Log analysis and threat detection are fundamental components of cybersecurity operations, enabling organizations to monitor system activities, identify security incidents, and respond timely to mitigate potential damages. Traditionally, log analysis has been a laborious and manual process, involving sifting through massive volumes of logs generated by diverse systems and applications.
However, the exponential growth in data volume, complexity, and sophisticated attack patterns has outpaced human capabilities, necessitating intelligent automation. Artificial intelligence (AI), with its ability to process large datasets, recognize complex patterns, and learn from evolving threats, has revolutionized log analysis and threat detection.
AI-assisted solutions enhance the speed, accuracy, and effectiveness of identifying malicious activities, reducing the threat detection time and improving incident response.
AI in Log Analysis: Transforming Raw Data into Insights
Logs are generated by various devices, including servers, firewalls, IDS/IPS, applications, and network devices. These logs contain valuable information about system events, user activities, network traffic, and potential security incidents. AI streamlines log analysis through:
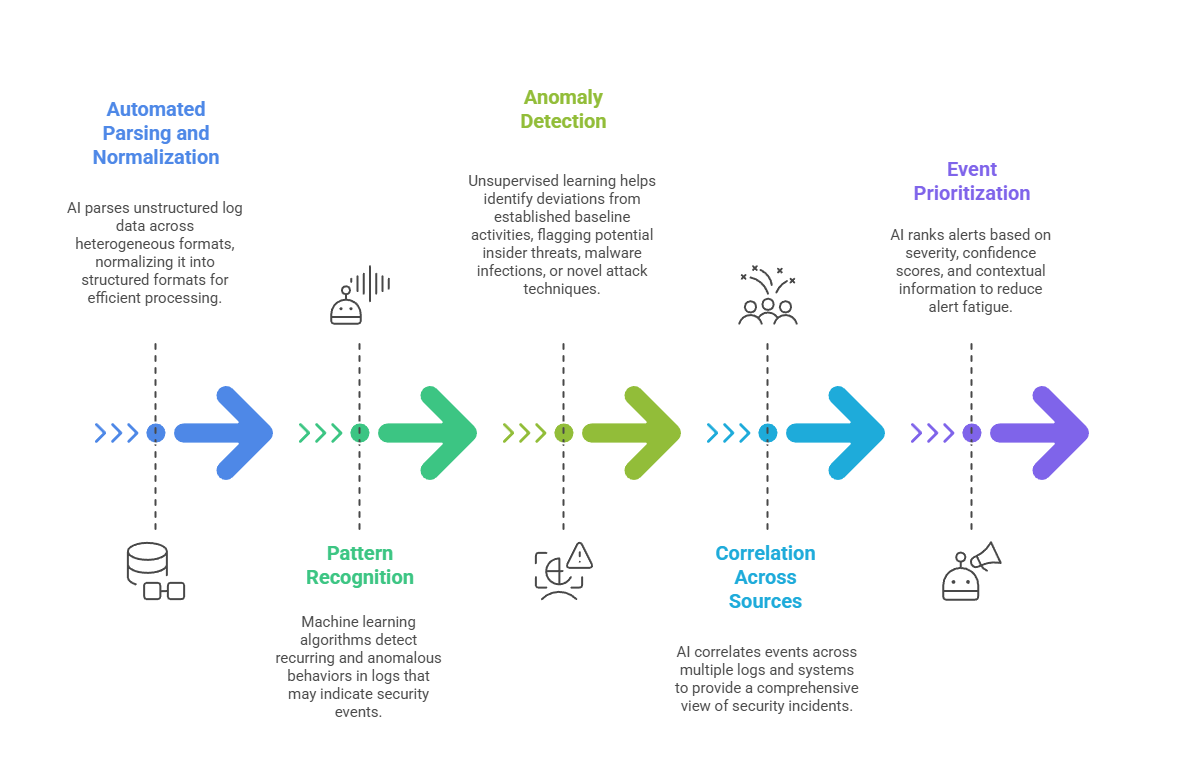
By automating these processes, AI greatly accelerates the conversion of raw log data into actionable threat intelligence.
AI-Driven Threat Detection Approaches
AI techniques play a vital role in enhancing traditional rule-based threat detection systems, extending capabilities to identify sophisticated, unknown, and evolving threats:
1. Supervised Machine Learning: Models trained on labeled datasets of known attacks detect patterns consistent with malware, phishing, or exploitation attempts.
2. Unsupervised Learning: Detects unknown threats by finding anomalies without prior knowledge, enabling discovery of zero-day attacks.
3. Deep Learning: Neural networks analyze complex sequences in log data, recognizing subtle attack signatures and behavioral anomalies.
4. Natural Language Processing (NLP): Extracts meaningful patterns from textual data within logs and security reports.
5. Behavioral Analytics: AI models profile normal user and system behaviors to spot deviations signaling account compromise or insider threats.
6. Threat Intelligence Integration: Incorporates external threat feeds and indicators of compromise (IOC) to enrich detection accuracy.
These AI-driven methods enable continuous learning and adaptation, essential against increasingly sophisticated cyber threats.
Benefits of AI-Assisted Log Analysis and Threat Detection
AI-assisted log analysis enhances threat detection by processing vast data quickly and providing actionable insights. Below are the key benefits that demonstrate how AI strengthens monitoring and incident response.

Challenges and Considerations
From noisy datasets to evolving threats, several factors can impact AI effectiveness in log analysis. The following points highlight the main challenges and considerations.
1. Data Quality and Volume: Requires high-quality, well-maintained log data; noisy or incomplete logs degrade AI accuracy.
2. Model Explainability: Ensuring AI decisions are interpretable to build analyst trust.
3. Integration Complexity: Seamlessly combining AI solutions with existing SIEM, SOAR, and SOC workflows can be challenging.
4. Privacy and Compliance: Securely handling sensitive log data while complying with regulations.
5. Continuous Updating: Regularly updating models to adapt to new threats and environmental changes.
