Predictive vulnerability analysis is an emerging approach in cybersecurity that leverages artificial intelligence (AI) and machine learning to forecast future vulnerabilities and detect anomalous patterns indicative of potential security weaknesses.
Unlike traditional vulnerability management, which largely reacts to known disclosures, predictive analysis aims to proactively identify likely vulnerabilities and emerging threats before they are widely exploited.
This proactive capability is crucial in today’s rapidly evolving threat landscape, where zero-day vulnerabilities and sophisticated attacks can cause significant damage. By using trend prediction and anomaly spotting, organizations can prioritize defensive measures, optimize patch management, and stay ahead of cyber adversaries.
Trend Prediction in Vulnerability Analysis
Trend prediction involves analyzing historical vulnerability data, threat intelligence, patch release cycles, and exploit occurrences to forecast future security risks. Key processes include:
1. Historical Data Analysis: AI models are trained on large datasets of past vulnerabilities, including their discovery, disclosure, exploitation timelines, and remediation effectiveness.
2. Pattern Recognition: Machine learning algorithms detect recurring patterns or seasonal trends, such as vulnerability spikes in certain software categories or changes following major software updates.
3. Threat Intelligence Integration: Correlates external threat feeds, dark web monitoring, and attacker behaviors to identify shifts in exploit tactics and target preferences.
4. Predictive Modeling: Statistical and machine learning models predict which systems or components are likely to exhibit vulnerabilities soon, helping allocate resources efficiently.
Trend prediction supports strategic planning by anticipating surges in vulnerability disclosures or exploit attempts in specific technologies or sectors.
Anomaly Spotting for Early Detection
Anomaly spotting focuses on identifying unusual patterns or deviations in system behavior, network traffic, or vulnerability data that may signal new or unknown vulnerabilities:
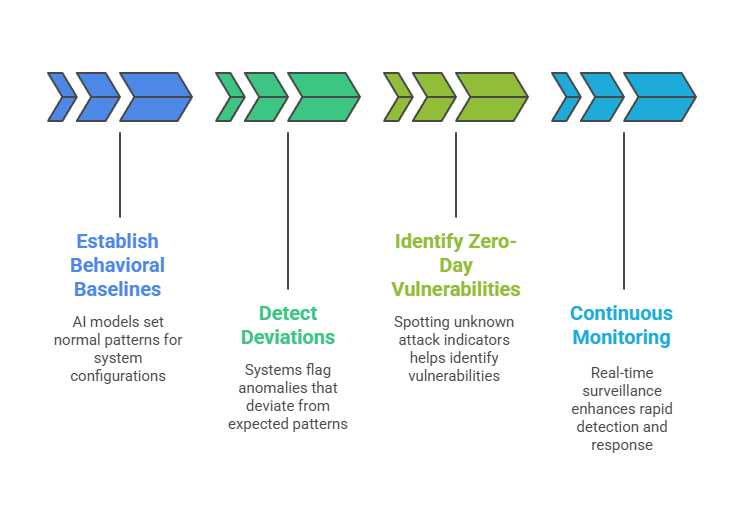
Together, anomaly spotting complements trend prediction by providing early warnings about novel or evolving threats.
AI Techniques in Predictive Vulnerability Analysis
AI-driven analysis helps organizations forecast vulnerabilities, understand attack pathways, and improve risk prioritization. The following points highlight the main techniques applied in predictive vulnerability analysis.
1. Supervised Learning: Uses labeled historical data to predict vulnerability outcomes and classify risk levels.
2. Unsupervised Learning: Identifies clusters or outliers in vulnerability data for anomaly detection.
3. Time-Series Forecasting: Models temporal patterns in vulnerability emergence and exploit activity.
4. Natural Language Processing (NLP): Analyzes text from vulnerability reports, advisories, and threat intelligence to extract signals for prediction.
5. Graph Machine Learning: Maps relationships among vulnerabilities, assets, and threat actors to uncover attack pathways and predict risk propagation.
Benefits of Predictive Vulnerability Analysis
Forecasting vulnerabilities allows security teams to focus on high-impact threats and minimize potential exploitation windows. Listed below are the key advantages of using predictive analysis for vulnerability management.

Challenges and Considerations
Implementing predictive analysis requires balancing data availability, model complexity, and integration with existing security workflows. Here are the main challenges and considerations for effective deployment.
1. Data Availability and Quality: Reliable predictions require comprehensive, timely, and high-quality data.
2. False Positives/Negatives: Misclassification can lead to unnecessary remediation or missed threats.
3. Model Complexity: Balancing accuracy with interpretability to build user trust and actionable outputs.
4. Dynamic Environments: Systems must adapt to rapid technology changes and emerging threat vectors.
5. Integration Needs: Combining predictive insights with existing vulnerability management and security operations processes.
Class Sessions
Sales Campaign

We have a sales campaign on our promoted courses and products. You can purchase 1 products at a discounted price up to 15% discount.
