platforms, and threat intelligence feeds.
2. Correlation Algorithms: Machine learning groups related events by temporal and logical relationships, exposing complex attack campaigns hidden in dispersed alerts.
3. Prioritization and Scoring: AI assigns risk scores to correlated events enabling analysts to focus on high-priority incidents.
4. Automated Incident Generation: Correlated events trigger predefined workflows or alerts, accelerating incident response.
5. Root Cause Analysis: Behavioral traces reconstructed through correlation help identify attack vectors and compromised assets.
Event correlation reduces alert fatigue, improves threat visibility, and enables more effective security operations center (SOC) performance.
Benefits of AI-Powered Intrusion Detection and Correlation
The list below highlights how AI transforms intrusion detection and event correlation operations. These advantages enable predictive insights, contextual alerting, and scalable monitoring.
1. Enhanced Detection Rates: AI identifies both known and novel threats with improved accuracy and fewer false positives.
2. Scalable Real-Time Monitoring: Processes massive data volumes continuously across complex, distributed network environments.
3. Context-Enriched Alerts: Event correlation enriches alerts with contextual information, leading to informed, faster decision making.
4. Proactive Defense Posture: Enables predictive threat detection and automated mitigation efforts.
5. Resource Optimization: Reduces manual analysis workload while augmenting analyst effectiveness.
Challenges and Best Practices
Below are the key challenges and recommended practices to ensure effective AI adoption in security workflows. These points highlight essential considerations for reliability, trust, and operational fit.
.png)
Class Sessions
Sales Campaign

We have a sales campaign on our promoted courses and products. You can purchase 1 products at a discounted price up to 15% discount.
