AI-assisted entity extraction is a powerful technique in the field of cybersecurity and ethical hacking that leverages artificial intelligence algorithms to automatically identify and extract key entities such as domains, people, organizations, technologies, and other relevant data from unstructured text and diverse data sources.
Entity extraction transforms raw, scattered data into structured, meaningful information, enabling security professionals to connect the dots and gain deep insights into their targets.
This technology is essential for accelerating reconnaissance, enriching Open Source Intelligence (OSINT), and enhancing the accuracy of threat analysis by providing comprehensive visibility into adversary infrastructures and operations.
Understanding AI-Assisted Entity Extraction
Entity extraction involves parsing text or datasets to locate and classify predefined categories of information. AI advances, especially in Natural Language Processing (NLP) and machine learning, have transformed entity extraction from simple keyword matching to sophisticated semantic understanding and context-aware recognition:
1. Natural Language Processing (NLP): NLP techniques enable machines to process human language, handling ambiguity, synonyms, and context to better identify entities in unstructured data.
2. Named Entity Recognition (NER): A core NLP task, NER models classify and tag entities like names of persons, organizations, locations, dates, and numerical expressions.
3. Deep Learning Models: Neural networks, including transformers, enhance entity extraction by learning complex linguistic patterns and relationships beyond rule-based detection.
4. Contextual Embeddings: Models like BERT contextualize entities within sentences, improving precision in disambiguating similar entity names.
5. Multi-Source Integration: AI systems aggregate data from social media, websites, dark web, technical documents, and more, combining context for richer extraction.
Types of Entities Extracted in Cybersecurity
In ethical hacking and security intelligence, the following entities are most critical:
1. Domains and URLs: Web addresses associated with the target network or attacker infrastructure.
2. IP Addresses: Internet Protocols that identify hosting servers or attacker nodes.
3. Person Names: Employees, executives, or threat actors linked to the organization or campaign.
4. Organizations: Companies, subsidiaries, partners, or threat groups relevant to investigation.
5. Technologies: Software, hardware, platforms, or tools identified in system fingerprints or attack signatures.
6. Email Addresses and Usernames: Contact points or account identifiers used for phishing or social engineering reconnaissance.
7. File Hashes and Malware Signatures: Unique identifiers of known malicious files or code variants.
Benefits of AI-Assisted Entity Extraction
Entity extraction powered by AI offers faster processing, richer insights, and better scalability for evolving security needs. Here are the primary benefits that demonstrate why this technology is increasingly adopted.
1. Efficiency: Automates repetitive manual data extraction tasks, saving time and resources.
2. Accuracy: Reduces human error through consistent and precise identification across large datasets.
3. Comprehensiveness: Processes heterogeneous data sources for a holistic view.
4. Contextual Insights: Understands entity relationships and hierarchies to reveal hidden threats.
5. Scalability: Handles ever-growing volumes of textual and technical data relevant to cybersecurity.
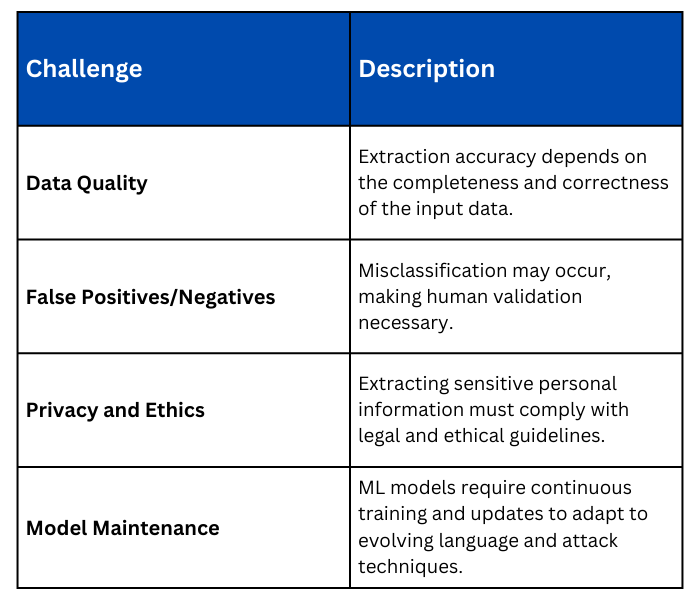
Challenges to Consider
.png)
