Securing Business Intelligence (BI) systems and controlling data access are critical for protecting sensitive business information, ensuring regulatory compliance, and maintaining user trust. BI platforms aggregate data from multiple sources to create centralized repositories of valuable insights, which, if not properly secured, can be vulnerable to unauthorized access, manipulation, and breaches.
Implementing comprehensive security measures—including access control, data encryption, auditing, and governance—helps organizations mitigate risks while enabling smooth, secure analytics workflows.
Core Principles of BI Security
A strong BI security framework safeguards sensitive information while supporting operational continuity. Below are the fundamental principles guiding confidentiality, integrity, and availability.
1. Confidentiality: Ensures data is accessible only by authorized users and systems. Essential to protect sensitive company and customer information.
2. Integrity: Protects data from unauthorized alterations, ensuring accuracy and trustworthiness throughout the BI lifecycle.
3. Availability: Maintains uninterrupted access to BI tools and data to support timely decision-making.
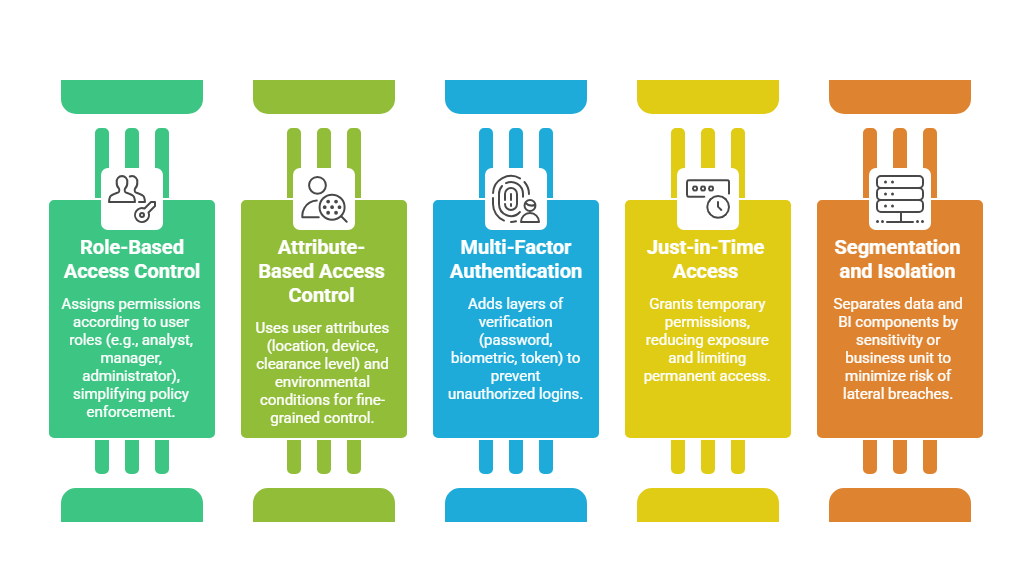
Access Control Mechanisms
Effective access control limits data visibility and functionality based on user roles and responsibilities.
Data Protection Techniques
To mitigate risks and comply with regulations, BI platforms must employ robust data protection strategies. The following methods outline best practices for securing data.
1. Encryption: Applies cryptographic protections for data at rest (stored data) and in transit (communications between BI components). Standards like TLS 1.3 and AES-256 are commonly used.
2. Data Masking and Tokenization: Conceals sensitive information by masking or replacing data elements to ensure privacy in reports and during data sharing.
3. Secure Development and Deployment: Incorporates security into the software development lifecycle with code analysis, penetration testing, and configuration management.
4. Cloud Security Practices: In cloud BI architectures, apply shared responsibility models, cloud access security brokers, and continuous monitoring for threats.
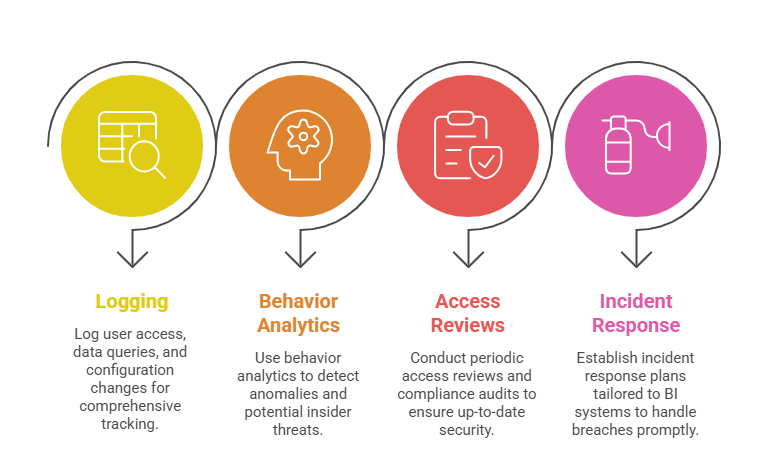
Auditing, Monitoring, and Compliance
Ensuring trustworthy and compliant BI operations relies on vigilant monitoring and structured audits. Here are the main techniques to maintain governance and security.
Best Practices for BI Security and Access Control
Maintaining secure and controlled access in BI systems is critical for compliance and operational trust. The following practices help enforce strong security measures.
1. Develop a layered security approach combining authentication, authorization, encryption, and monitoring.
2. Regularly train users and administrators on security awareness and policies.
3. Establish clear data governance policies delineating data ownership, stewardship, and accountability.
4. Use automated tools to manage user access lifecycle—from onboarding to de-provisioning.
5. Stay current with security patches, updates, and industry best practices for BI platforms.
