Identifying abnormal network behavior is a critical function in cybersecurity, enabling organizations to detect potential security threats such as intrusions, malware propagation, data exfiltration, and insider attacks. Normal network traffic follows predictable patterns based on business operations, user activities, and system communications.
Deviations from these patterns—referred to as anomalies—often signal malicious activity or misconfigurations. Traditional rule-based detection systems have limitations in identifying novel or subtle abnormalities across large-scale networks.
Artificial intelligence (AI) techniques, such as traffic clustering and anomaly detection, have become increasingly vital tools to automatically analyze complex network traffic data, detect unusual behavior, and provide timely alerts to security teams.
Understanding Traffic Clustering in Network Monitoring
Traffic clustering categorizes network data into groups with similar characteristics, enabling the identification of patterns and the separation of normal from abnormal traffic flows. Key aspects of traffic clustering include:
1. Feature Extraction: Extracting attributes such as packet size, frequency, source/destination IPs, protocols used, and timing intervals from raw network traffic.
2. Unsupervised Learning Algorithms: Techniques like k-means, DBSCAN, and hierarchical clustering group traffic flows based on similarity without prior labeling.
3. Behavior Profiling: Clusters representing normal operational activities establish behavioral baselines for network segments, applications, or devices.
4. Outlier Detection: Traffic flows that do not fit into established clusters are flagged as potential anomalies deserving further investigation.
Traffic clustering helps reduce noise in network data and supports focused anomaly detection by isolating suspicious traffic patterns.
Anomaly Detection Techniques for Network Behavior
Anomaly detection algorithms assess network data to identify outliers or deviations that may correspond to threats:
1. Statistical Methods: Measure deviations from expected metrics such as traffic volume, connection duration, or error rates.
Machine Learning-Based Detection:
Supervised Models classify traffic as normal or abnormal based on historical labeled data.
Unsupervised Models identify novel anomalies by learning the normal traffic distribution.
Deep Learning Models, including autoencoders and recurrent neural networks, detect complex temporal anomalies and sequences.
2. Time-Series Anomaly Detection: Monitors traffic patterns over time to detect spikes or gradual deviations indicating attacks.
3. Hybrid Approaches: Combine rule-based filters with AI models for improved detection accuracy and fewer false positives.
4. Correlation Analysis: Combines network anomalies with alerts from other sources to improve contextual understanding.
AI-powered anomaly detection continuously adapts to evolving network conditions, improving resilience against emerging threats.
Benefits of AI for Identifying Abnormal Network Behavior
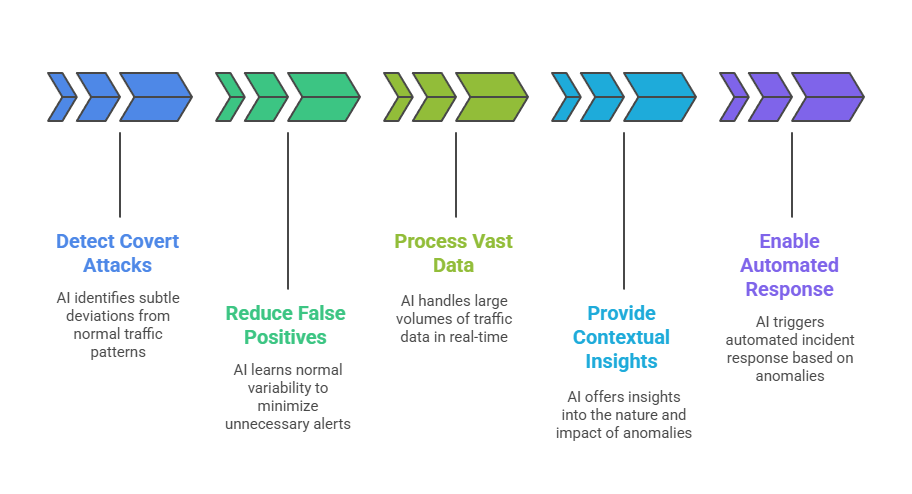
From early detection to contextual insights, AI improves both the speed and accuracy of identifying abnormal network activity. The following points highlight the main benefits of AI for network anomaly detection.
Use Cases and Applications
AI-powered systems improve visibility and response to evolving network threats, both internal and external. Below are some core use cases and applications for AI in network security.
1. Intrusion Detection Systems (IDS): Enhances IDS capabilities by dynamically identifying suspicious network activity.
2. Insider Threat Monitoring: Spots unusual access patterns or data transfers indicative of insider misuse.
3. Botnet and Malware Detection: Identifies command-and-control traffic and unusual outbound communications.
4. Denial-of-Service (DoS) Attack Detection: Detects abnormal traffic volume surges signaling DoS attempts.
5. Cloud Network Security: Monitors cloud traffic for anomalous behaviors across virtualized environments.
Challenges and Considerations
Deploying AI for anomaly detection requires balancing data quality, model adaptability, and operational resource requirements. Here are the essential challenges and considerations for successful implementation.
1. Data Quality: Accurate anomaly detection requires comprehensive and clean traffic data.
2. Evolving Baselines: Normal behavior can change over time, requiring adaptive model updates.
3. Complexity and Interpretability: AI models can be complex; providing understandable alerts is essential.
4. Resource Requirements: Real-time analysis of high-volume data demands significant computational capacity.
5. Integration: Effectively correlating network anomalies with other security events for comprehensive detection.
