Sensitive data handling is a critical component of ethical data science, ensuring that personal, confidential, or high-risk information is managed with maximum security and respect.
Sensitive data may include health records, financial transactions, biometric identifiers, location trails, behavioral patterns, or any information that can cause harm if misused or exposed.
As organizations collect increasingly granular data through apps, sensors, AI systems, and third-party platforms, they must adopt robust practices that minimize risk while maximizing the ethical value of data.
1. Data Classification and Risk Assessment
Effective sensitive data handling begins with classifying data based on its sensitivity, potential impact, and level of protection required.
Organizations often fail because they treat all data equally, leading to under-protection of highly sensitive categories like biometrics or medical records.
Risk assessments help identify vulnerabilities and determine necessary controls such as encryption, restricted access, or stricter retention policies.
Ethical frameworks require regular reassessment as new data types emerge or existing datasets grow.
By understanding the nature and value of data, organizations can apply tailored safeguards rather than generic, insufficient measures.
2. Principle of Least Privilege and Access Control
Access to sensitive data must be strictly limited to individuals who genuinely need it for their role.
The “least privilege” principle ensures that both employees and automated systems have minimal access necessary to perform their tasks.
Role-based access control (RBAC), multi-factor authentication, and continuous monitoring further strengthen protections.
Many real-world breaches occur because unnecessary access permissions remain active for months or years.
Ethical systems require periodic reviews, immediate revocation of outdated privileges, and logging every access attempt.
This prevents internal misuse and reduces exposure during cyberattacks.
3. Secure Collection, Storage, and Transfer of Data
Sensitive data must be collected using secure channels (such as encrypted forms or APIs), stored using strong encryption standards, and transferred only through verified, encrypted pathways.
Misconfigurations in cloud storage—like open S3 buckets—are one of the leading causes of global data leaks.
Ethical data management demands frequent security audits, encryption key rotation, vulnerability scanning, and backup integrity checks.
When sharing data externally, organizations must verify partner security, use secure file exchange protocols, and apply watermarking or anonymization to reduce risk.
Secure handling at every step prevents unauthorized access and preserves data integrity.
4. Privacy-by-Design and Secure System Architecture
Privacy-by-design (PbD) requires integrating privacy and protection measures into systems from the beginning, rather than adding them as a patch later.
This includes designing systems that minimize data collection, incorporate default encryption, and log every action that affects sensitive datasets.
Ethical PbD encourages early threat modeling, security testing, and the use of privacy-preserving technologies such as differential privacy or federated learning.
When privacy is embedded into architecture, the likelihood of vulnerabilities, misuse, or unintentional exposure drops significantly.
This proactive approach builds long-term resilience and user trust.
5. Strong Data Minimization and Ethical Retention Policies
Data minimization ensures that only essential information is collected and stored, reducing the risk of exposure.
Ethical retention policies further require deleting data once it is no longer needed for the original purpose.
Excessive retention is a silent risk—legacy databases, unused backups, and forgotten logs often contain sensitive data that attackers can exploit.
Regular deletion, archival reviews, and automated cleanup tools ensure that sensitive information does not linger unnecessarily.
Minimization and retention policies also support compliance with modern privacy laws, which emphasize “collect less, keep less.”
6. Monitoring, Incident Detection, and Rapid Response Plans
Constant monitoring of sensitive data environments helps detect unusual behavior, such as unauthorized access or large downloads.
Ethical systems include intrusion detection tools, anomaly detection models, detailed audit logs, and automated alerts.
If a breach occurs, a rapid response plan ensures swift containment, communication, investigation, and remediation.
This minimizes harm to affected individuals and prevents further misuse of exposed data.
Transparency—informing users and regulators promptly forms a key ethical requirement. Without strong monitoring, even well-protected data can go unnoticed when compromised.
7. Employee Training, Governance, and Accountability
Human error remains the leading cause of data breaches; therefore, continuous training on secure practices, phishing awareness, and ethical responsibilities is essential.
Governance structures ensure accountability by defining who owns datasets, who approves access, and who is responsible for audits and compliance.
Organizations should maintain clear policies, enforce disciplinary actions when necessary, and foster a culture of privacy awareness rather than viewing compliance as a checklist task.
Ethical handling is effective only when employees understand the seriousness of sensitive data protection.
8. Ethical Vendor Management and Third-Party Security Controls
Modern organizations rely heavily on third-party vendors—cloud providers, analytics platforms, payment processors, and AI service companies.
Even if an organization manages its own data securely, sensitive information can still be exposed through weak vendor practices.
Ethical data handling therefore requires thorough vendor audits, contractual safeguards, due diligence checks, and continuous monitoring of third-party access.
Organizations must ensure vendors follow strong encryption standards, maintain compliance certifications, and implement access restrictions.
Weak vendor oversight has been responsible for many major breaches, making third-party governance a critical part of responsible data protection.
9. Advanced Privacy-Preserving Techniques (PPTs)
New technologies such as homomorphic encryption, secure multi-party computation, and synthetic data generation provide powerful tools for handling sensitive information without exposing raw data.
These techniques allow organizations to analyze data securely, support AI training, or collaborate across teams without revealing underlying personal details.
Homomorphic encryption enables computations on encrypted data, while SMPC distributes sensitive data across multiple parties before processing.
Ethical practice encourages adopting such emerging tools, especially in industries like healthcare, finance, telecom, and government where sensitive data is unavoidable.
As threats evolve, PPTs offer a future-proof approach to minimizing exposure.
