Web and network footprinting is a fundamental phase in ethical hacking and cybersecurity assessments where the goal is to gather information about a target's internet presence and network architecture. Traditionally, footprinting involved manual techniques to identify IP ranges, domain information, server details, open ports, and services running on the network.
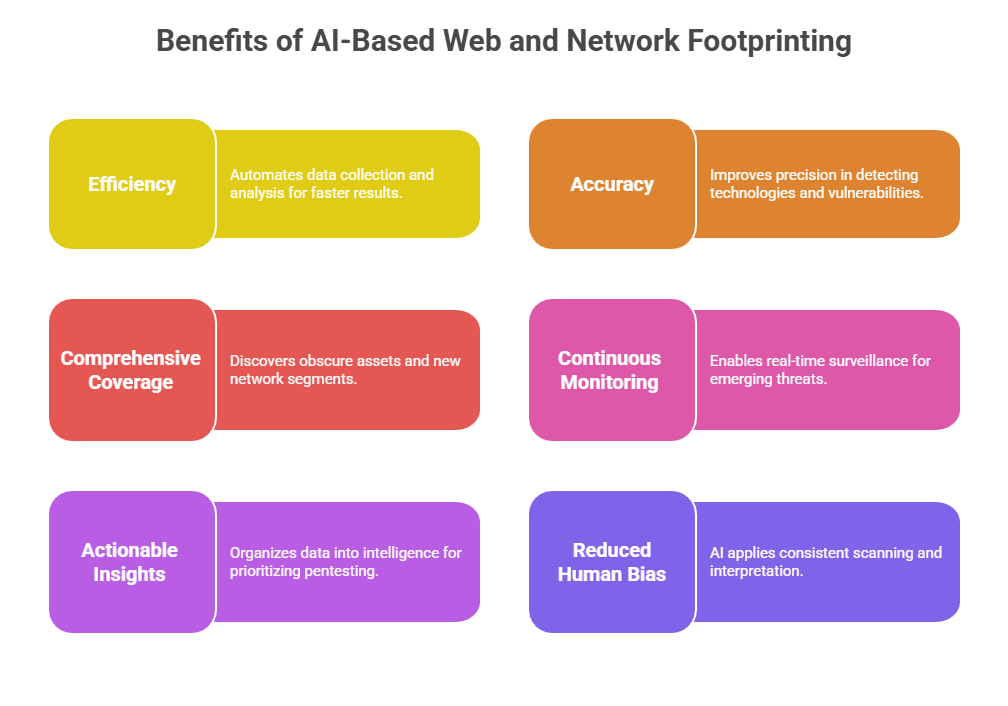
With advancements in artificial intelligence (AI), footprinting has evolved to become more automated, intelligent, and insightful. AI-based footprinting tools leverage data analytics, machine learning, and pattern recognition to not only collect data at scale but also derive actionable intelligence that improves understanding of the target’s attack surface and assists in planning penetration testing or defensive strategies.
AI-Based Web Footprinting Insights
AI automates and enriches the discovery and analysis of a target's web presence through the following techniques:
1. Domain and Subdomain Enumeration: AI tools crawl DNS records and public data sources to automatically discover primary domains and subdomains, including hidden or forgotten ones that increase the attack surface.
2. Web Asset Identification: Automated scanning identifies all web-facing applications, hosting environments, Content Management Systems (CMS), and third-party integrations.
3. Content Analysis: AI-powered natural language processing (NLP) examines website content, metadata, and source code to identify technologies used (e.g., server types, frameworks, plugins), version info, and potential vulnerable components.
4. Change Detection: Machine learning models monitor web assets over time to detect unauthorized content changes, defacements, or exposure of sensitive information.
5. Link Graphs and Relationship Mapping: AI constructs maps showing how different domains, subdomains, IP addresses, and external links interconnect, revealing dependencies and potential pivot points for attackers.
AI enables faster, deeper, and more continuous web footprinting beyond traditional manual techniques, uncovering subtle details and evolving risks.
AI-Based Network Footprinting Insights
Network footprinting powered by AI enhances mapping and analysis of the target network architecture, including devices, connectivity, and security controls:
1. IP Range Discovery: Automated scanning combined with AI analytics identifies active IP ranges and subnet boundaries.
2. Port and Service Enumeration: Intelligent scanning tools detect open ports and running services, classifying them based on behavior and known vulnerabilities.
3. Protocol Anomaly Detection: AI monitors network traffic and flags unusual patterns or protocol irregularities that might indicate misconfigurations or backdoors.
4. Device Fingerprinting: Machine learning models analyze network responses to accurately identify devices, operating systems, and firmware versions.
5. Topology Reconstruction: AI algorithms visualize network layouts from gathered data, helping understand segmentation and potential lateral movement paths.
6. Threat Correlation: Network footprint data is correlated with threat intelligence feeds to flag IPs or services with known malicious activity or prior compromise.
Together, these AI-augmented methods produce a comprehensive, dynamic network footprint critical for accurate vulnerability assessments.
 Challenges and Considerations
Challenges and Considerations
Despite its advantages, AI is not immune to error, compliance constraints, or data quality dependencies. Below are the primary challenges that teams should evaluate before relying on AI-powered processes.
1. False Positives/Negatives: AI systems may misclassify benign or risky assets without human validation.
2. Privacy and Compliance: Automated crawling and scanning require adherence to legal guidelines and ethical standards.
3. Data Overload: Large amounts of collected data need to be effectively filtered and contextualized to avoid analyst fatigue.
4. Dependence on Quality Inputs: AI output quality depends on data freshness and diversity.