10. Secure Disposal and End-of-Life Data Management
Data security does not end when information becomes obsolete; improper disposal can expose sensitive information even after it has lost operational value.
Ethical practices require secure deletion, cryptographic wiping, destruction of physical media, and verification logs to ensure no remnants remain recoverable.
Many cyberattacks exploit old archives or forgotten backup drives, emphasizing the importance of secure disposal processes.
End-of-life management also applies to devices—laptops, servers, USB drives, and cloud instances—that may store sensitive logs or cached data. Proper disposal prevents data resurrection by attackers.
11. Ethical Use of Automated Decision Systems
When sensitive data is used to train machine learning or AI systems, ethical handling must also ensure that automated decisions do not unintentionally expose, infer, or misuse private information.
AI models may memorize patterns from sensitive data, leading to indirect leakage through outputs.
Ethical practices include model monitoring, privacy-preserving ML techniques, red-teaming models for vulnerabilities, and restricting access to model internals.
Organizations must also ensure fairness and compliance, especially when sensitive data influences decisions such as credit scores, healthcare risk predictions, or fraud detection.
Real-World Stories (Failures & Successes)
1. Equifax Data Breach (2017) – Major Failure
One of the largest data breaches in history occurred when Equifax exposed sensitive financial and identity data of 147 million users.
The breach resulted from an unpatched system vulnerability and weak internal monitoring. Attackers accessed social security numbers, credit history, addresses, and birthdates.
Learning: Even basic failures in patch management can compromise vast amounts of sensitive data.
Continuous updates and automated vulnerability scanning are essential.
2. Capital One Cloud Misconfiguration Leak (2019) – Misconfiguration Failure
A misconfigured AWS bucket allowed an attacker to access sensitive financial data of over 100 million customers.
The breach occurred because a firewall rule was improperly set, giving unauthorized access to cloud data.
Learning: Technical protections like encryption mean little without proper configuration. Regular audits and automated security tools are necessary for cloud environments.
3. Singapore Health Services (SingHealth) Breach – Highly Sensitive Data Exposure
Attackers compromised 1.5 million medical records, including those of the Prime Minister. Investigation revealed that passwords were weak, internal monitoring was inadequate, and admin accounts lacked MFA.
Learning: Medical data is extremely sensitive; weak internal practices can expose critical information even in advanced healthcare systems.
4. Spotify Stolen Credentials Attack – A Third-Party Failure
Millions of Spotify accounts were compromised not because Spotify was breached, but because attackers used credentials leaked from unrelated services.
Learning: Third-party exposures can compromise sensitive data. Organizations must require MFA, login throttling, and anomaly detection to prevent credential stuffing.
5. Google Project Nightingale – A Mixed Outcome
Google partnered with a U.S. hospital chain to analyze patient data for improving healthcare AI.
Although data was legally shared, the public criticized the lack of transparency and unclear consent.
Learning: Even when data handling is secure, ethical failures in communication can damage trust.
6. Apple’s Secure Enclave – A Strong Success Case
Apple’s hardware-based Secure Enclave encrypts fingerprint and facial recognition data directly on the device.
Sensitive biometric data never leaves the hardware module or Apple’s servers.
Learning: Privacy-by-design at the hardware level creates the highest form of sensitive data protection.
Practical Challenges in Sensitive Data Handling
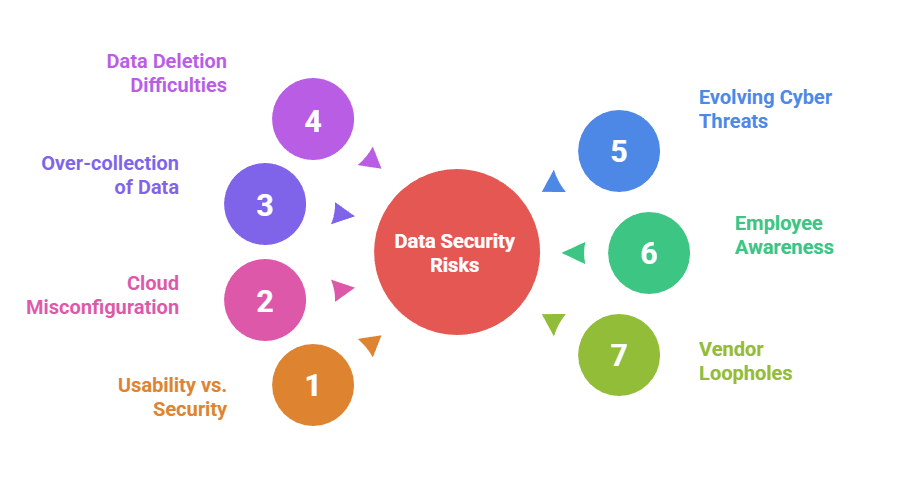 1. Balancing usability and security: Strong protections sometimes slow workflow; organizations struggle to keep systems both secure and efficient.
1. Balancing usability and security: Strong protections sometimes slow workflow; organizations struggle to keep systems both secure and efficient.
2. Misconfigured cloud infrastructure: One of the top causes of sensitive data leaks due to human error or lack of cloud expertise.
3. Over-collection of data: Businesses gather more than necessary, creating unnecessary risk and regulatory exposure.
4. Difficulty deleting data everywhere: Backups, logs, caches, vendor systems, and old servers often retain sensitive data unintentionally.
5. Evolving cyber threats: Attackers use AI-driven methods, making traditional security insufficient.
6. Lack of employee awareness: Staff often mishandle sensitive files, send data insecurely, or click phishing links.
7. Vendor loopholes: External partners might not maintain equivalent security levels.
